Liberium RAT 2.1 is a highly modular Remote Access Trojan (RAT) designed for cybercriminal ecosystems. It integrates surveillance, system control, financial theft, and distributed attack capabilities into one unified malware platform.
🧩 Main Idea of Liberium RAT 2.1
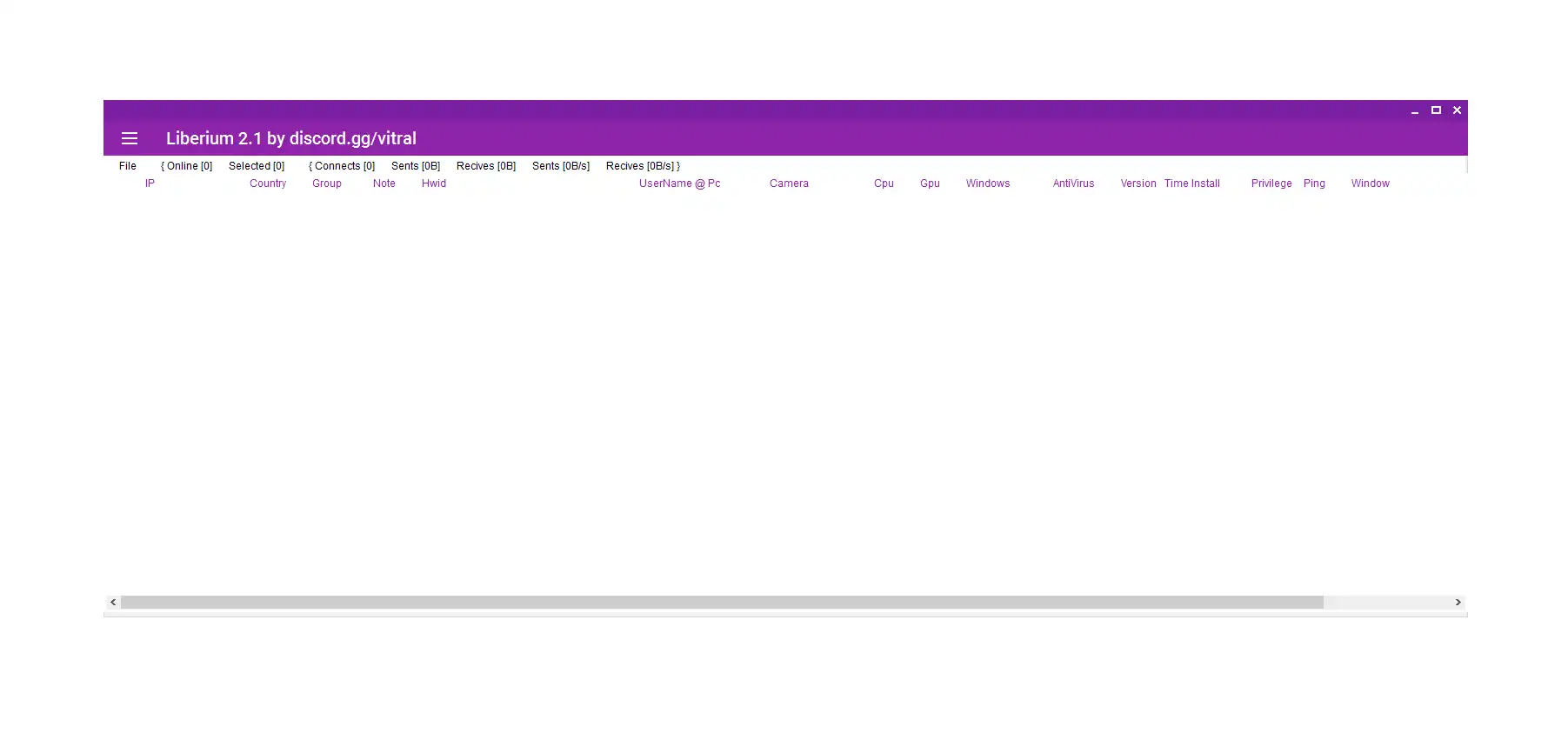
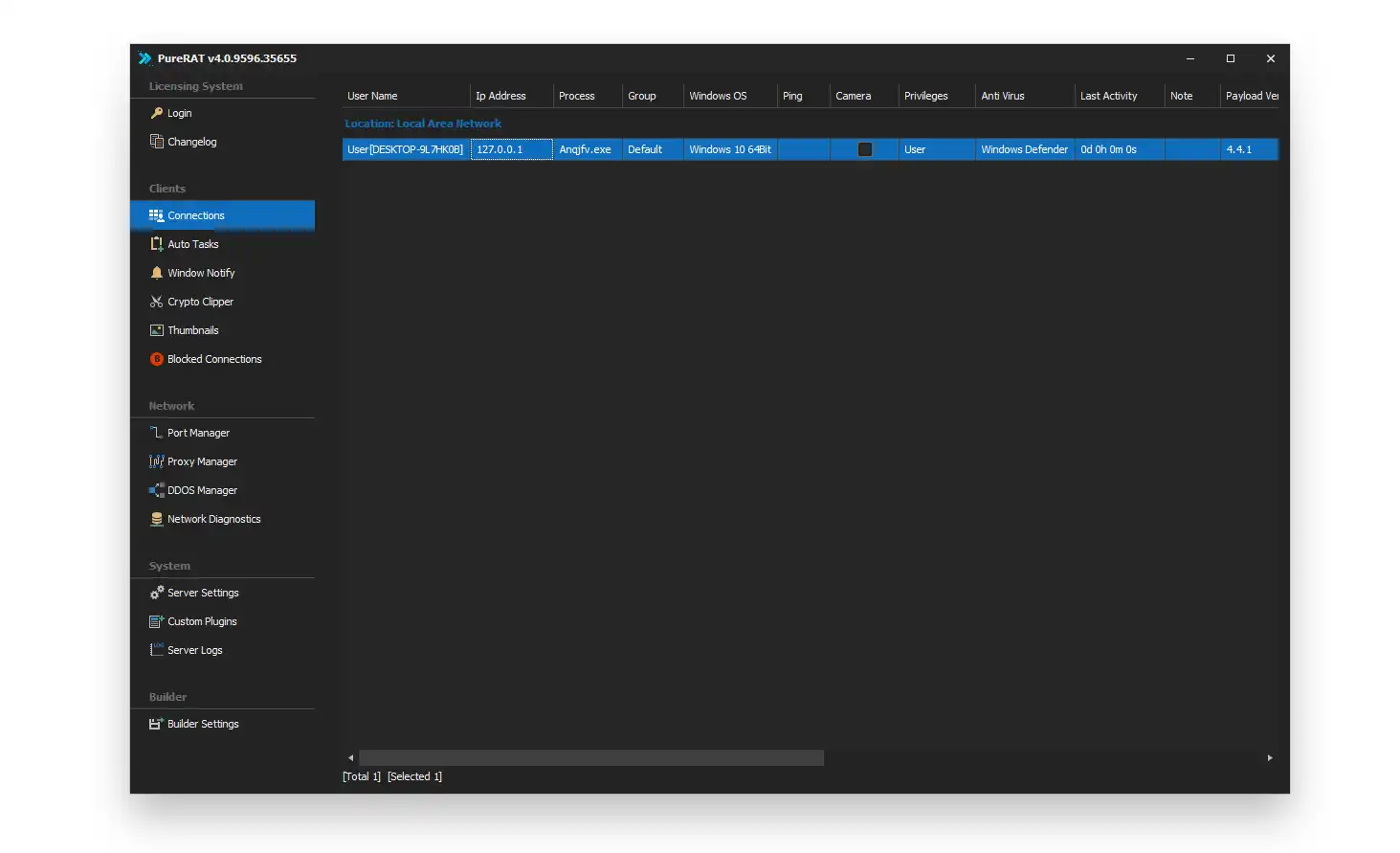
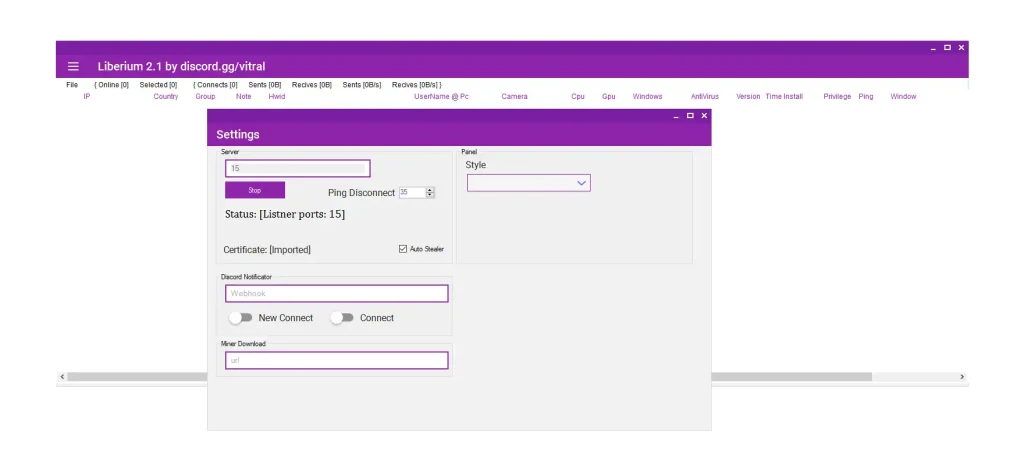
🧠 Core Dashboard & Botnet Management
- 🟢 Live Bot Monitoring System:
Tracks all infected devices in real time, showing active bots, connectivity, and system status.➤ This dashboard acts as the central command hub of the entire botnet infrastructure. It allows attackers to prioritize high-performance machines for tasks like mining or DDoS attacks. It also helps monitor infection stability and ensures continuous bot availability across global regions. - 🌍 Victim Profiling Engine:
Collects detailed hardware and software fingerprints including CPU, GPU, OS version, and installed security tools.➤ This feature enables intelligent victim categorization. Attackers can filter machines based on computational strength or geographic location. It also helps adapt malware behavior depending on detected antivirus solutions, increasing stealth and survivability.
🎮 control Liberium RAT 2.1
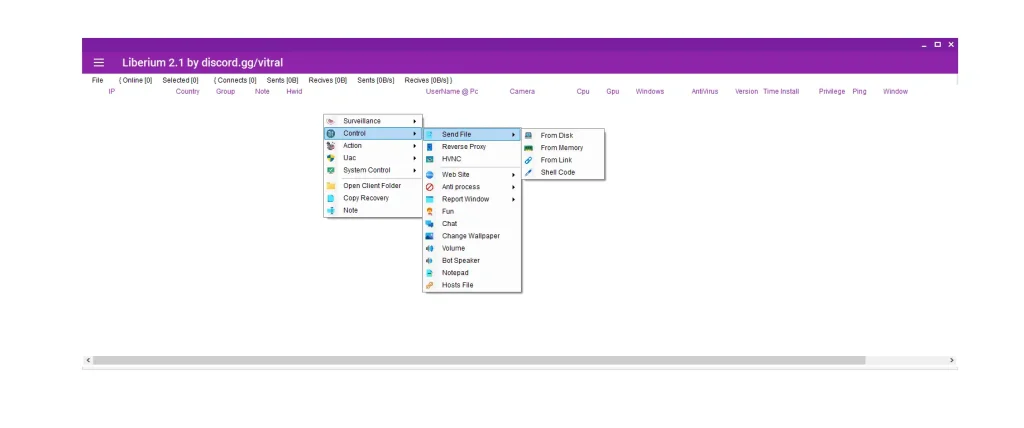
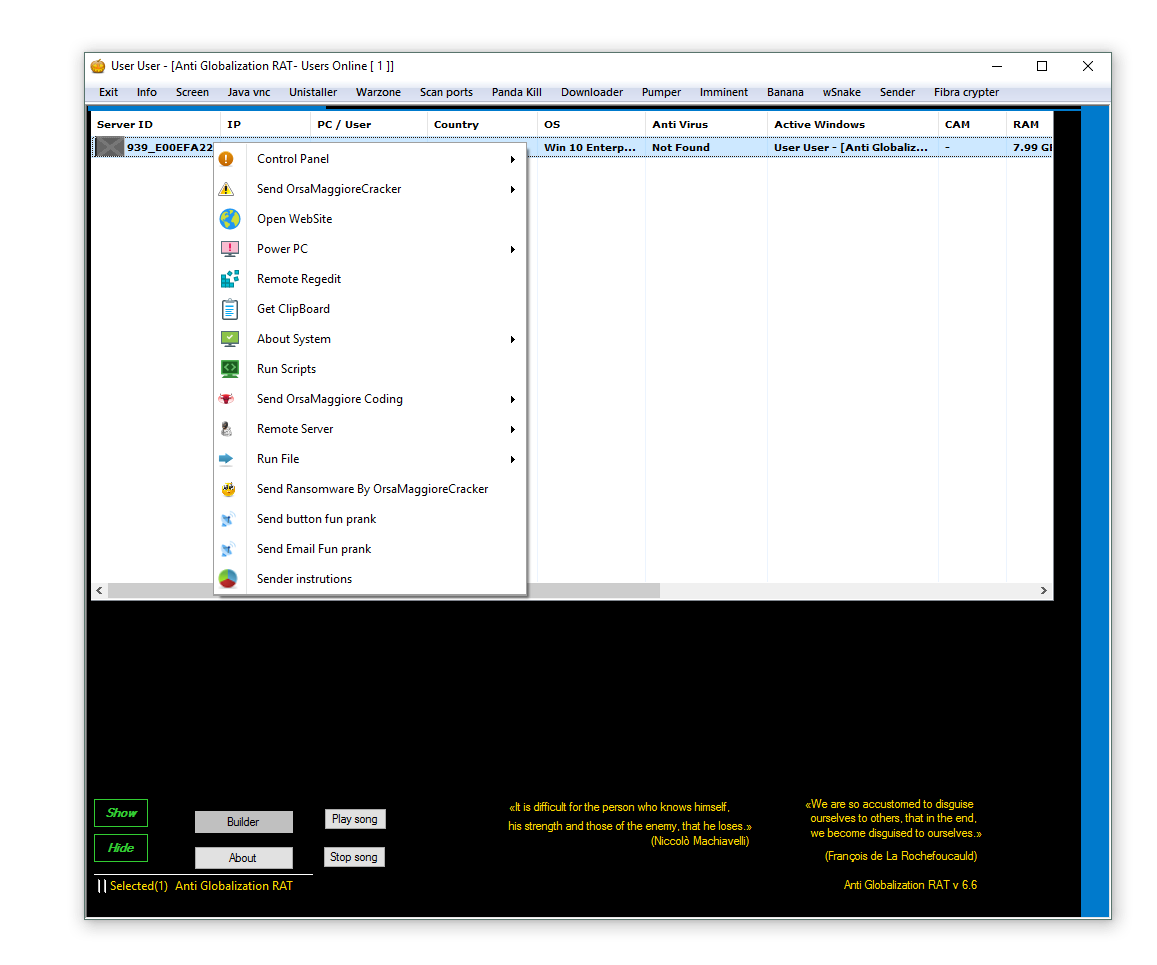
🖥️ Remote Control & Payload Execution
- 📁 Remote Execution System:
Executes files, scripts, or shellcode directly on compromised systems.➤ This allows attackers to deploy secondary malware, update payloads, or execute commands without user awareness. It effectively transforms infected systems into fully programmable remote execution nodes. - 🌐 Reverse Proxy & Browser Manipulation:
Routes traffic through infected systems and forces browser actions.➤ This provides anonymity for attackers while turning victims into proxy nodes. It is commonly used to mask malicious traffic origins and conduct phishing or credential-harvesting operations.
🕵️ surveillance Liberium RAT 2.1
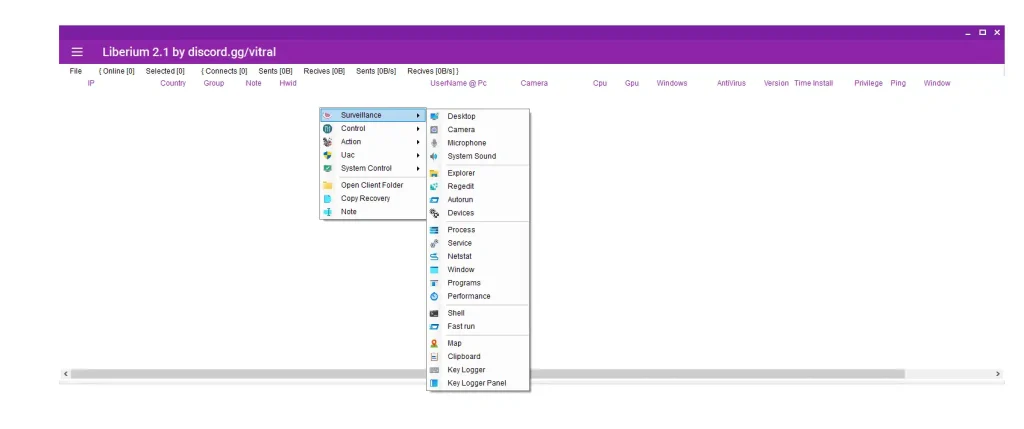
🧿 Espionage & Data Theft
- 📸 Screen & Webcam Monitoring:
Captures screenshots and webcam feeds in real time.➤ This provides attackers with visual access to sensitive environments such as offices, financial dashboards, or private communications. It is especially dangerous in corporate and enterprise systems. - ⌨️ Keylogging & Clipboard Tracking:
Records keystrokes and copied data including passwords and wallet addresses.➤ This is a primary credential theft mechanism. It silently captures login details, banking credentials, and authentication tokens without any visible indication to the user.
💣 ddos via Liberium RAT 2.1
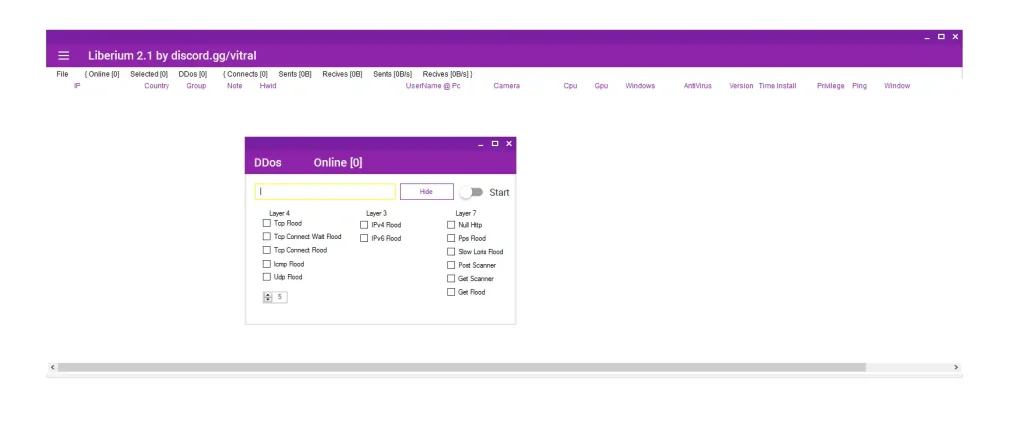
🌐 Network Attack Module
- ⚡ Layer 7 HTTP Flood Engine:
Overloads web applications using massive request traffic.➤ This targets web servers and APIs, exhausting CPU and memory resources. It can bring down poorly protected websites by simulating legitimate traffic at scale. - 🔌 Network Scanning System:
Detects open ports and vulnerable services on external systems.➤ This helps attackers map potential targets before launching attacks. It is used for reconnaissance in preparation for exploitation or intrusion attempts.
🪙 xmr miner & etc miner feature Liberium RAT 2.1
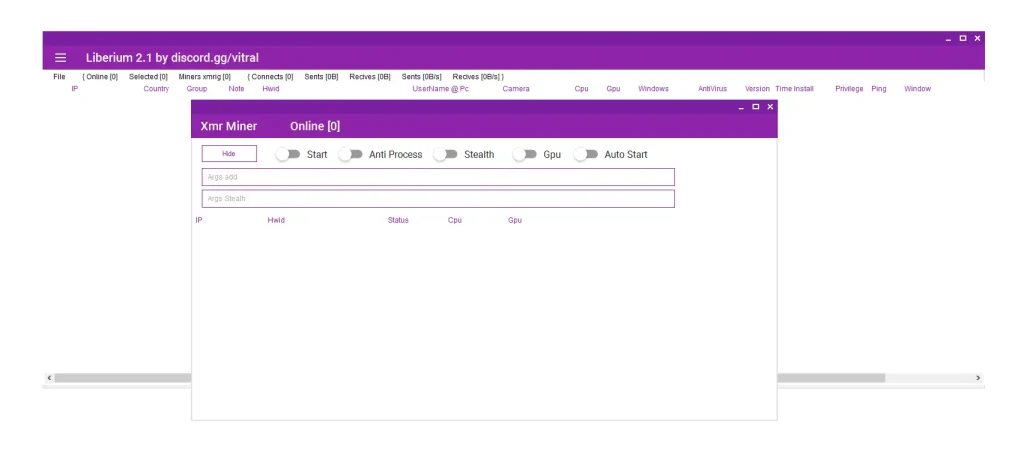
⛏️ Cryptocurrency Mining Modules (Cryptojacking)
- 🧠 CPU & GPU Mining Engine:
Uses victim hardware to mine cryptocurrencies such as Monero.➤ This covertly consumes system resources, leading to performance degradation and increased power usage. It generates continuous revenue for attackers without direct theft detection. - 🛡️ Stealth Persistence Mechanism:
Hides mining activity and restarts automatically after termination.➤ This ensures long-term operation by resisting manual removal and antivirus detection. It manipulates system processes to maintain invisible background execution.
📋 clipper Liberium RAT 2.1
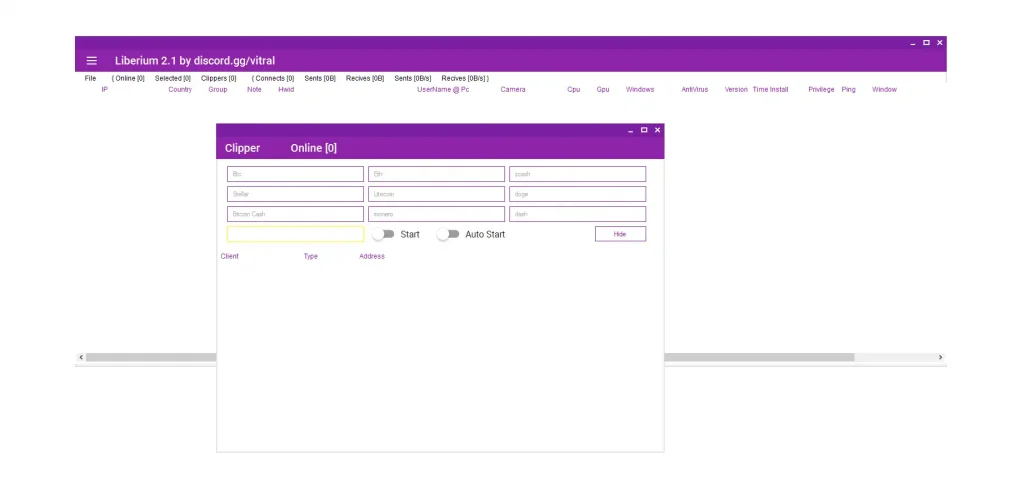
💰 Cryptocurrency Address Swapper
- 🔁 Clipboard Hijacking System:
Replaces copied wallet addresses with attacker-controlled addresses.➤ This enables silent financial theft during cryptocurrency transactions. Victims unknowingly send funds to attackers when pasting altered wallet addresses. - 🧾 Multi-Currency Support Engine:
Targets multiple cryptocurrencies including Bitcoin, Ethereum, and Litecoin.➤ This increases attack success rates across global crypto ecosystems by supporting widely used blockchain networks.
🔀 reverse proxy random mode & reverse proxy users mode
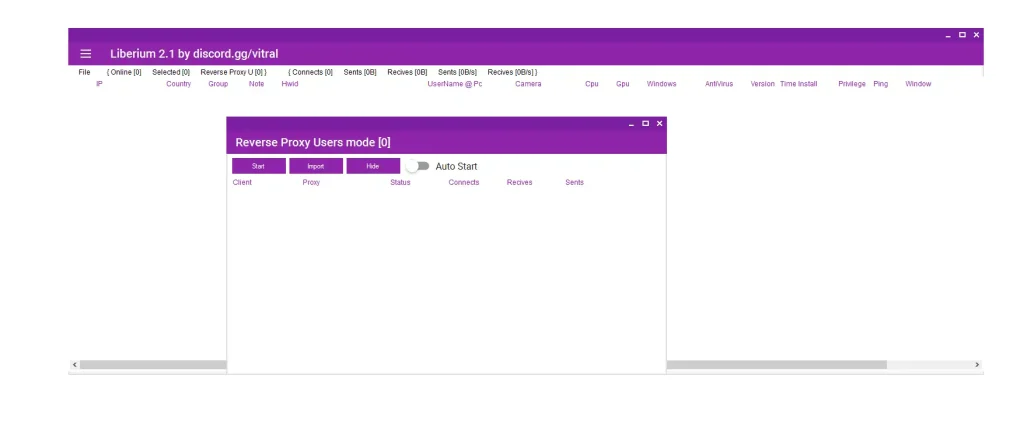
🕶️ Anonymization & Relaying
- 🔄 Traffic Relay System:
Routes attacker traffic through infected machines to hide origin.➤ This makes forensic tracking significantly more difficult. Victims unknowingly become part of a proxy chain used in cybercriminal infrastructure. - 🧩 Manual Proxy Selection Mode:
Allows attackers to choose specific infected systems as relay nodes.➤ This enables structured anonymity networks for advanced cyber operations like fraud, credential stuffing, or intrusion masking.
🔐 uac
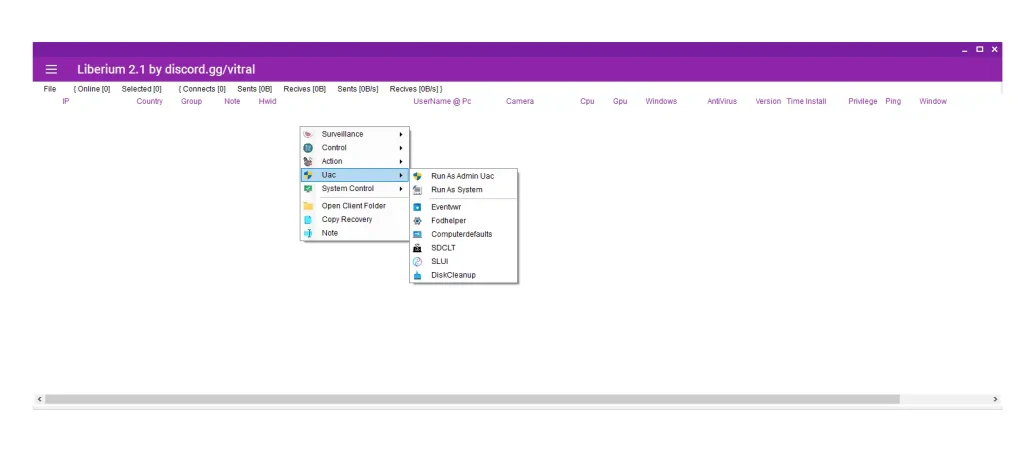
⚙️ Privilege Escalation Techniques
- 🧨 Windows UAC Bypass Exploitation:
Abuses legitimate system utilities such as Fodhelper and SLUI.➤ This allows malware to gain administrative privileges without triggering user consent prompts. It bypasses Windows security barriers to achieve deeper system access. - 🧠 SYSTEM-Level Execution:
Runs processes with highest privilege level on Windows systems.➤ This provides unrestricted access to system files, registry entries, and security configurations, making detection and removal extremely difficult.
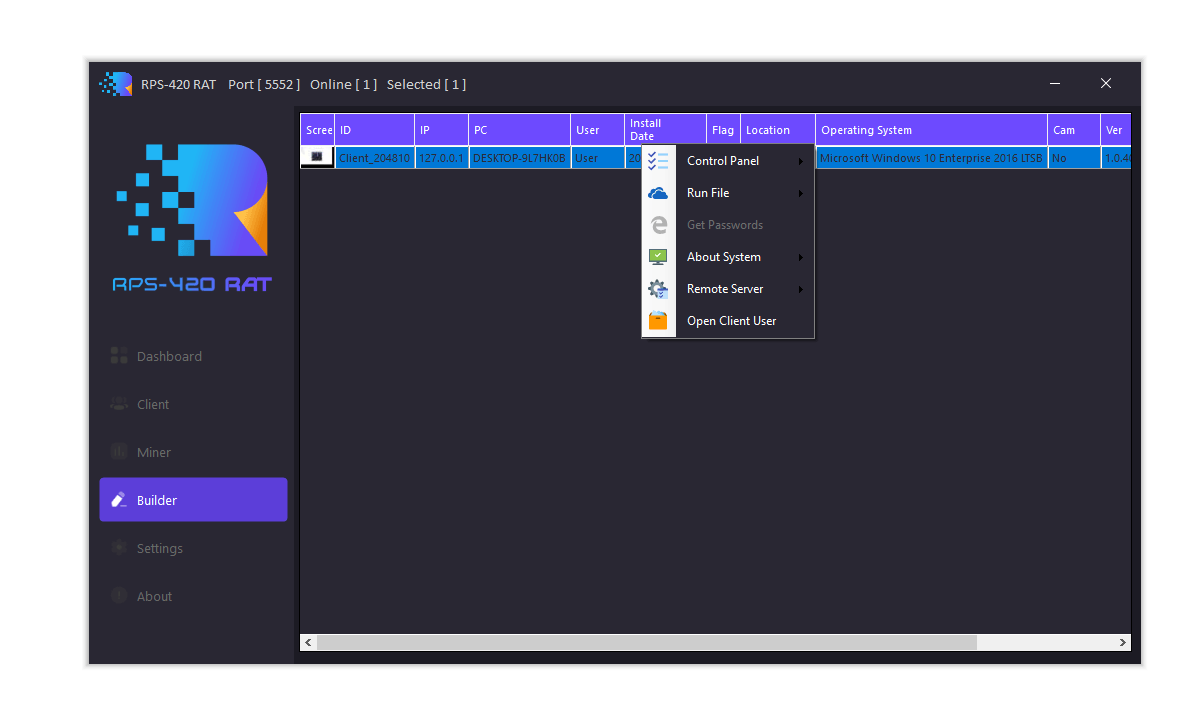
🏗️ builder options & builder
🧪 Configurable Malware Builder
- 🧩 Custom Payload Generator:
Creates tailored malware builds based on attacker configuration.➤ This modular system allows targeted attacks against specific victims or environments. Each build can behave differently depending on selected features. - 🔔 Command & Control Integration System:
Connects malware to remote servers and sends real-time infection alerts.➤ This provides attackers with instant updates when new victims are compromised, enabling real-time botnet management and scaling.
🧯 system control
🧨 Final Manipulation & Destruction
- 🔄 System Restart & Session Control:
Allows remote rebooting or session termination of infected machines.➤ This can be used for disruption, hiding activity, or resetting system states during malicious operations. It also assists in avoiding forensic detection. - 🗂️ Victim Organization System:
Allows labeling and categorizing infected systems.➤ This helps attackers manage large botnets efficiently by grouping victims based on value, geography, or system power.
Download Liberium RAT 2.1
Virus Total Report for Liberium RAT 2.1
https://www.virustotal.com/gui/file/9d12b9fb18f031c13648d2aff2bf8c7df9ed654e0c6eb8f62bc52987a9b8c571🧾 Conclusion: A Complete Cybercrime Infrastructure
Liberium RAT 2.1 is not a traditional malware tool—it is a fully integrated cybercrime platform combining surveillance, financial theft, botnet orchestration, cryptomining, and distributed attacks.
Its architecture reflects the evolution of modern malware toward automation, scalability, and stealth monetization systems.
❓ FAQs
1. What is Liberium RAT 2.1?
It is a remote access trojan designed for surveillance, botnet control, crypto theft, and cyberattacks.
2. Is Liberium RAT dangerous?
Yes, it enables full system compromise including data theft and remote control.
3. How does it steal cryptocurrency?
Through clipboard hijacking that replaces wallet addresses during transactions.
4. Can it bypass antivirus software?
Advanced versions use stealth techniques and system exploitation to evade detection.
5. What is the main purpose of RAT malware?
To gain unauthorized remote control over systems for spying, theft, or attack operations.