🧠 Understanding SVCHOST Injector 2026 Attacks in Modern Windows Systems
In modern cybersecurity threats, attackers frequently use process injection techniques to hide malicious code inside legitimate system processes. One of the most targeted processes is svchost.exe, a critical Windows component responsible for hosting system services.
Security researchers refer to these attacks as SVCHOST Injector 2026, where malicious software attempts to execute code inside the trusted Windows process to avoid detection.
Understanding how these attacks work is essential for cybersecurity professionals, IT administrators, and system defenders.
⚙️ What Is SVCHOST Injector 2026 in Windows?
svchost.exe (Service Host) is a core Windows system process used to run multiple background services required for operating system functionality.
🔍 Key Characteristics of svchost.exe
• 🖥️ Hosts multiple Windows services
• 🔐 Digitally signed by Microsoft
• 🌐 Handles network communication for many services
• ⚙️ Runs continuously in the background
Because of its trusted status, attackers often attempt to abuse this process for stealth operations.
🕵️ What Is a SVCHOST Injector 2026 Attack?
A SVCHOST injector attack is a type of process injection malware technique where malicious code is executed inside the memory of the svchost.exe process.
💡 How the Attack Works
• 🧬 Malicious code loads into system memory
• 🧠 The code injects itself into svchost.exe
• 🌐 Network communication occurs through the trusted process
• 🛡️ Security tools may initially trust the activity
This technique allows malware to blend with legitimate system activity, making detection more difficult.
🎯 Why Attackers Target svchost.exe with SVCHOST Injector 2026
Cybercriminals select svchost.exe because it is one of the most trusted processes in Windows.
🔑 Reasons It Is Targeted
• 🛡️ Trusted by security software
• 🌐 Commonly uses network connections
• ⚙️ Runs continuously on every Windows system
• 📊 Appears normal inside Task Manager
Because many legitimate services run inside it, malicious activity may remain hidden among normal operations.
🔬 Common Techniques Used in Process Injection
Modern malware families use several code injection techniques to hide inside system processes.
🧩 Popular Injection Methods
• 🧠 Remote Thread Injection
Creates a thread inside another process to run malicious code.
• 💾 DLL Injection
Loads a malicious dynamic library into a trusted process.
• ⚡ Process Hollowing
Replaces the memory of a legitimate process with malicious code.
• 🧬 Reflective Injection
Loads malware directly into memory without writing files to disk.
These techniques are widely used in advanced persistent threats (APT) and modern malware campaigns.
🚨 Warning Signs of svchost.exe Malware Activity
Detecting malicious activity hidden in svchost.exe requires monitoring system behavior rather than file names.
🔍 Suspicious Indicators
• 🌐 Unexpected network connections
• ⚙️ svchost.exe communicating with unknown IP addresses
• 💾 High memory usage from a single svchost instance
• 🧬 Unknown modules loaded inside svchost.exe
• 🖥️ svchost.exe spawning unusual processes
Security monitoring tools often detect these anomalies during endpoint threat analysis.
🛡️ How Security Tools Detect Process Injection
Modern Endpoint Detection and Response (EDR) solutions use behavioral monitoring to identify injection attacks.
🔐 Detection Techniques
• 🧠 Memory scanning
• 📊 Behavioral analysis
• 🔍 API monitoring
• ⚙️ parent-child process inspection
• 🌐 abnormal network traffic analysis
These techniques help security teams identify hidden threats inside legitimate processes.
🔧 Best Practices to Protect Against Injection Attacks
Organizations and individuals can reduce risk by implementing strong endpoint security practices.
✅ Security Recommendations
• 🔐 Keep Windows and security software updated
• 🛡️ Use advanced EDR or antivirus solutions
• 📊 Monitor unusual network activity
• ⚙️ Enable system logging and auditing
• 🧠 Restrict unnecessary administrative privileges
Strong security policies significantly reduce the chances of process injection malware succeeding.
📊 Why Understanding svchost Attacks Matters
Process injection remains one of the most widely used techniques in modern cyber attacks. By abusing trusted Windows components like svchost.exe, attackers can hide malicious activity for extended periods.
For cybersecurity professionals, understanding these techniques helps improve:
• 🛡️ malware detection
• 🔍 incident response
• 📊 threat intelligence
• ⚙️ system hardening
The better defenders understand these tactics, the stronger their protection becomes.
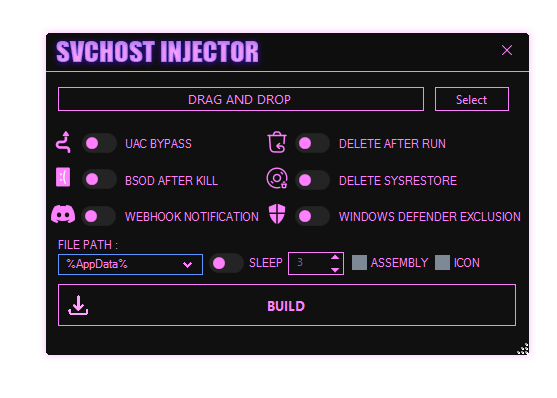
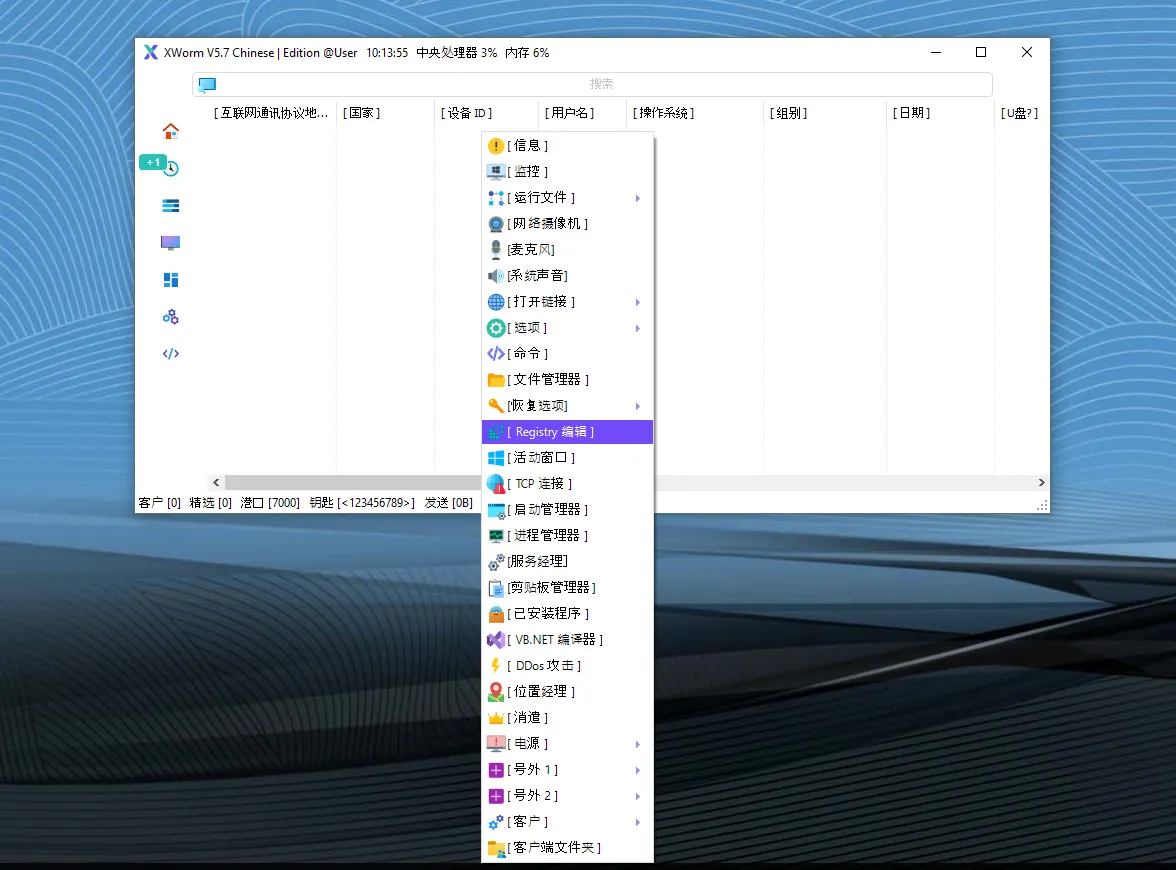
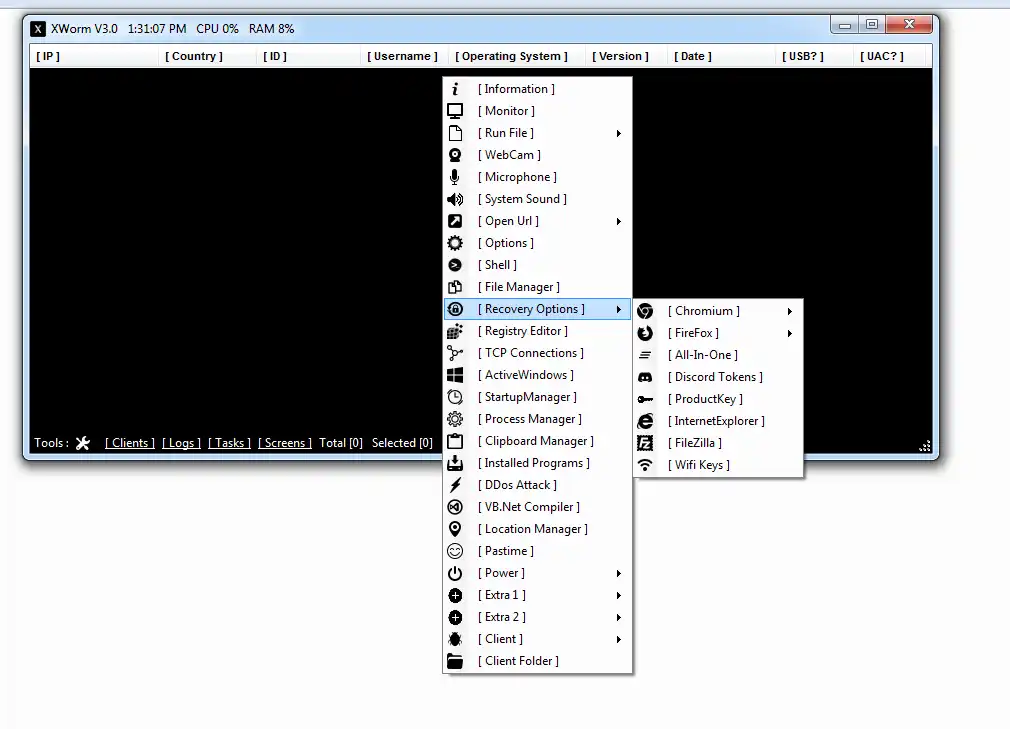
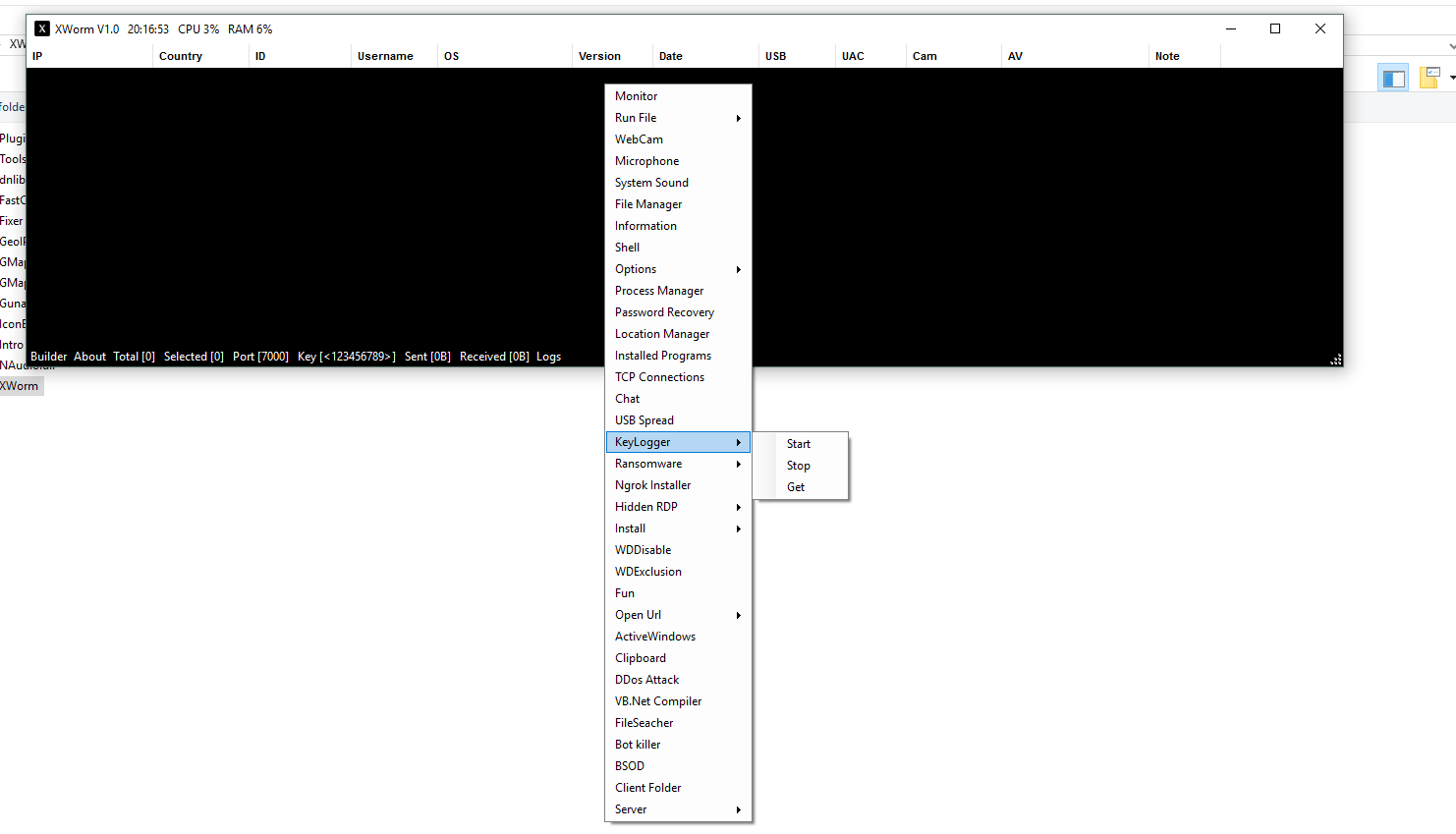
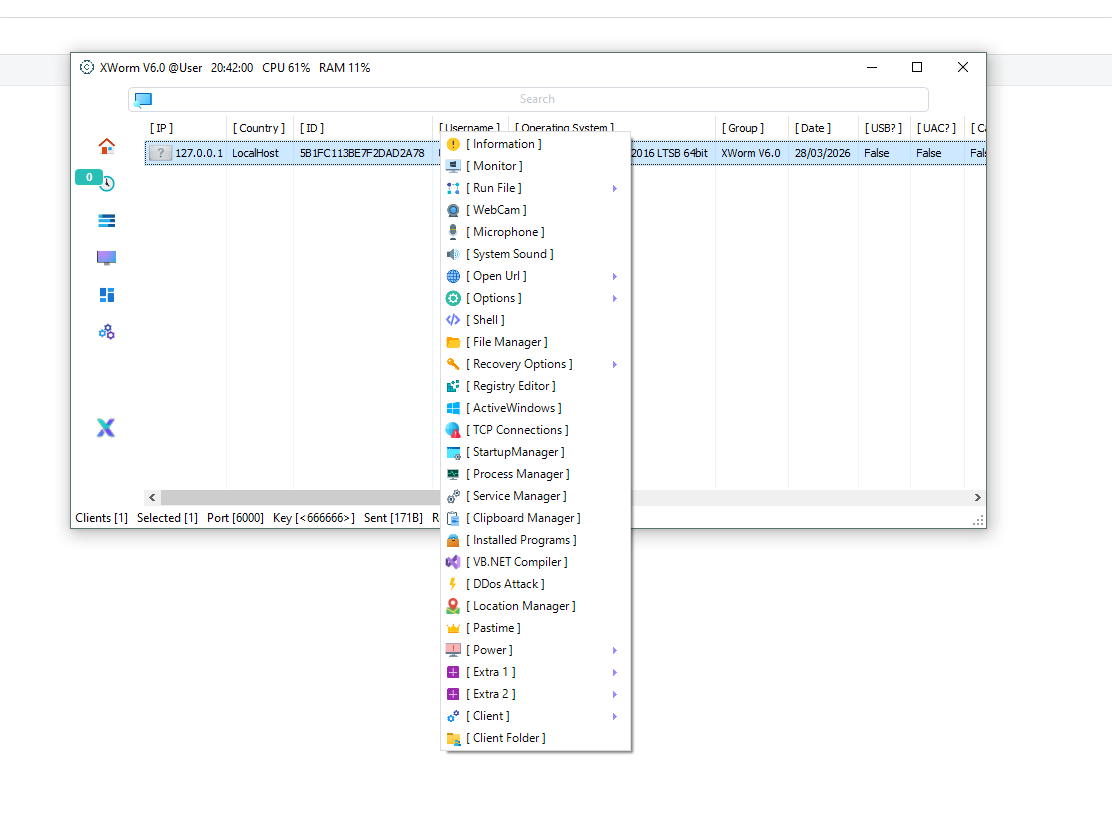
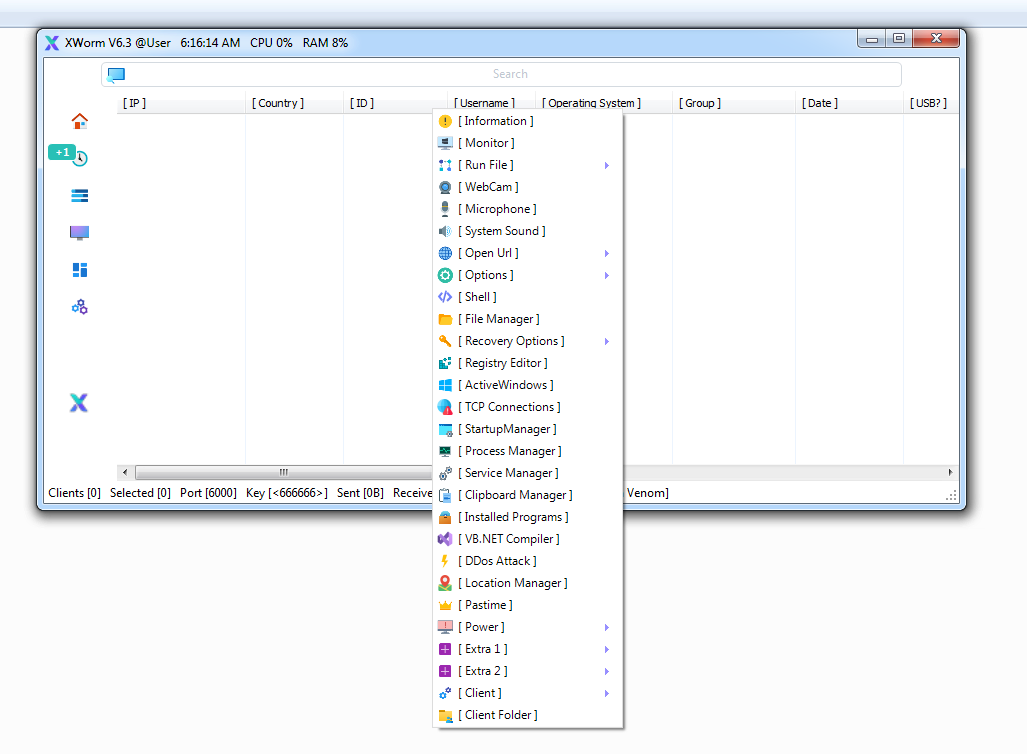
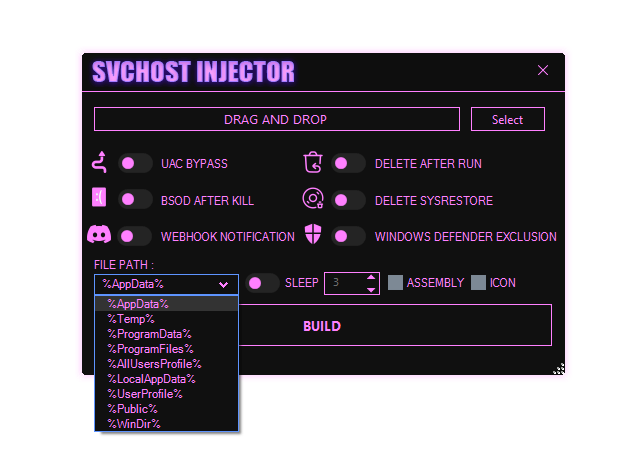
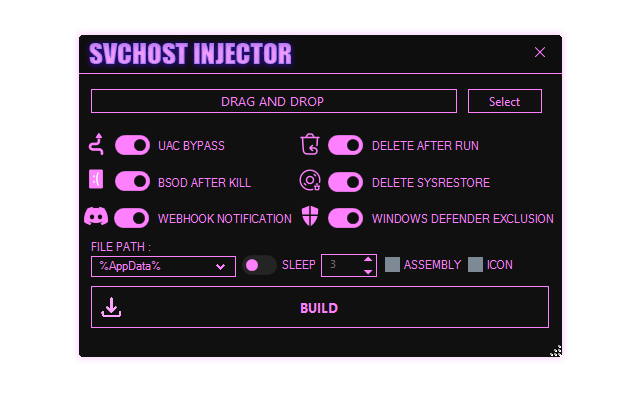
Download SVCHOST Injector 2026
🧾 Conclusion
SVCHOST injection attacks highlight how attackers exploit trusted Windows processes to remain hidden inside operating systems.
By learning how these attacks operate and how security tools detect them, organizations can strengthen their cyber defense strategies and endpoint protection.
Continuous monitoring, updated security tools, and strong system policies remain the best defense against modern injection-based malware threats.
❓ FAQ
❓ What is svchost.exe in Windows?
svchost.exe is a Windows system process responsible for hosting multiple background services required for the operating system.
❓ What is process injection malware?
Process injection is a technique where malicious code executes inside another legitimate process to hide from security software.
❓ Why do attackers use svchost.exe?
Attackers target svchost.exe because it is trusted, always running, and commonly performs network communication.
❓ Can antivirus detect svchost injection attacks?
Modern antivirus and EDR solutions can detect suspicious behavior such as abnormal memory activity or unusual network connections.