🔍 Introduction
In today’s evolving cyber threat landscape, advanced remote access tools are becoming increasingly sophisticated. One such tool gaining attention is Collapse HVNC RAT 2026, often distributed in cracked form.
This software is widely discussed in cybersecurity communities due to its stealth capabilities and powerful system control features. While it is commonly linked with malicious usage, analyzing its structure and behavior is crucial for ethical hackers, cybersecurity researchers, and system administrators.
This article provides a deep, structured, and SEO-optimized analysis of its features, risks, and defensive insights.
🧠 What is Collapse Collapse HVNC RAT 2026?
Collapse HVNC RAT 2026 is a Remote Administration Tool (RAT) that enables remote control over a target system using Hidden Virtual Network Computing (HVNC) technology.
🔑 Key Concept: HVNC
HVNC allows attackers to create a completely hidden desktop session, meaning:
- 👁️ The victim cannot see any activity happening in the background
- 🖱️ No mouse or keyboard movement is visible
- 🖥️ Hidden browsers and applications can run silently
👉 This makes it significantly more dangerous than traditional remote access tools.
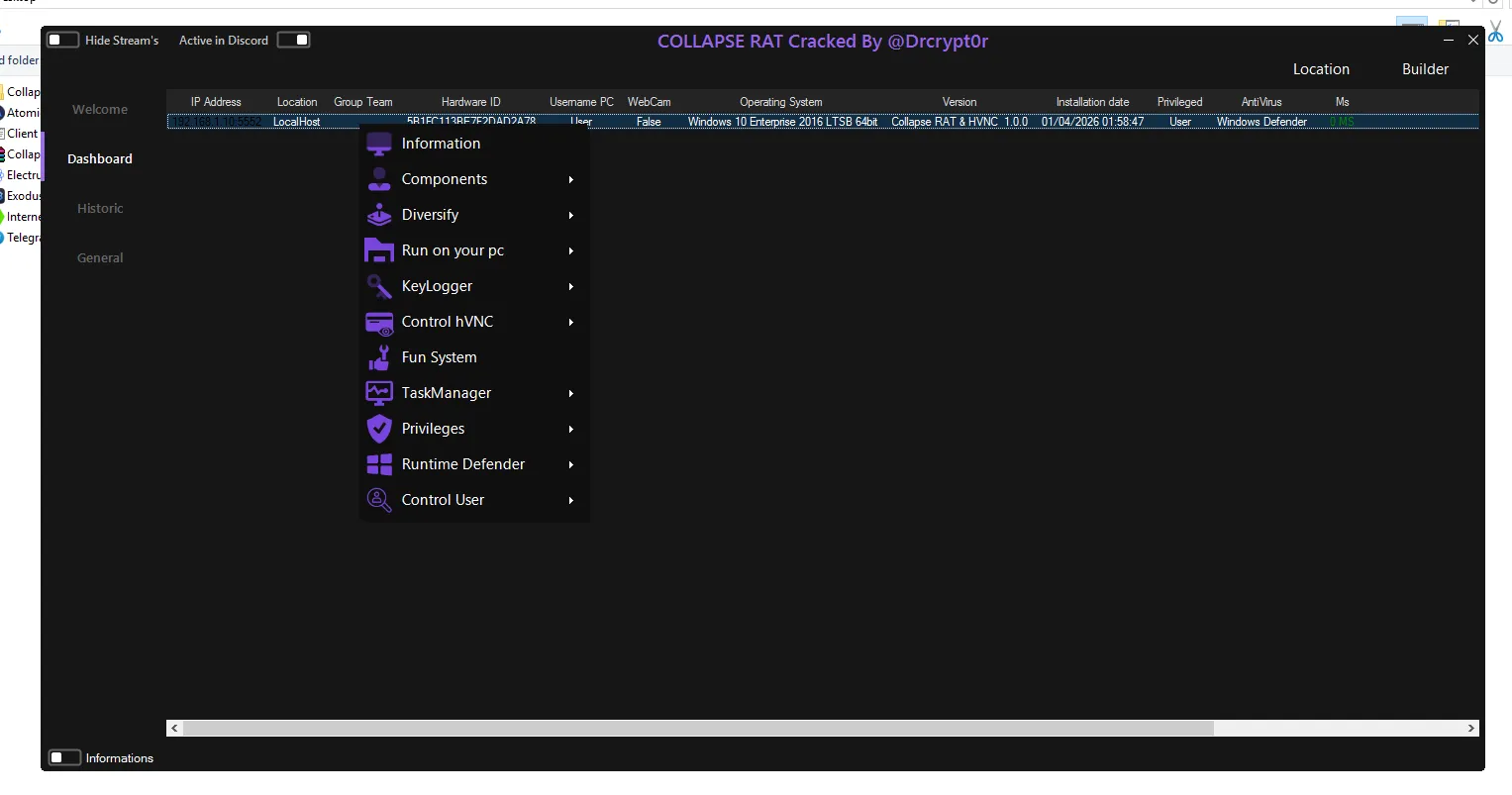
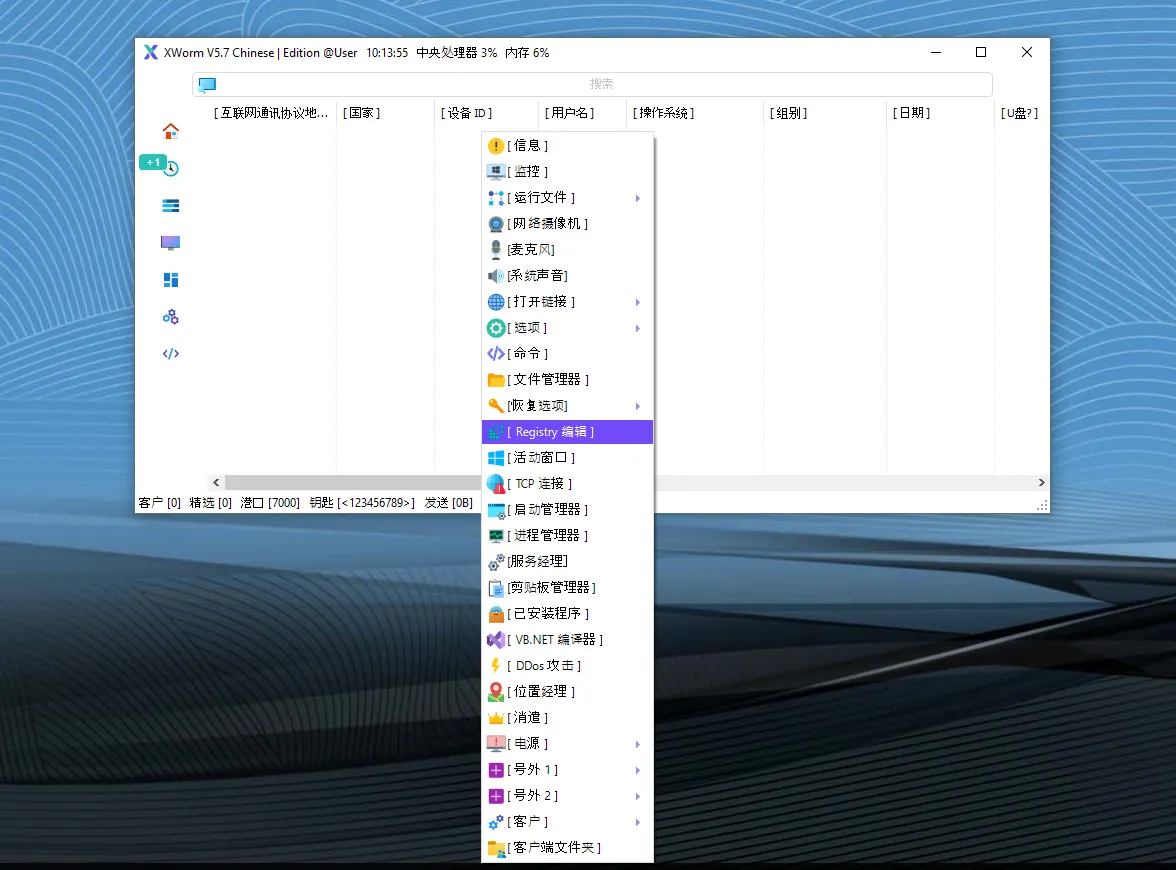
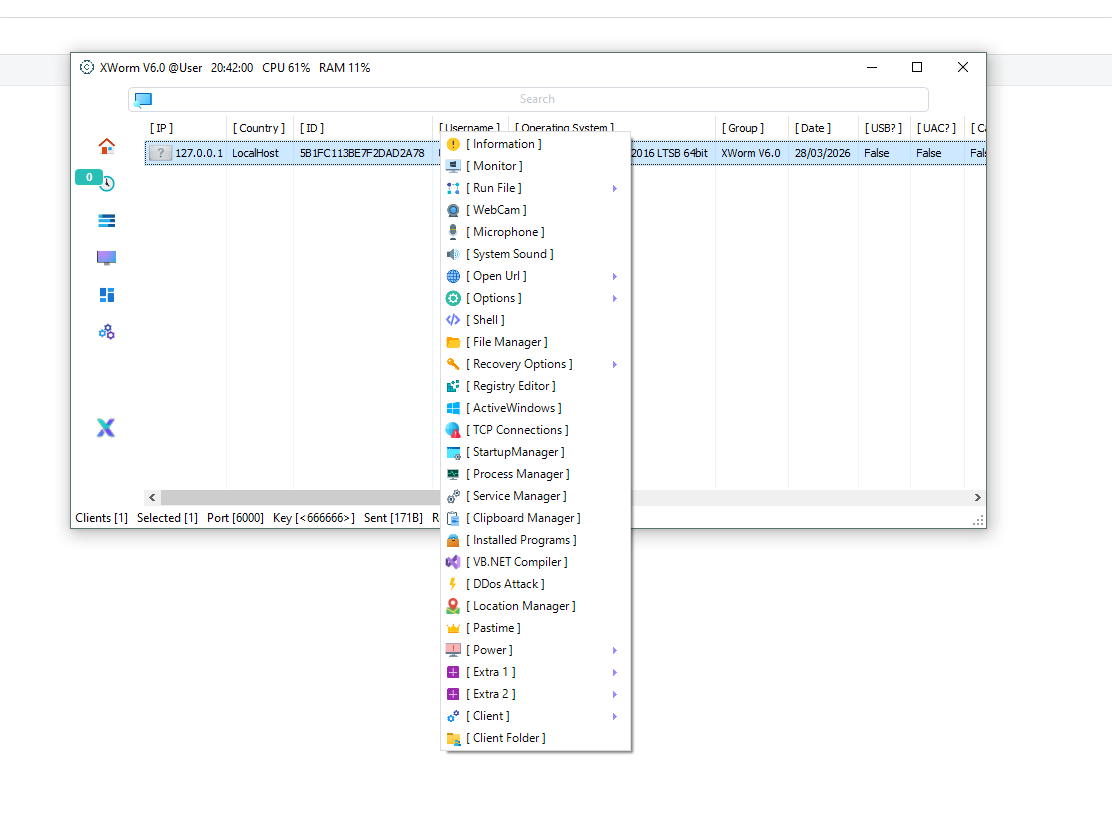
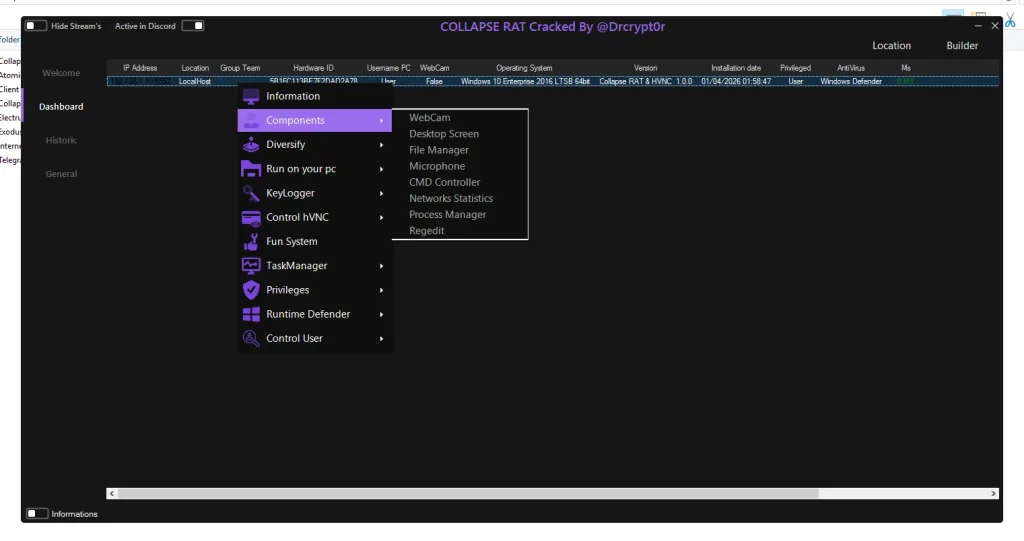
⚙️ Core Features of Collapse HVNC RAT 2026
Below is a detailed breakdown of its major functionalities:
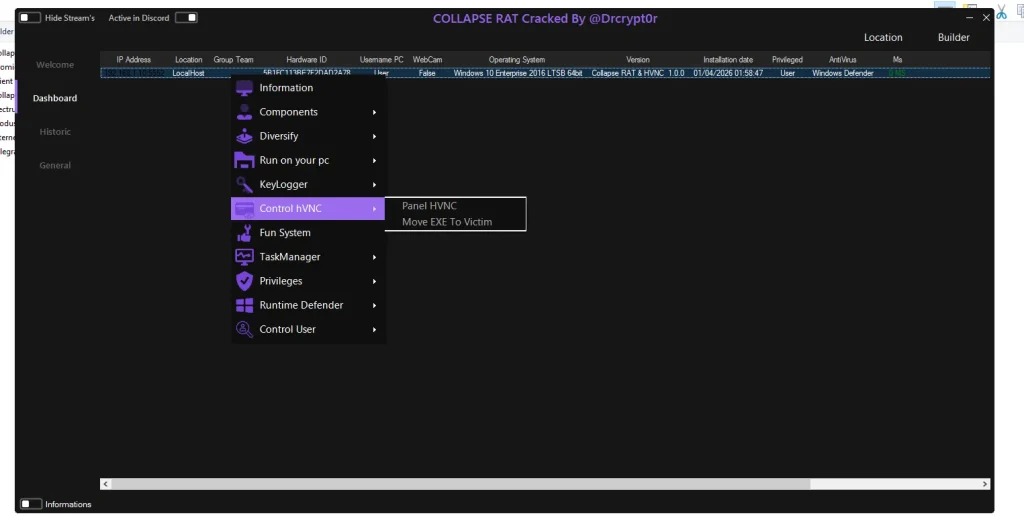
🖥️ System Information & Target Profiling
- 🌐 IP Address & Location Tracking
The software collects the victim’s IP address and estimates geographic location. This helps attackers understand where the target is based and can influence further actions such as targeted attacks or fraud. - 🧬 Hardware ID (HWID) Identification
A unique fingerprint is generated for each infected machine. This ensures that the attacker can track specific devices and avoid duplication in their control panel. - 💻 Operating System & User Details
Information like OS version, username, and privilege level (admin or standard user) is collected.
👉 This helps attackers decide what level of control they can achieve. - 🛡️ Security Software Detection
The tool scans for antivirus programs or security defenses.
👉 This allows attackers to adapt their strategy and bypass protection mechanisms.
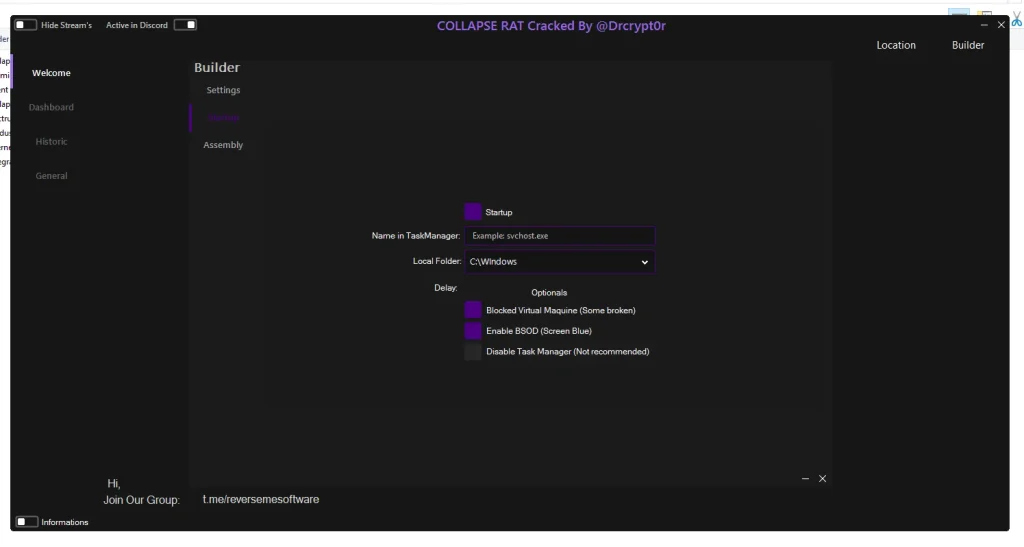
🕵️ Stealth & Persistence Mechanisms
- 👻 Hidden Desktop (HVNC Mode)
Attackers can open invisible browser sessions to perform activities such as logging into accounts or accessing sensitive platforms without the user noticing. - 🔒 Process Protection (Runtime Defense)
The malware protects itself from being terminated by system tools or antivirus software, ensuring it remains active for longer periods. - 🔁 Startup Persistence
The malware automatically runs when the system boots.
👉 This ensures continuous access even after system restarts. - 🧾 Fake System File Naming
It mimics legitimate system processes (like system services), making detection more difficult.
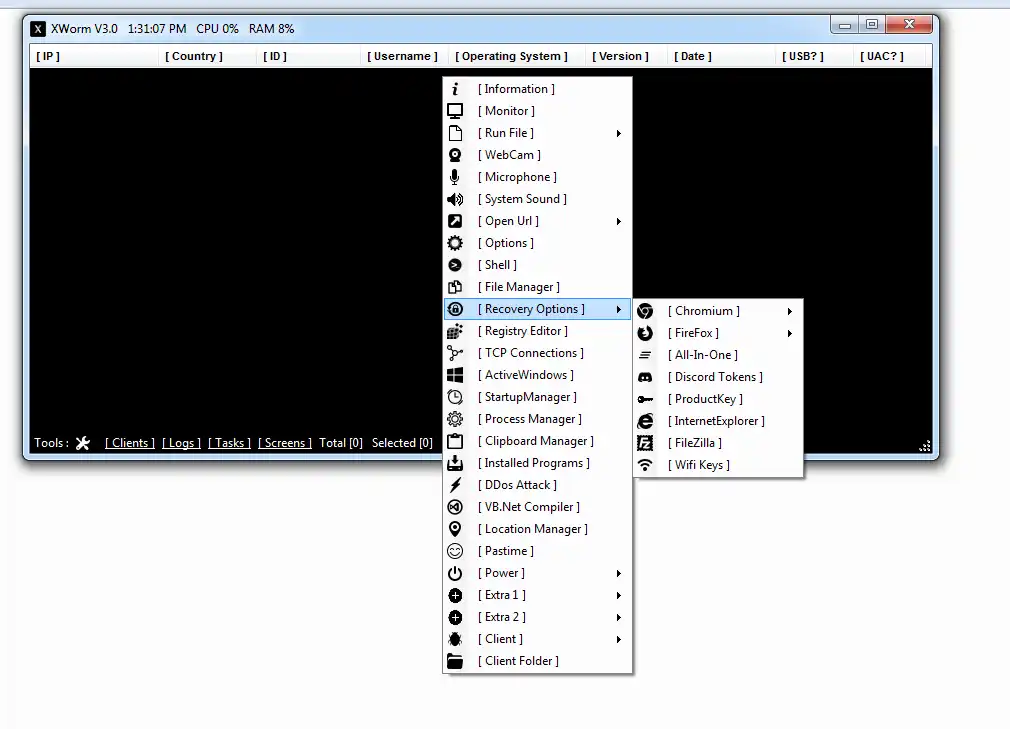
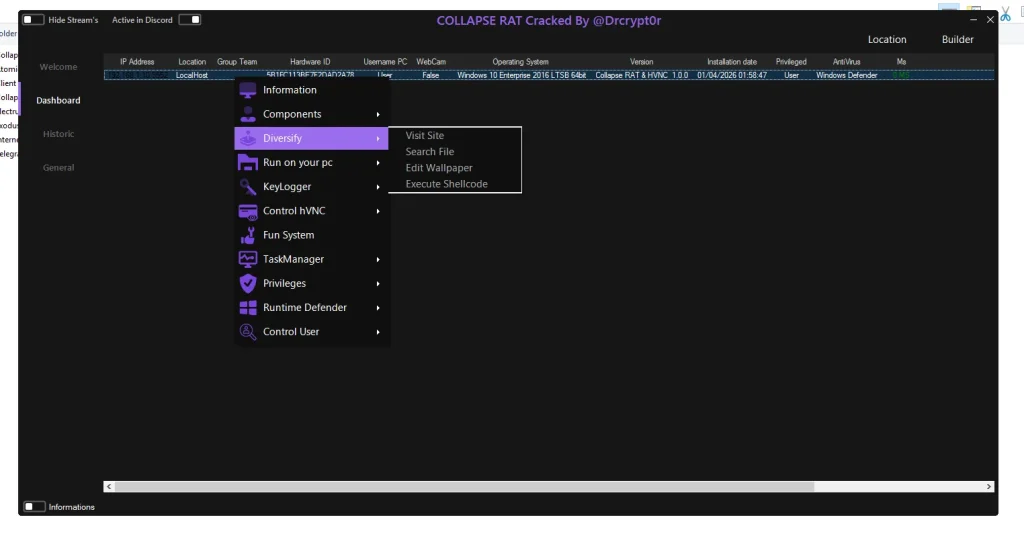
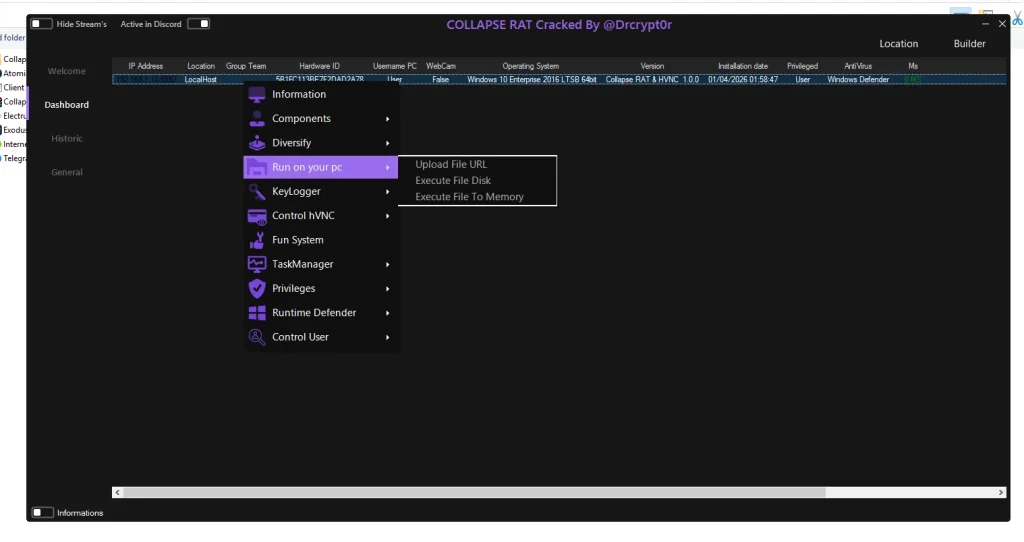
🛠️ Remote Command & Control Capabilities
- 📁 File Management System
Attackers can upload, download, delete, or execute files remotely.
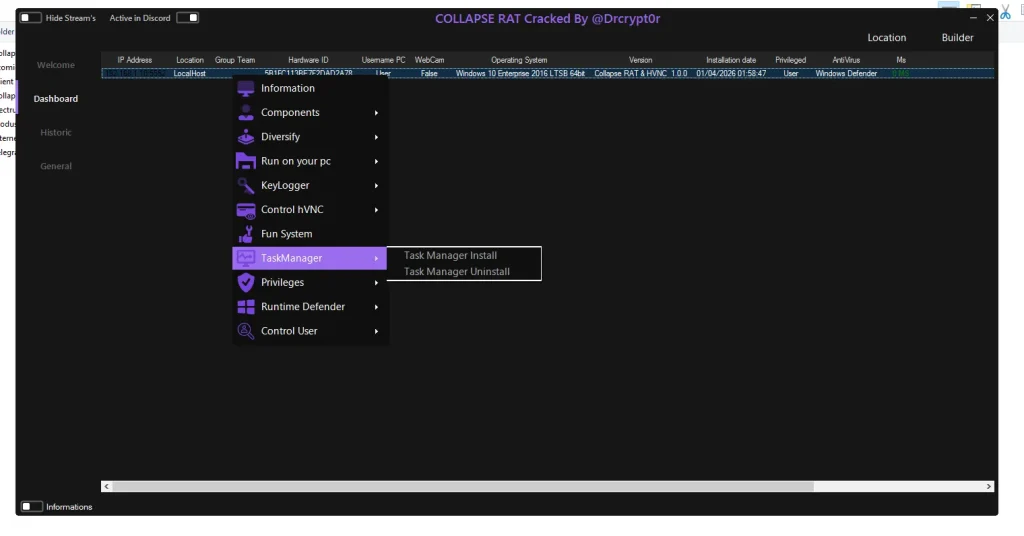
👉 This enables data theft and malware deployment. - ⚡ Task Manager Control
Running processes can be viewed and terminated.
👉 Often used to disable security software. - 💻 Command Line Execution (CMD Access)
Provides full command-line control, allowing execution of scripts and administrative commands. - 🧩 Registry Editing (Regedit Access)
Attackers can modify system registry settings to maintain persistence or alter system behavior.
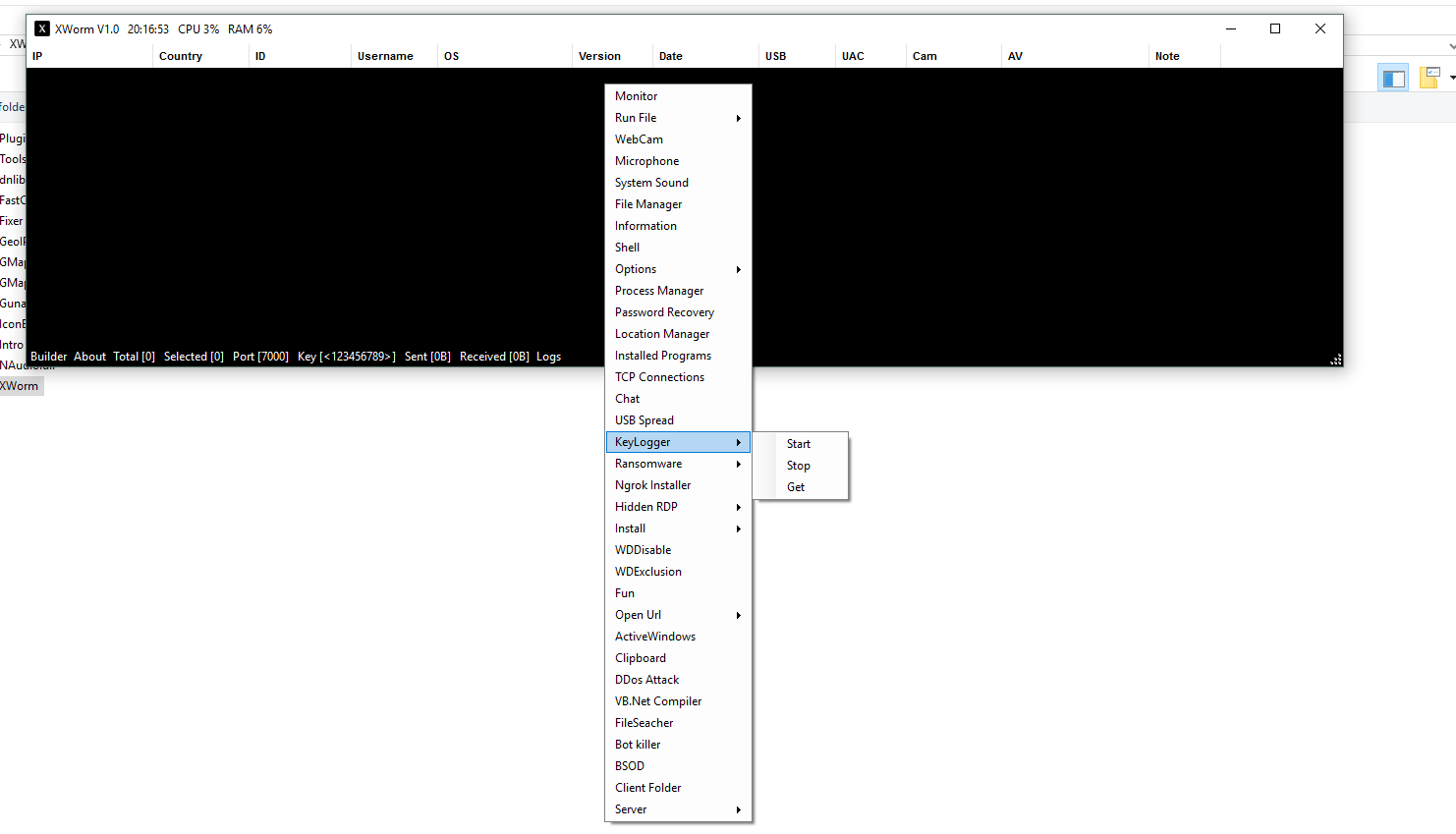
🎥 Surveillance & Monitoring Features
- 📷 Webcam Access
Enables capturing images or recording video through the victim’s camera. - 🎤 Microphone Recording
Records surrounding audio, potentially capturing private conversations. - 🖥️ Screen Monitoring
Allows screenshots or live desktop viewing. - ⌨️ Keylogger Functionality
Records every keystroke typed by the user.
👉 This is one of the most dangerous features as it captures passwords, messages, and sensitive data.
💣 System Manipulation & Exploitation Tools
- 🧠 In-Memory Code Execution
Executes malicious code without saving files on disk, making detection harder. - 🖼️ Wallpaper Modification
Changes desktop visuals, often used for intimidation or ransomware-like behavior. - 💥 Forced System Crash (BSOD)
Can intentionally crash the system, disrupting normal usage. - 🚫 Disable Task Manager
Prevents users from stopping malicious processes.
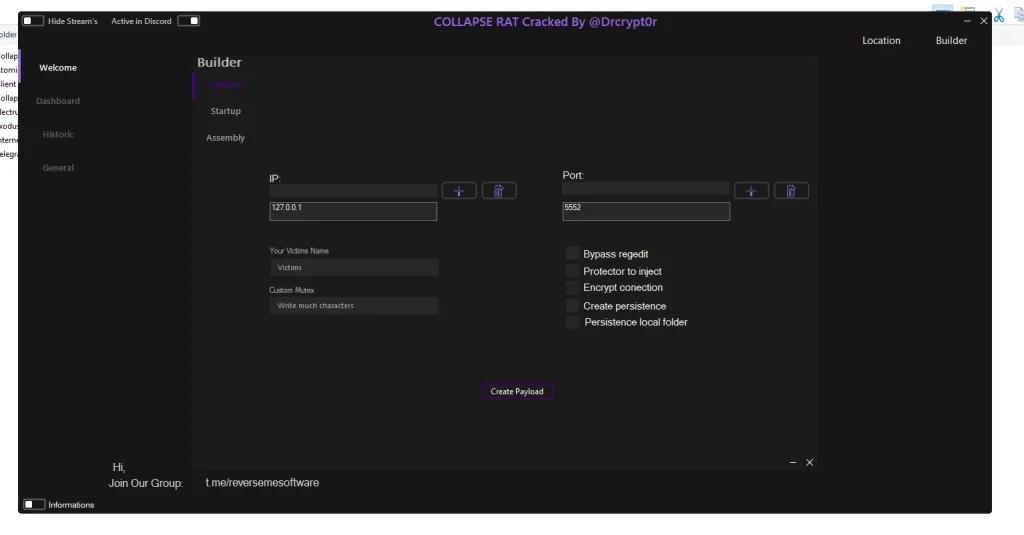
⚙️ Builder & Custom Payload Configuration
- 🧩 Custom Payload Creation
Attackers can configure malware settings before deployment. - 🔕 Silent Mode Options
Allows the malware to operate without any visible indicators. - 🧪 Anti-Virtual Machine Detection
Detects if running in a virtual environment (used by analysts).
👉 Helps avoid detection during security testing.
⚠️ Risks of Using Cracked RAT Software
- 🔓 Hidden Backdoors
Cracked versions often include additional malicious code that can steal attacker data. - 🕵️ Traceability Issues (Poor OpSec)
Using common builds makes it easier for investigators to track activities. - 🚨 High Detection Rate
Popular cracked tools are quickly identified by antivirus software.
Download Collapse HVNC RAT 2026
🧾 Conclusion Collapse HVNC RAT 2026
Collapse HVNC RAT 2026 represents a highly advanced remote access threat, combining stealth technology with full system control and surveillance features.
Its ability to operate invisibly through HVNC makes it particularly dangerous. For cybersecurity professionals, understanding such tools is essential for building stronger defenses.
👉 Implementing strong endpoint protection, monitoring unusual processes, and maintaining updated security systems are critical steps in preventing such threats.
❓ FAQs about Collapse HVNC RAT 2026
❓ What is HVNC in cybersecurity?
HVNC (Hidden Virtual Network Computing) is a technique that allows attackers to control a system through an invisible desktop session.
❓ Is Collapse HVNC RAT 2026 legal?
No, using such tools without permission is illegal and violates cybersecurity laws worldwide.
❓ Why are cracked RATs risky?
They often contain hidden malware, backdoors, and are easily detected by modern security systems.
❓ How can I protect my system?
- Install reliable antivirus or EDR solutions
- Avoid downloading unknown files
- Keep your system updated
- Monitor unusual background processes
❓ Who should study such tools?
Cybersecurity professionals, ethical hackers, and IT administrators for defensive purposes.