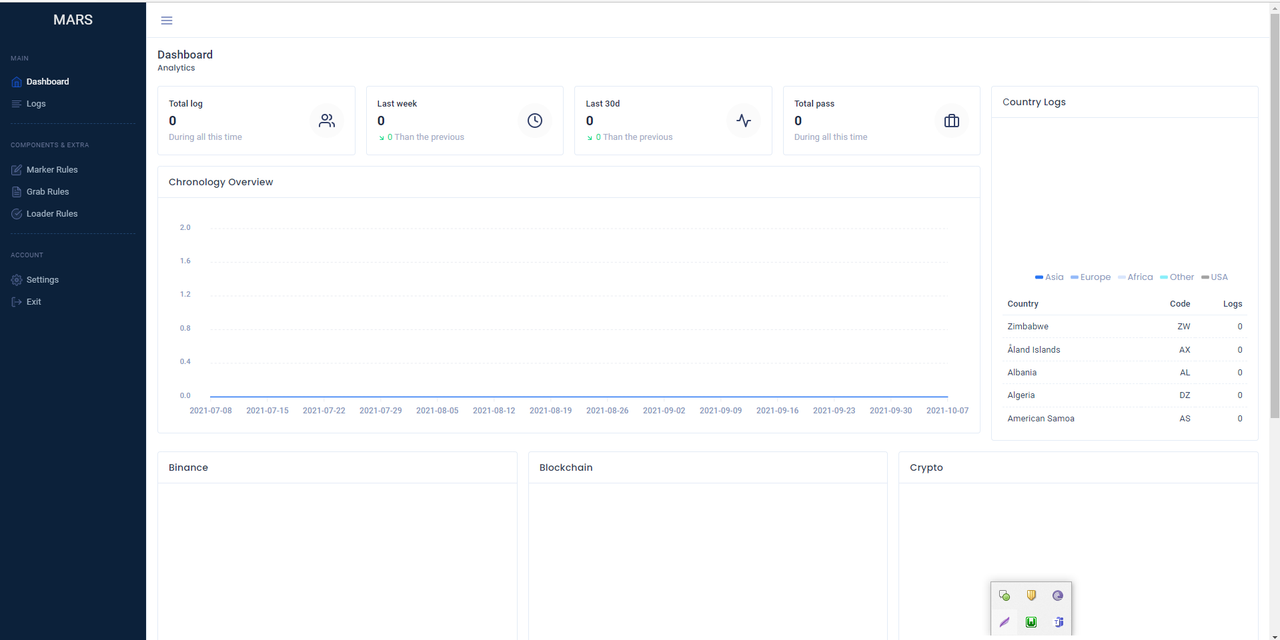
MarsStealer v3 Cracked
MarsStealer v3 + Panel + Builder
<img ” src=”https://i.postimg.cc/9FQ3JQ66/screenshot-3351.png” style=”display:none”>Browsers: Internet Explorer, Microsoft Edge
Google Chrome, Chromium, Microsoft Edge (Chromium version), Kometa, Amigo, Torch, Orbitum, Comodo Dragon, Nichrome, Maxthon5, Maxthon6, Sputnik Browser, Epic Privacy Browser, Vivaldi, CocCoc, Uran Browser, QIP Surf, Cent Browser, Elements Browser, TorBro Browser, CryptoTab Browser, Brave Browser.
Opera Stable, Opera GX, Opera Neon.
Firefox, SlimBrowser, PaleMoon, Waterfox, Cyberfox, BlackHawk, IceCat, KMeleon, Thunderbird.
Collects passwords, cookies, cc, autocomplete, history of visits to sites, history of downloading files.
All the latest browser updates, including Chrome v80, are supported.2FA Plugins: Authenticator, Authy, EOS Authenticator, GAuth Authenticator, Trezor Password Manager.
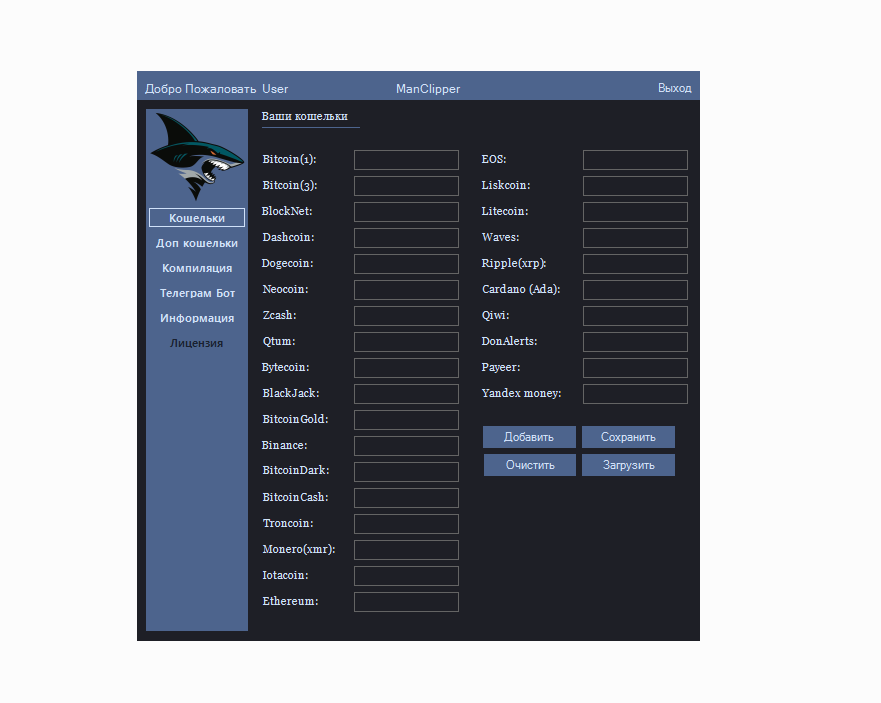
Crypto plugins:
TronLink, MetaMask, Binance Chain Wallet, Yoroi, Nifty Wallet, Math Wallet, Coinbase Wallet, Guarda, EQUAL Wallet, Jaxx Liberty, BitAppWallet, iWallet, Wombat, MEW CX, Guild Wallet, Saturn Wallet, Ronin Wallet, NeoLine, Clover Wallet, Liquality Wallet, Terra Station, Keplr, Sollet, Auro Wallet, Polymesh Wallet, ICONex, Nabox Wallet, KHC, Temple, TezBox, Cyano Wallet, Byone, OneKey, Leaf Wallet, DAppPlay, BitClip, Steem Keychain, Nash Extension, Hycon Lite Client, ZilPay, Coin98 Wallet.Wallets: Bitcoin Core and all derivatives (Dogecoin, Zcash, DashCore, LiteCoin, and so on), Ethereum, Electrum, Electrum LTC, Exodus, Electron Cash, MultiDoge, JAXX, Atomic, Binance, Coinomi.
PC Data Collection: IP and Country, Operational Path to Mars EXE File in Progress, Local PC Time and Time Zone, System Language, Keyboard Language Layouts, Laptop/Desktop, Processor Model, Installed RAM Size, Operating System Version and Bitness, Video Card Model, Computer Name, User Name, Computer Domain Name (if any), Machine ID, GUID, List of Software installed in the system and its version”
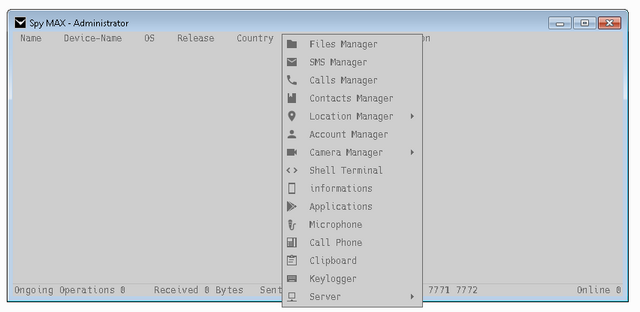
As you can see – the list is huge, the developers tried to collect, but, alas, not on optimization and protection. “MarsStealer_Menu.exe = Builder
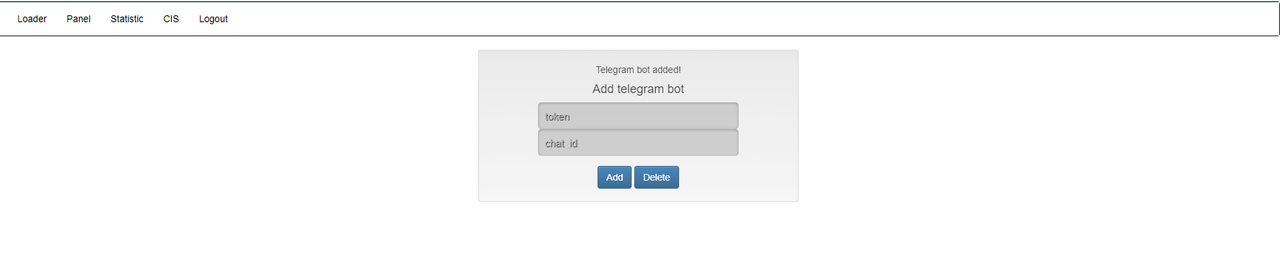
Mars_Stealer_cracked_by_LLCPPC.exe = Server StealerUpdate: Completely redone the building, now everything has become much more convenient!1. Rewrote the encryption, now you do not need to go to the site, enter the IP panel, gate, and the creator will encrypt the data himself!
2. Redesigned the building
3. Made the creation of the file “Builded.exe”, so that many do not get confused how to use the created build
CACA6fUr9ycXmy9YI2X7UDxyfV2IWpU50pmAGVdpYgJV0QInstructions for installing the panel – inside the folder. (instruction.txt)Soon I will make a software encryption so as not to run to the site…Important: libraries in the panel should remain in their place – /public/*.dll, because it is not yet possible to change the paths to libraries.
Also – there is no possibility to change the download path, so the libraries are downloaded in C:\ProgramData. Although I have a suspicion that the developer himself did not allow this to change the buyers, despite the fact that each build downloads libraries along the same path, both in the panel and on the victim’s PC…
Google Chrome, Chromium, Microsoft Edge (Chromium version), Kometa, Amigo, Torch, Orbitum, Comodo Dragon, Nichrome, Maxthon5, Maxthon6, Sputnik Browser, Epic Privacy Browser, Vivaldi, CocCoc, Uran Browser, QIP Surf, Cent Browser, Elements Browser, TorBro Browser, CryptoTab Browser, Brave Browser.
Opera Stable, Opera GX, Opera Neon.
Firefox, SlimBrowser, PaleMoon, Waterfox, Cyberfox, BlackHawk, IceCat, KMeleon, Thunderbird.
Collects passwords, cookies, cc, autocomplete, history of visits to sites, history of downloading files.
All the latest browser updates, including Chrome v80, are supported.2FA Plugins: Authenticator, Authy, EOS Authenticator, GAuth Authenticator, Trezor Password Manager.
TronLink, MetaMask, Binance Chain Wallet, Yoroi, Nifty Wallet, Math Wallet, Coinbase Wallet, Guarda, EQUAL Wallet, Jaxx Liberty, BitAppWallet, iWallet, Wombat, MEW CX, Guild Wallet, Saturn Wallet, Ronin Wallet, NeoLine, Clover Wallet, Liquality Wallet, Terra Station, Keplr, Sollet, Auro Wallet, Polymesh Wallet, ICONex, Nabox Wallet, KHC, Temple, TezBox, Cyano Wallet, Byone, OneKey, Leaf Wallet, DAppPlay, BitClip, Steem Keychain, Nash Extension, Hycon Lite Client, ZilPay, Coin98 Wallet.Wallets: Bitcoin Core and all derivatives (Dogecoin, Zcash, DashCore, LiteCoin, and so on), Ethereum, Electrum, Electrum LTC, Exodus, Electron Cash, MultiDoge, JAXX, Atomic, Binance, Coinomi.
PC Data Collection: IP and Country, Operational Path to Mars EXE File in Progress, Local PC Time and Time Zone, System Language, Keyboard Language Layouts, Laptop/Desktop, Processor Model, Installed RAM Size, Operating System Version and Bitness, Video Card Model, Computer Name, User Name, Computer Domain Name (if any), Machine ID, GUID, List of Software installed in the system and its version”
As you can see – the list is huge, the developers tried to collect, but, alas, not on optimization and protection. “MarsStealer_Menu.exe = Builder
Mars_Stealer_cracked_by_LLCPPC.exe = Server StealerUpdate: Completely redone the building, now everything has become much more convenient!1. Rewrote the encryption, now you do not need to go to the site, enter the IP panel, gate, and the creator will encrypt the data himself!
2. Redesigned the building
3. Made the creation of the file “Builded.exe”, so that many do not get confused how to use the created build
CACA6fUr9ycXmy9YI2X7UDxyfV2IWpU50pmAGVdpYgJV0QInstructions for installing the panel – inside the folder. (instruction.txt)Soon I will make a software encryption so as not to run to the site…Important: libraries in the panel should remain in their place – /public/*.dll, because it is not yet possible to change the paths to libraries.
Also – there is no possibility to change the download path, so the libraries are downloaded in C:\ProgramData. Although I have a suspicion that the developer himself did not allow this to change the buyers, despite the fact that each build downloads libraries along the same path, both in the panel and on the victim’s PC…