Oski Stealer Cracked
Oski Stealer Cracked
Secondly, the payload will self destruct after loading, making it hard to trace the malware. Given the strong stealing features alongside being silent makes this extremely severe. In other words, alongside an exploit this stealer can be spread completely undetected. Allowing you to grow logs of data on a new level for any of your needs. However, with this stealer being completely native, working on all systems, it is arguably the best. In conclusion we highly suggest using Oski Stealer alongside any of our exploits to expand any of your data logging needs!
Features:
– Advanced Stealer
– Browser Cookies / Passwords:
– Chromium Based: Chromium, Google Chrome, Kometa, Amigo, Torch, Orbitum, Opera, Comodo Dragon, Nichrome, Yandex Browser, Maxthon5, Sputnik, Epic Privacy Browser, Vivaldi, CocCoc and other browsers that use the working directory Chromium.
– Firefox Based: Mozilla Firefox, Pale Moon, Waterfox, Cyberfox, BlackHawk, IceCat, K-Meleon and other browsers that use the working directory Firefox.
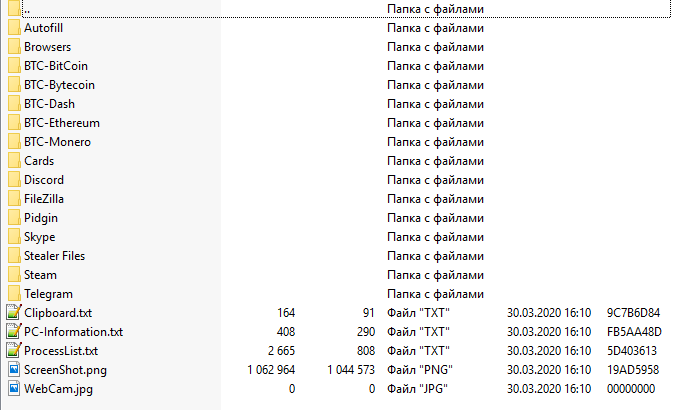
Filezilla Stealer
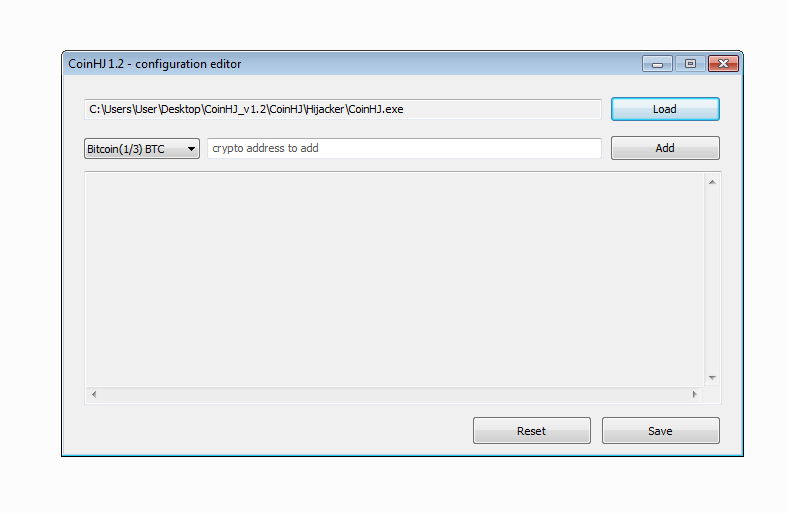
– Crypto-Wallet Stealer
– Bitcoin Core, Ethereum, ElectrumLTC, Monero, Electrum, Exodus, Dash, Litecoin, ElectronCash, ZCash, MultiDoge, AnonCoin, BBQCoin, DevCoin, DigitalCoin, FlorinCoin, Franko, FreiCoin, GoldCoin, InfiniteCoin, IOCoin, IxCoin, MegaCoin, MinCoin, NameCoin, PrimeCoin, TerraCoin, YACoinFiles from machine data about machine.
Installed Softwares
Native Stub requiring no dependencies other than Windows installation
Multi-profile (up to 10)
Low stub size of 93kb
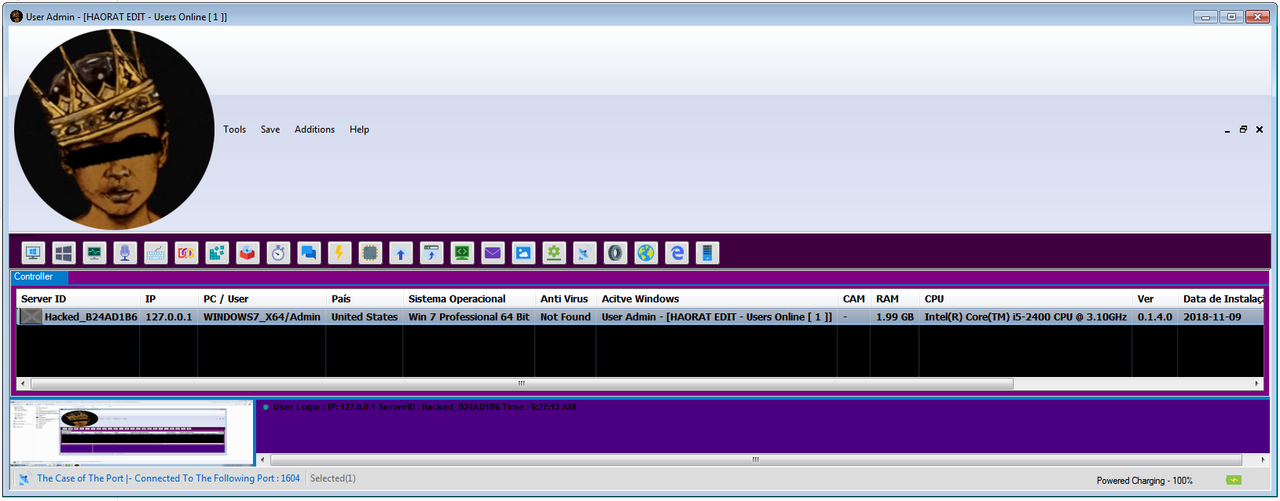
Supports Windows 7/8 / 8.1 / 10 | x32 / x64
Does not require administrative privilege
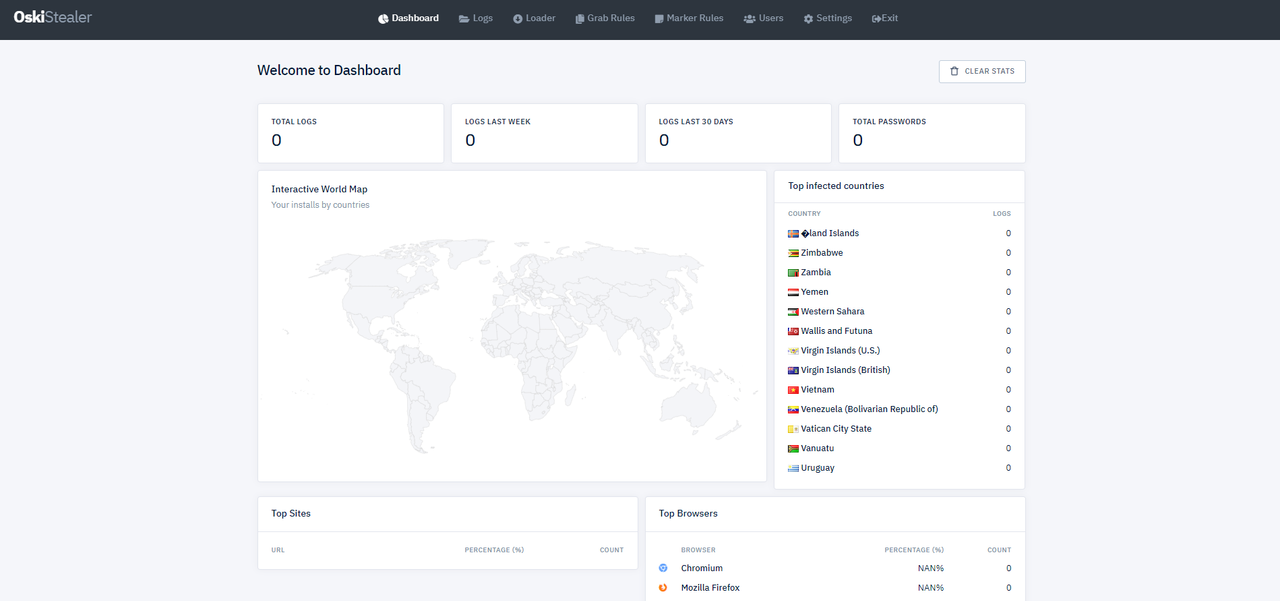
User-friendly Admin Panel
ICQ:653580170
Whatsapp +79017473945
jabber: russianhackerclub@jabber.ru


![IPKiller v2.3 ADVANCED DDOS [8 DDoS Floods] Cracked](http://image.prntscr.com/image/31de3efc2ce14ba8b6c98a8d00b3c7fd.png)