🛡️ Abko RAT 2026: Complete Cybersecurity Analysis & Defense Guide
In today’s rapidly evolving cybersecurity landscape, Remote Access Trojans (RATs) have become one of the most dangerous tools in the hands of cybercriminals. Among the latest threats identified in intelligence reports is Abko RAT 2026, a sophisticated malware strain designed to infiltrate Windows systems and grant attackers full remote control.
This in-depth guide explores how Abko RAT 2026 works, its key features, attack capabilities, and—most importantly—how individuals and organizations in the US and Europe can defend against it. Whether you’re a cybersecurity enthusiast, IT professional, or business owner, understanding this threat is essential for maintaining digital safety.
⚙️ What is Abko RAT 2026?
🧠 Understanding Remote Access Trojans
- Definition and core functionality:
Remote Access Trojans are a category of malware that allow attackers to control a victim’s computer remotely. Abko RAT 2026 operates silently in the background, giving unauthorized users access to files, applications, and system settings. Unlike traditional viruses, RATs focus on stealth and long-term control rather than immediate damage. - Stealth and persistence mechanisms:
Abko RAT 2026 is engineered to remain undetected for extended periods. It uses hidden installation paths, disguises itself as legitimate software, and ensures persistence by adding itself to system startup processes. This allows it to survive reboots and maintain continuous access. - Target operating systems:
The malware primarily targets Windows environments, including enterprise and personal systems. This makes it particularly dangerous for businesses relying on Windows-based infrastructure across the US and Europe.
🧰 Builder Interface: Lowering the Barrier for Cybercrime
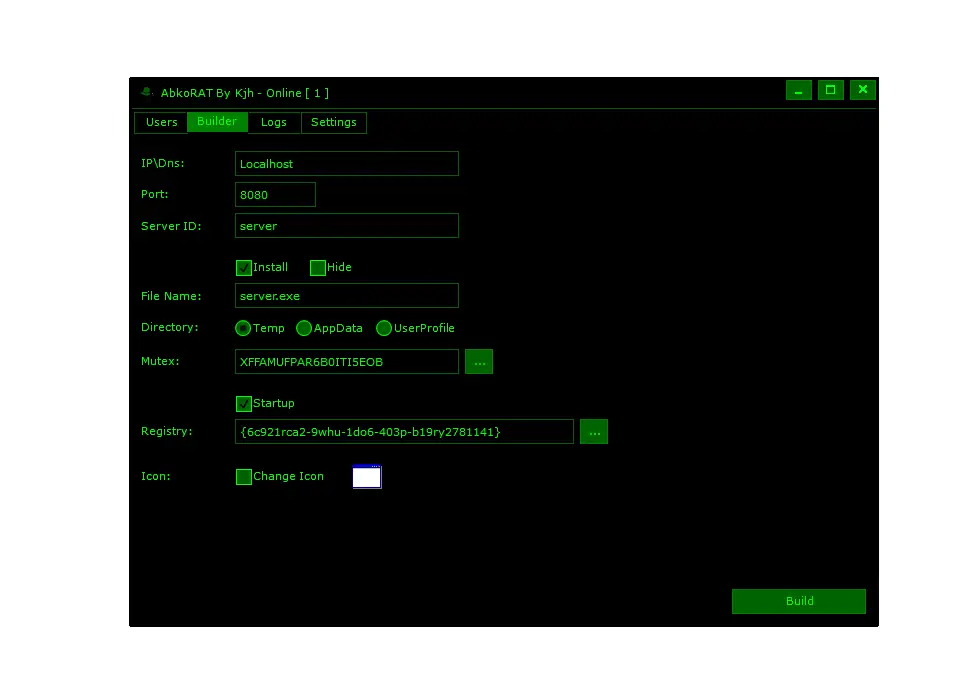
🛠️ Malware Customization Made Easy
- User-friendly configuration panel:
The builder interface allows attackers to create customized malware payloads without advanced technical skills. With simple input fields for IP addresses, ports, and server IDs, even beginners can generate functional RAT samples. This democratization of cybercrime tools significantly increases the volume of attacks. - Persistence and installation options:
Attackers can define installation directories such as AppData or Temp folders, ensuring the malware blends with legitimate system files. Options like “Startup” guarantee automatic execution during system boot, making removal difficult for average users. - Stealth and disguise features:
The “Change Icon” function allows the malware to mimic trusted applications like PDF readers or system utilities. Combined with hidden execution modes, this significantly reduces suspicion and increases infection success rates.
🖥️ Control Panel: Full System Takeover
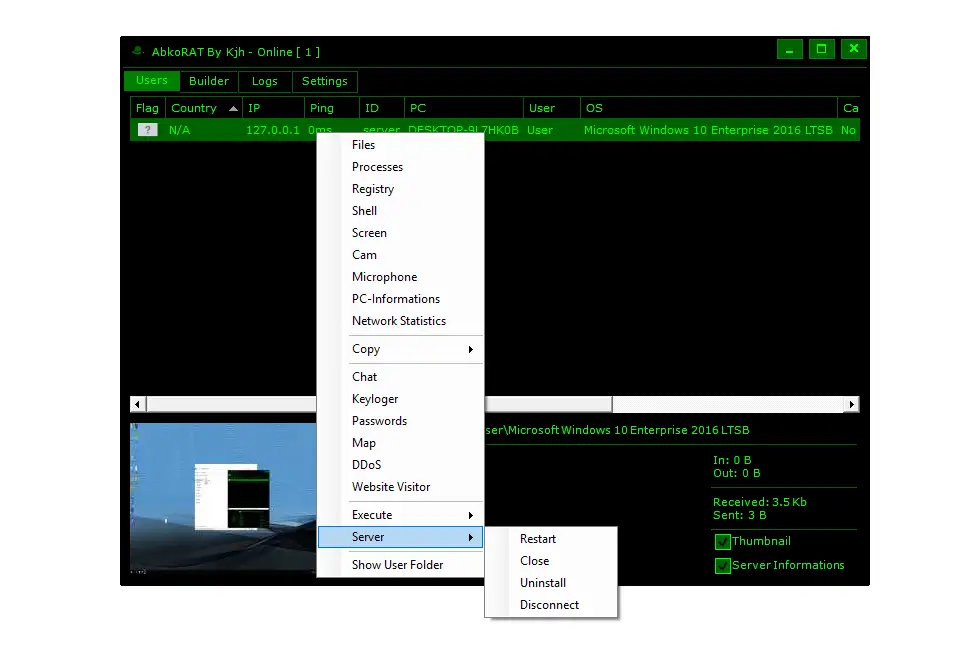
🎮 Real-Time Remote Administration
- Comprehensive victim dashboard:
Once deployed, attackers gain access to a control panel displaying victim details such as IP address, system name, OS version, and connection status. This centralized dashboard allows efficient management of multiple infected systems simultaneously. - Advanced surveillance tools:
Modules like screen capture, webcam access, and microphone recording enable real-time spying. Attackers can monitor user behavior, capture sensitive conversations, and gather confidential information without detection. - Data theft capabilities:
Built-in tools such as keyloggers and password extractors allow attackers to capture login credentials, banking details, and browsing activity. This information is often sold on dark web marketplaces or used for identity theft.
⚡ Execute Function: The Most Dangerous Feature
💣 Remote Command Execution
- Unlimited command execution:
The Execute feature allows attackers to run any command or script on the victim’s system. This includes installing additional malware such as ransomware or cryptocurrency miners, significantly increasing the damage. - System manipulation and control:
Attackers can disable antivirus programs, modify system settings, and access sensitive files. This level of control effectively turns the victim’s computer into a fully controlled remote device. - Botnet and DDoS capabilities:
Infected machines can be used to launch Distributed Denial-of-Service (DDoS) attacks. By combining multiple compromised systems, attackers can overwhelm websites and online services, causing significant disruptions.
📡 Feature Set: A Multi-Purpose Cyber Weapon
🔎 Extensive Functional Modules
- File and process management:
Attackers can browse, upload, download, and delete files on the victim’s system. They can also terminate or start processes, giving them control over running applications and services. - Remote shell access:
The shell module provides command-line access with elevated privileges. This allows attackers to execute advanced administrative tasks and automate malicious activities. - Network monitoring and statistics:
Real-time data transfer metrics help attackers track how much information is being exfiltrated. This ensures efficient use of compromised systems and avoids detection by maintaining low traffic levels.
📊 Logs and Tracking: Organized Cybercrime Operations
📁 Attack Monitoring and Analytics
- Detailed connection logs:
The malware records timestamps, IP addresses, and system details for each connection. This helps attackers track active and inactive victims, ensuring efficient management of infected systems. - Operational intelligence:
Logs allow attackers to identify high-value targets and prioritize them for further exploitation. This structured approach mirrors legitimate business analytics but for malicious purposes. - Resale of access:
Access to compromised systems can be sold to other cybercriminals. These “initial access brokers” profit by providing entry points into corporate networks, increasing the overall threat landscape.
🖼️ Victim Profiling and Data Collection
🧾 Deep System Intelligence
- Comprehensive system information:
Abko RAT 2026 collects detailed metadata including installation paths, registry entries, and system configurations. This helps attackers understand the environment and plan further attacks. - Live screen previews:
Thumbnail previews provide real-time snapshots of user activity. This allows attackers to monitor sensitive actions such as online banking or email communication. - Low-traffic stealth techniques:
By transmitting small amounts of data, the malware avoids triggering network-based detection systems. This makes it particularly dangerous in environments without advanced monitoring tools.
🔌 Server Controls: Managing Infected Machines
⚙️ Command and Control Functions
- Session management tools:
Attackers can restart, disconnect, or uninstall the malware remotely. This flexibility allows them to adapt to different scenarios, such as avoiding detection during forensic investigations. - Persistence maintenance:
Restart functions ensure the malware remains active even after system reboots. This guarantees long-term access to compromised systems. - Covering tracks:
The uninstall feature can remove traces of the malware after an attack is completed, making forensic analysis more challenging for investigators.
⚙️ Attacker Settings Panel: Optimized for Stealth
🕶️ Hidden Operations
- Stealthy interface options:
Features like system tray minimization and transparent UI help attackers hide their activities on their own machines. This reduces the risk of exposure during operations. - Automation features:
Auto-start options for screen and camera monitoring allow instant surveillance upon connection. This ensures attackers capture valuable data without delay. - Notification management:
Sound alerts and notifications help attackers manage multiple victims efficiently, ensuring no important activity goes unnoticed.
🚨 Real-World Threat Context
🌐 Malware Distribution and Availability
- Presence in underground repositories:
Abko RAT 2026 has been linked to collections of malware tools shared across online platforms. These repositories often reappear under different names, making enforcement difficult. - Continuous evolution:
The malware appears to be actively maintained, with version tracking and potential update mechanisms. This ensures it remains effective against modern security solutions. - Widespread risk:
Due to its ease of use and powerful features, Abko RAT poses a significant threat to both individuals and organizations across developed regions.
🛡️ How to Protect Against Abko RAT 2026
🔐 Practical Cybersecurity Measures
- Use advanced endpoint protection:
Deploy modern antivirus and Endpoint Detection and Response (EDR) solutions that can identify behavioral anomalies. These tools are essential for detecting stealthy threats like RATs. - Avoid untrusted downloads:
Never run executable files from unknown sources. Many RAT infections occur through phishing emails or malicious downloads disguised as legitimate software. - Monitor system activity:
Keep an eye on unusual behavior such as unexpected network traffic, high CPU usage, or unknown startup programs. Early detection can prevent serious damage. - Regular updates and patching:
Ensure your operating system and software are always up to date. Security patches fix vulnerabilities that malware often exploits. - User awareness training:
Educate employees and users about phishing attacks and safe browsing practices. Human error remains one of the biggest cybersecurity risks.
Download Abko RAT 2026
🧠 Conclusion
Abko RAT 2026 represents a powerful and dangerous evolution in Remote Access Trojans. With its user-friendly builder, extensive surveillance capabilities, and advanced control features, it poses a serious threat to both individuals and organizations.
However, with proper awareness, strong security practices, and proactive monitoring, the risks can be significantly reduced. Cybersecurity is not just about tools—it’s about understanding threats and staying one step ahead.
❓ FAQs
❓ What is Abko RAT 2026 used for?
Abko RAT 2026 is used by cybercriminals to remotely control infected computers, steal data, monitor users, and launch attacks such as DDoS or ransomware deployment.
❓ How does Abko RAT 2026 infect systems?
It typically spreads through phishing emails, malicious downloads, or fake software installers that trick users into executing infected files.
❓ Can antivirus software detect Abko RAT 2026?
Yes, modern antivirus and EDR solutions can detect it, especially with updated definitions and behavioral analysis features enabled.
❓ What are the signs of a RAT infection?
Common signs include slow performance, unusual network activity, unknown programs running, and unauthorized access to files or devices.
❓ Is Abko RAT 2026 dangerous for businesses?
Absolutely. It can compromise sensitive corporate data, disrupt operations, and lead to financial and reputational damage.
❓ How can I remove Abko RAT 2026 from my system?
Use trusted antivirus tools, perform a full system scan, and consider professional cybersecurity assistance for complete removal.
❓ Are RATs legal to use?
No, using RATs without authorization is illegal and considered a serious cybercrime in most countries.
❓ How can organizations prevent RAT attacks?
By implementing strong security policies, using advanced protection tools, training employees, and monitoring network activity continuously.