🐀 Desert Rat 2026: Complete Android Malware Technical & SEO Guide
The evolution of mobile cyber threats has accelerated significantly, with Android devices becoming the primary target for advanced malware campaigns across the United States and Europe. One of the most sophisticated examples is Desert Rat 2026, a modular Remote Access Trojan (RAT) designed for full-scale device compromise.
Unlike traditional malware, Desert Rat 2026 operates as a complete cyber intrusion ecosystem, combining infection delivery, code manipulation, remote control, surveillance, and persistence mechanisms in a unified framework.
This article provides a deep technical, semantic SEO breakdown of Desert Rat 2026 for cybersecurity analysts, researchers, and digital safety professionals.
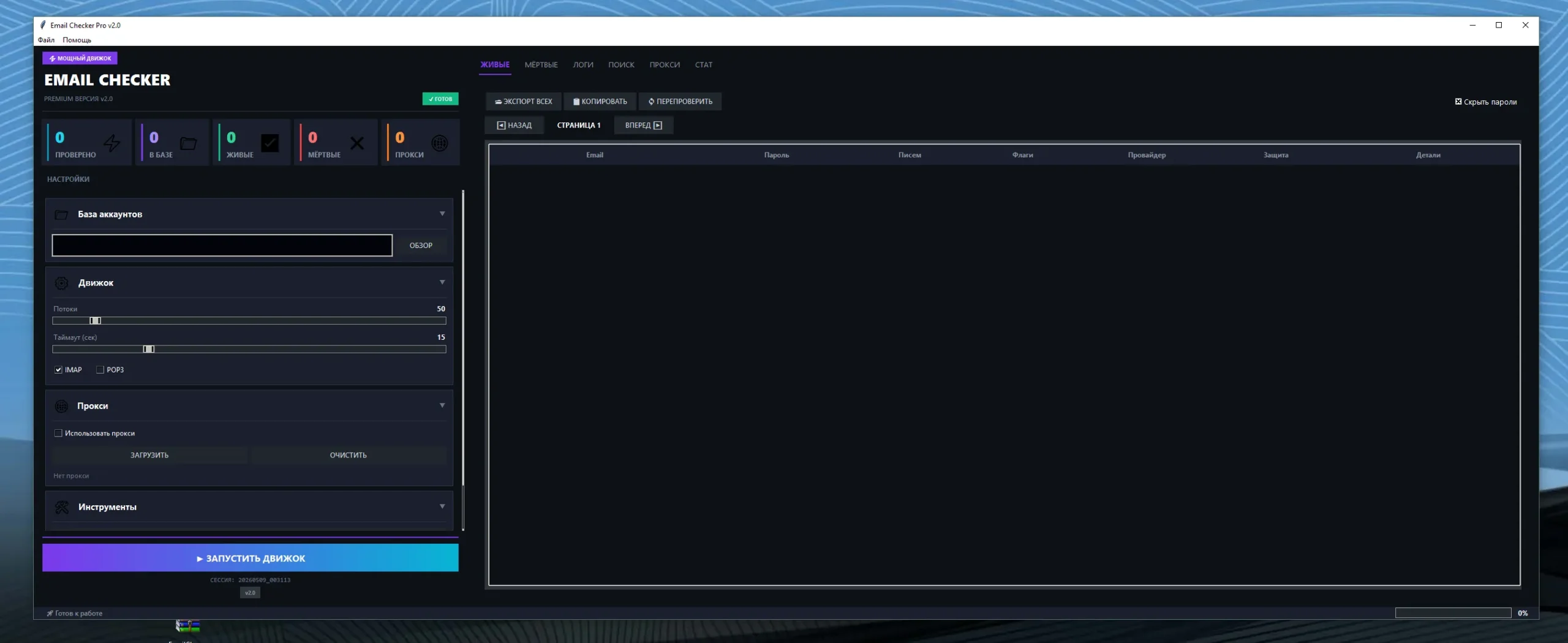
📦 🧪 APK Dropper Module (Initial Infection Layer of Desert Rat 2026)
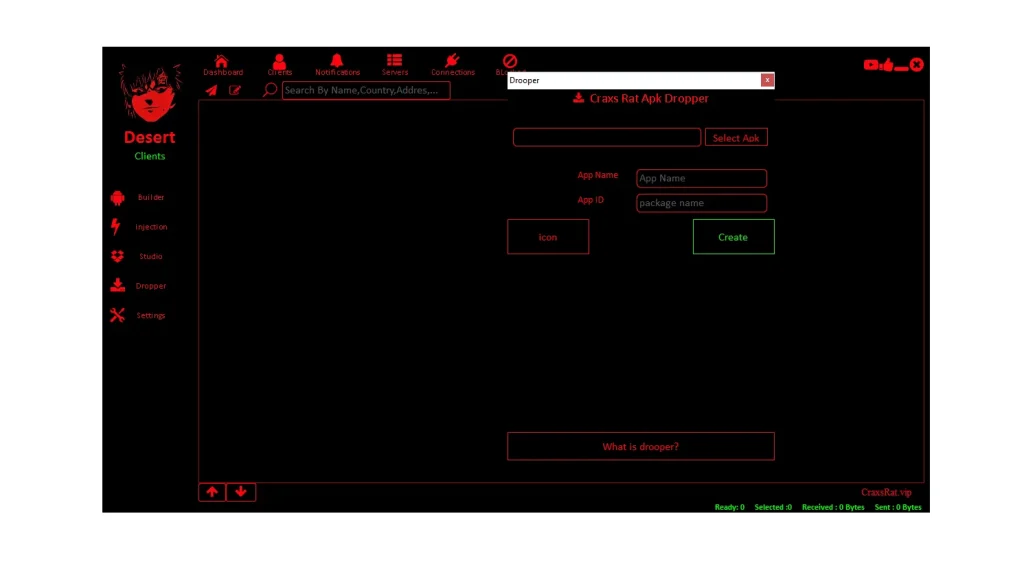
The APK Dropper is the first stage of Desert Rat 2026 infection, responsible for delivering malicious payloads through disguised applications.
📲 APK Binding System:
📌 Deep Technical Explanation:
- 📲: APK Binding in Desert Rat 2026 merges malicious code with legitimate Android applications:
- The infected app behaves normally during installation and daily usage:
- Users unknowingly install hidden malware alongside functional software:
- The malicious payload activates automatically after installation:
- It exploits user trust in familiar applications:
- It is commonly distributed through phishing and third-party APK sources:
- It bypasses basic user awareness and visual verification:
- It significantly increases infection success rates in real-world attacks:
➡️ This technique makes Desert Rat 2026 highly effective in trust-based exploitation attacks.
🎭 App Identity Spoofing System:
📌 Deep Technical Explanation:
- 🎭: This system allows Desert Rat 2026 to modify application identity:
- Attackers change app name, icon, and package signature:
- It mimics trusted services like banking apps and system updates:
- It manipulates user perception during installation:
- Users rely on visual recognition instead of technical validation:
- It increases installation success probability significantly:
- It enables region-based and targeted cyber campaigns:
- It strengthens psychological manipulation strategies:
➡️ This is a core social engineering vector in Desert Rat 2026 attacks.
⚡ Silent Payload Execution Engine:
📌 Deep Technical Explanation:
- ⚡: After installation, Desert Rat 2026 executes silently:
- No alerts or visible system notifications are triggered:
- Background services initialize immediately:
- It connects to remote command-and-control servers:
- It activates surveillance and data collection modules:
- Execution remains hidden from user interface visibility:
- It ensures stealth during early infection stages:
- It reduces detection probability significantly:
➡️ Silent execution enables undetected system compromise and persistence.
🔁 Mass APK Generation System:
📌 Deep Technical Explanation:
- 🔁: This system automates creation of multiple Desert Rat 2026 payloads:
- Attackers can generate infected APKs in bulk:
- Each version can be customized for specific targets:
- It supports global-scale cyberattack campaigns:
- Automation reduces manual attacker workload:
- It enables continuous malware evolution:
- It increases operational scalability significantly:
- It supports distributed infection strategies:
➡️ This feature supports industrial-scale cybercrime operations.
🛠️ 🧩 APK Studio Module (Desert Rat 2026 Modification Engine)
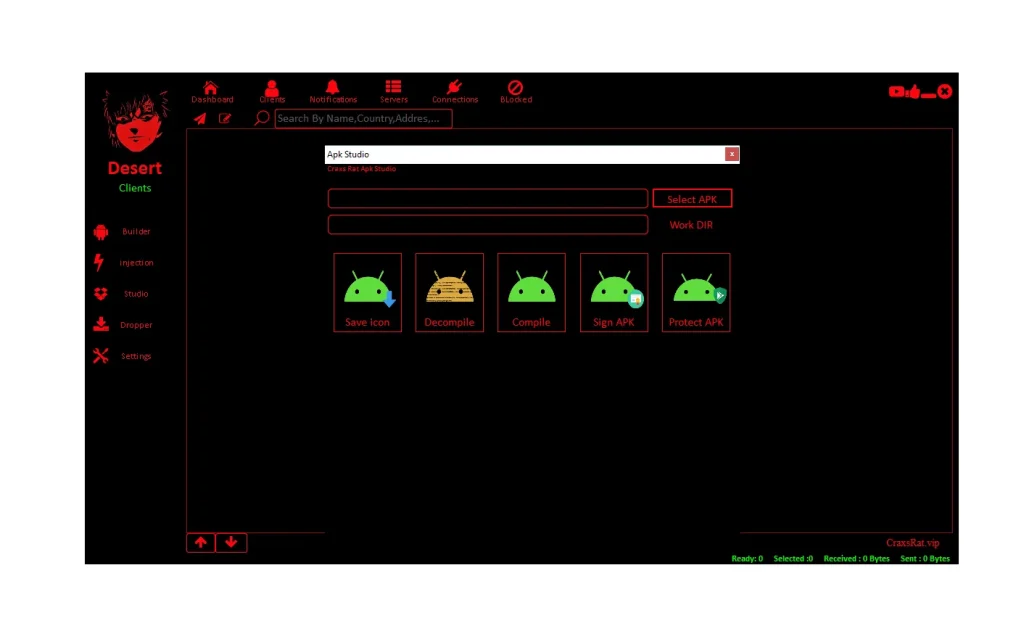
APK Studio is the reverse engineering and modification core of Desert Rat 2026.
🧬 APK Decompilation System:
📌 Deep Technical Explanation:
- 🧬: Converts compiled APKs into readable source code:
- Reveals internal application architecture:
- Allows identification of injection points:
- Helps attackers understand application logic:
- Exposes security mechanisms within apps:
- Enables precise malware insertion:
- Supports deep reverse engineering workflows:
- Forms foundation of modification process:
➡️ This enables deep structural exploitation of Android apps.
✏️ Code Injection System:
📌 Deep Technical Explanation:
- ✏️: Inserts malicious code into legitimate applications:
- Enables hidden execution of malware functions:
- Applications continue normal operation:
- Users remain unaware of compromise:
- Malware integrates into system workflows:
- Supports surveillance and remote control functions:
- Enhances persistence and stealth:
- Widely used in advanced mobile attacks:
➡️ This is one of the most critical Desert Rat 2026 attack mechanisms.
🔐 APK Signing System:
📌 Deep Technical Explanation:
- 🔐: Ensures modified APKs can be installed on Android devices:
- Android requires valid digital signatures for execution:
- Attackers use custom or self-signed certificates:
- It bypasses installation warnings:
- It increases perceived legitimacy:
- It ensures cross-device compatibility:
- It supports smooth malware deployment:
- It is essential for infection success:
➡️ Signing ensures Desert Rat 2026 appears system-compliant and trusted.
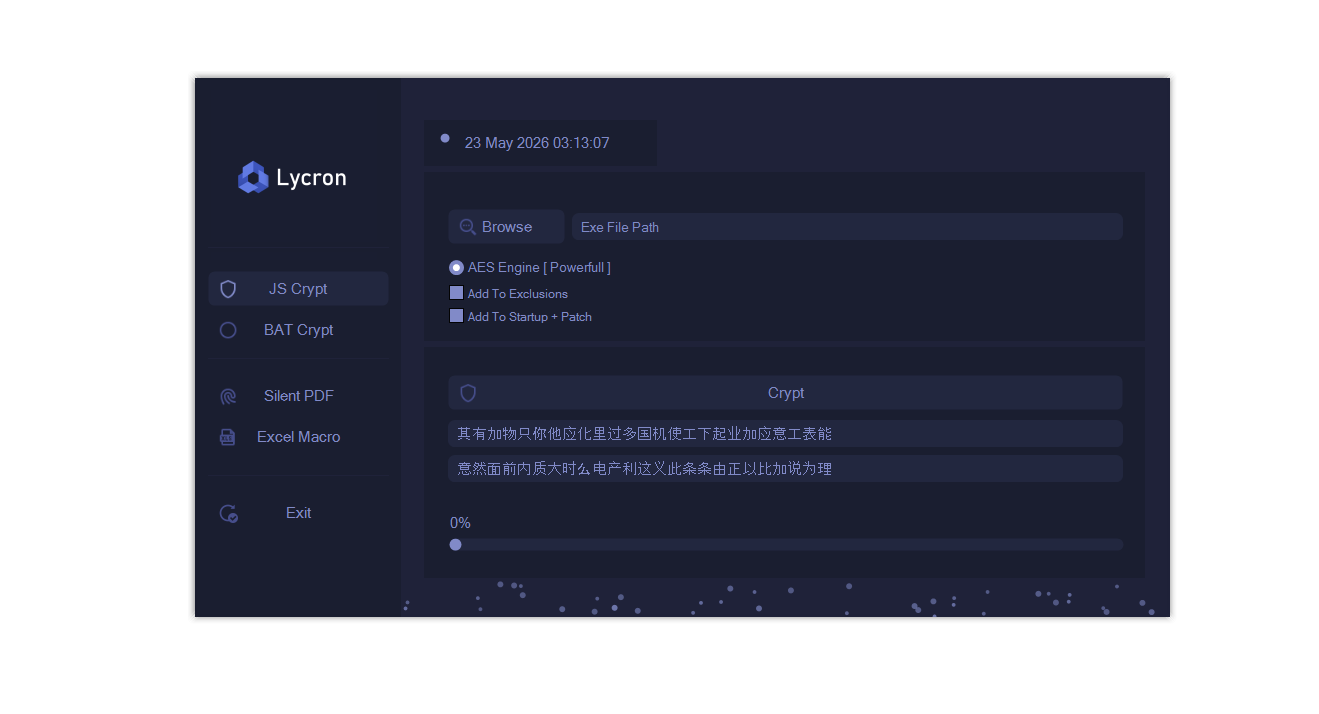
🛡️ Obfuscation & Anti-Analysis Layer:
📌 Deep Technical Explanation:
- 🛡️: Hides malicious logic from detection tools:
- Renames variables and functions dynamically:
- Encrypts execution flow and internal logic:
- Prevents reverse engineering attempts:
- Reduces antivirus detection rates:
- Increases malware lifespan in real environments:
- Complicates forensic investigation:
- Strengthens stealth capabilities:
➡️ Obfuscation is a core anti-detection strategy in Desert Rat 2026.
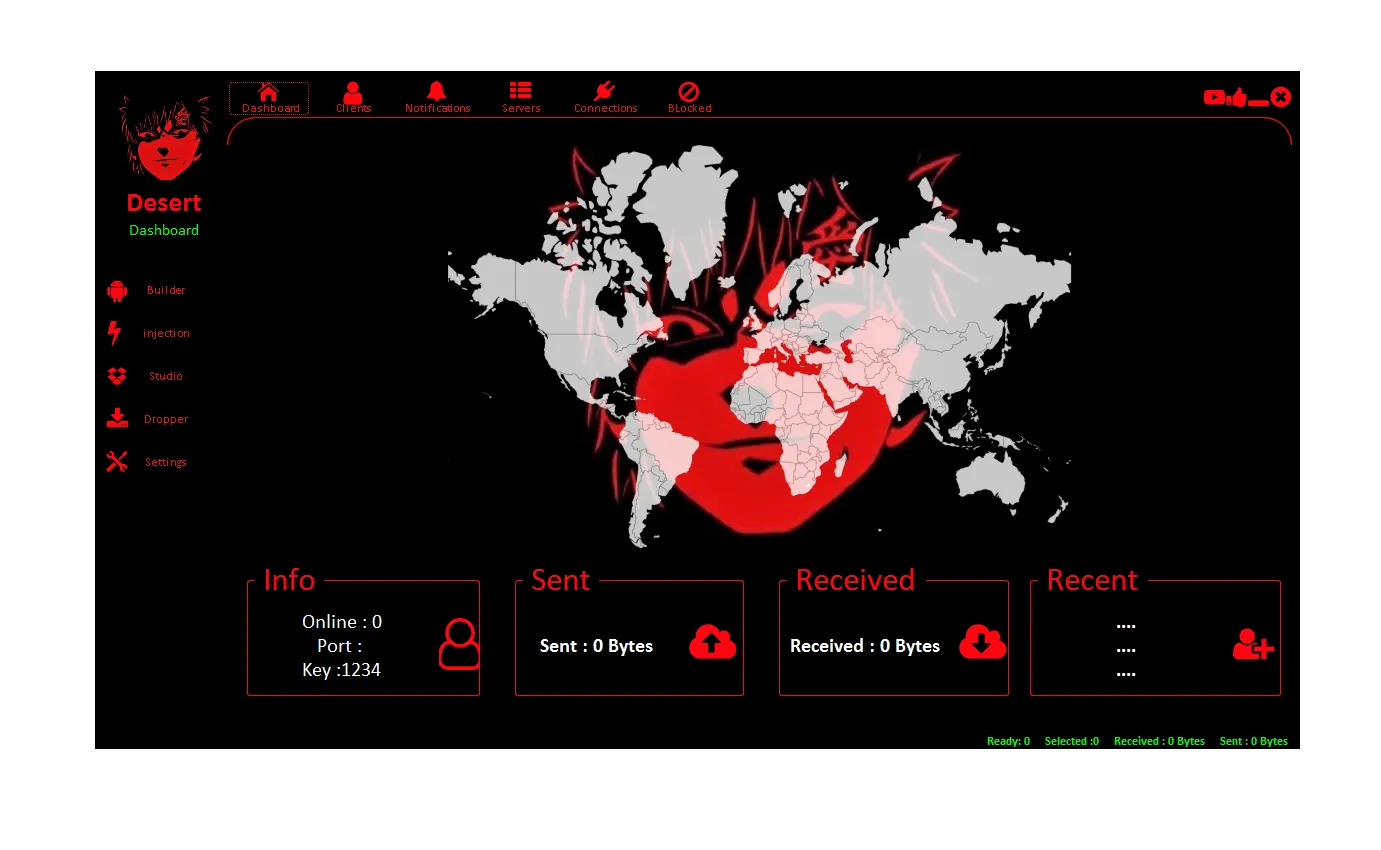
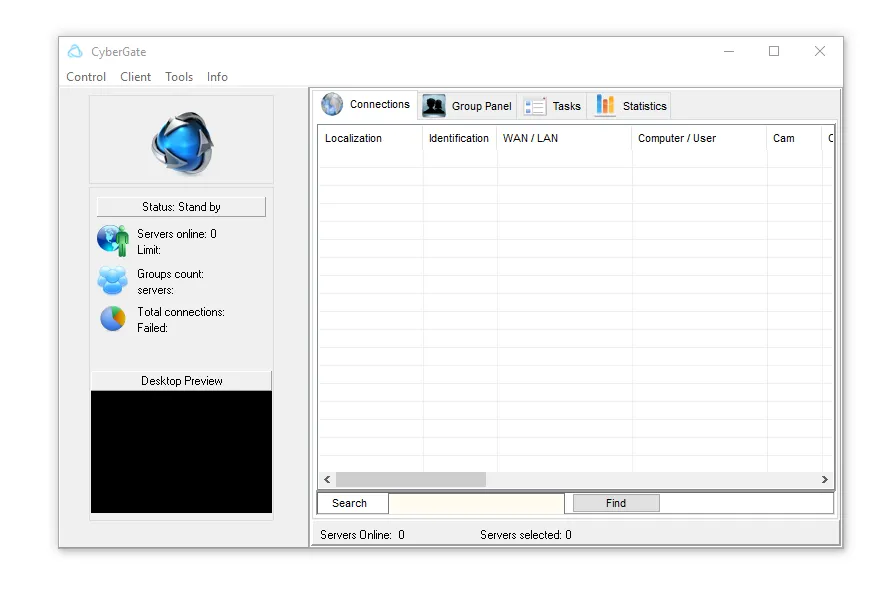
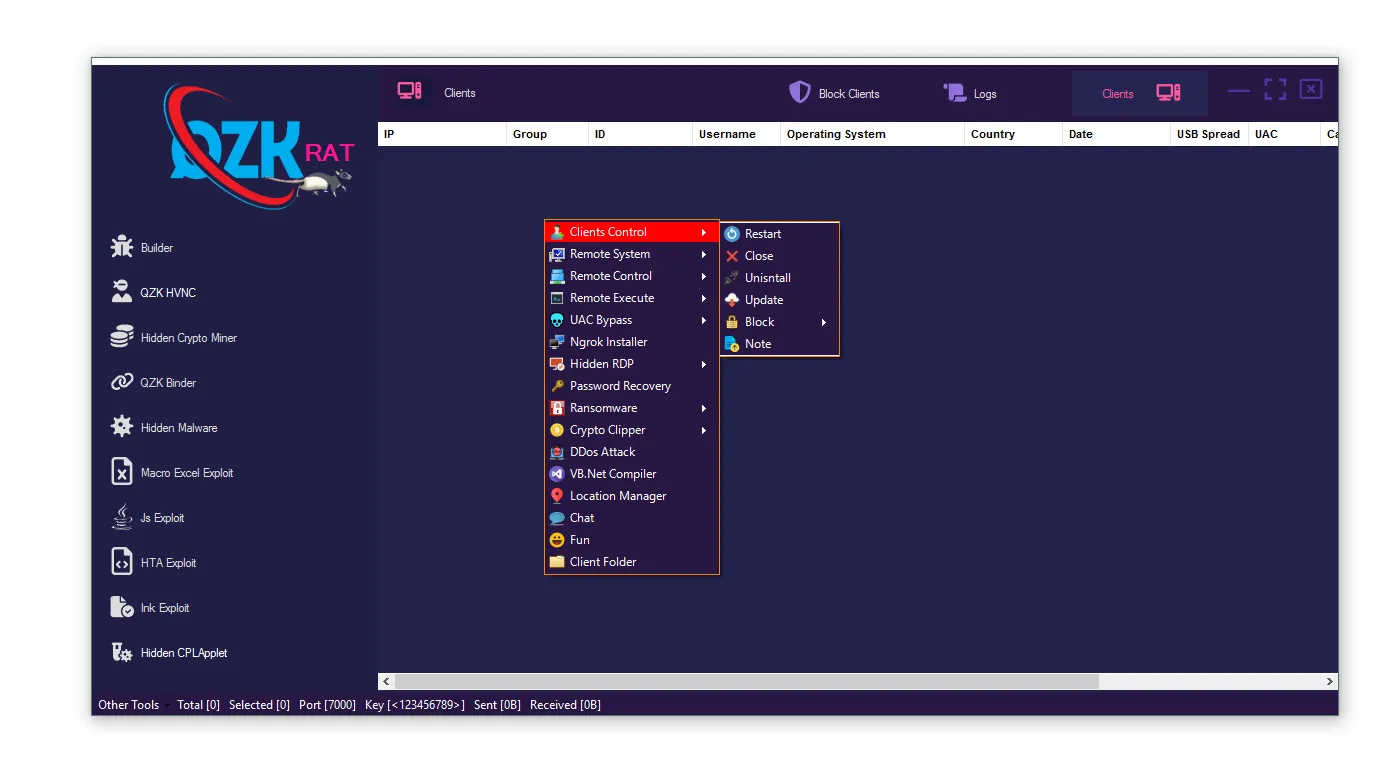
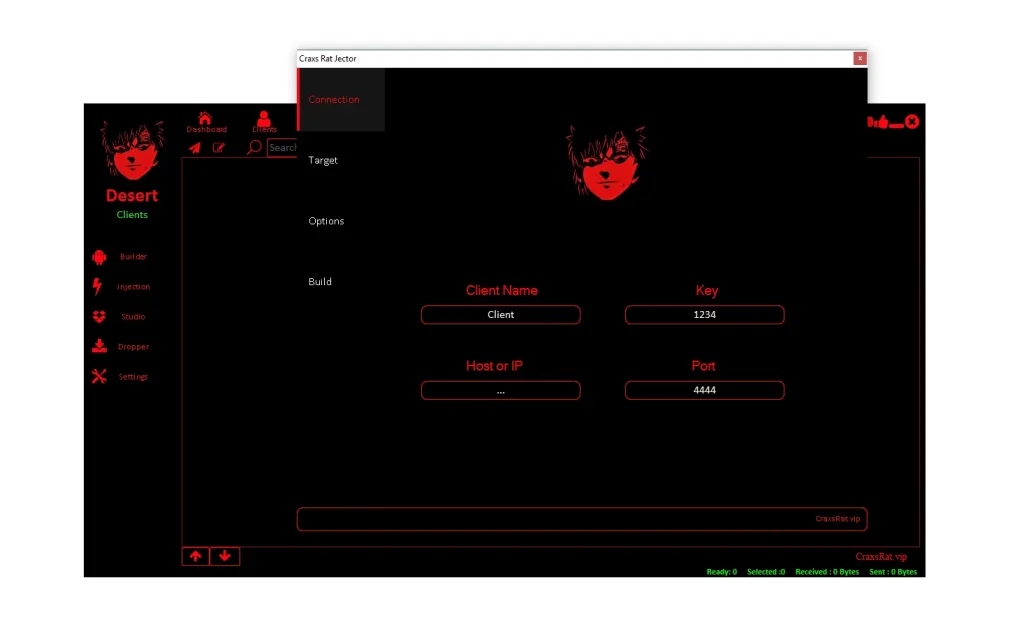
⚙️ 🧠 Builder System (Command & Control Center of Desert Rat 2026)
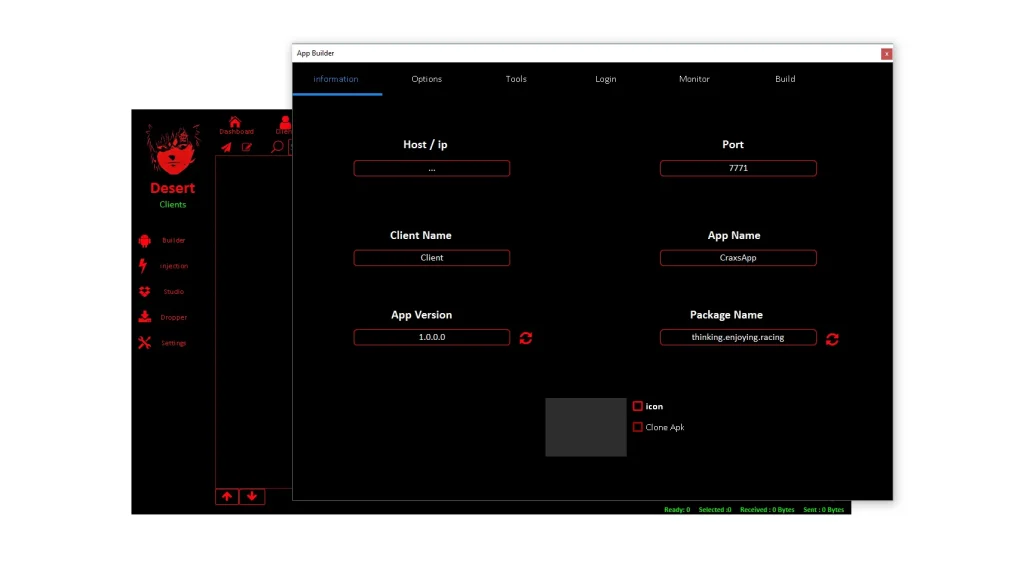
The Builder is the central configuration panel for malware operators.
🧾 Builder Login System:
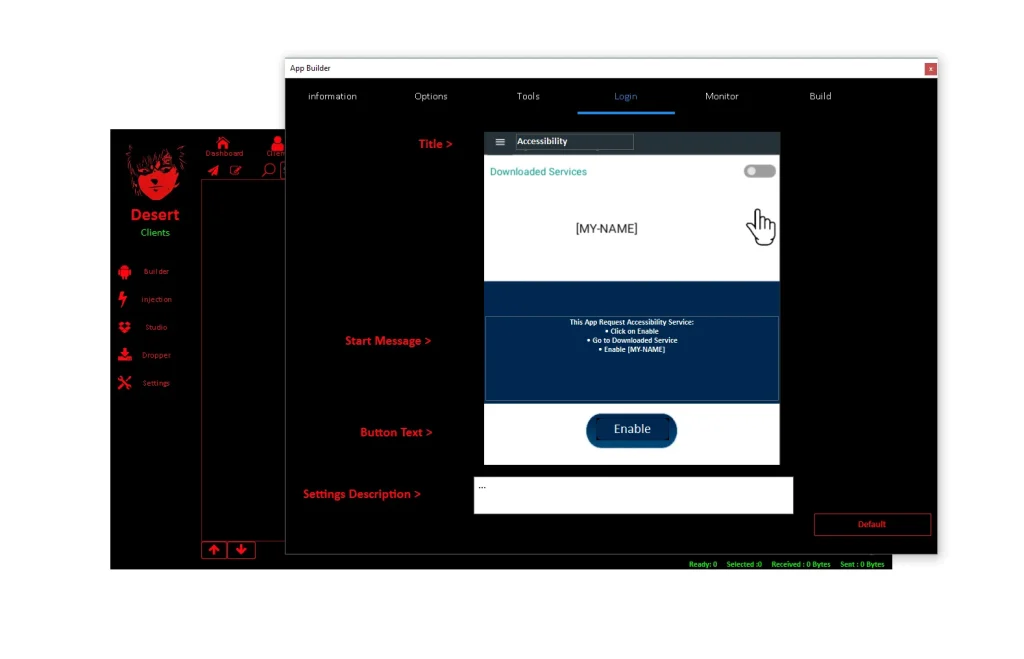
📌 Deep Technical Explanation:
- 🧾: Authentication system for malware operators:
- Restricts access using credentials or keys:
- Prevents unauthorized usage:
- Protects configuration environment:
- Supports multi-operator environments:
- Secures malware infrastructure:
- Acts as entry gateway to control panel:
- Ensures operational security:
📊 Builder Monitor System:
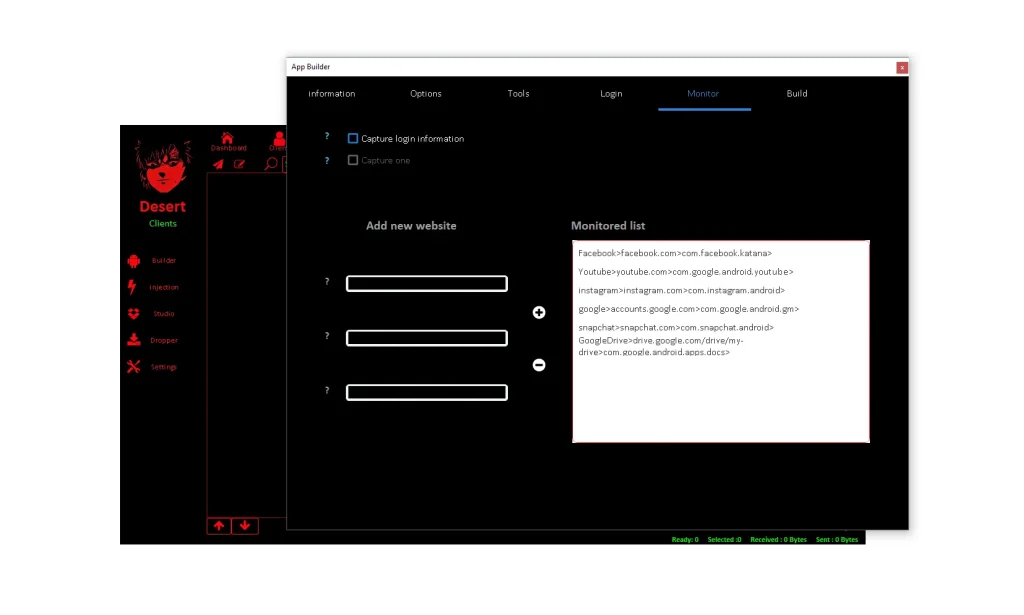
📌 Deep Technical Explanation:
- 📊: Real-time monitoring dashboard:
- Displays infected device status:
- Tracks online and offline devices:
- Monitors data transmission activity:
- Identifies high-value targets:
- Provides operational intelligence:
- Supports campaign optimization:
- Enables live cyber supervision:
⚙️ Builder Options System:
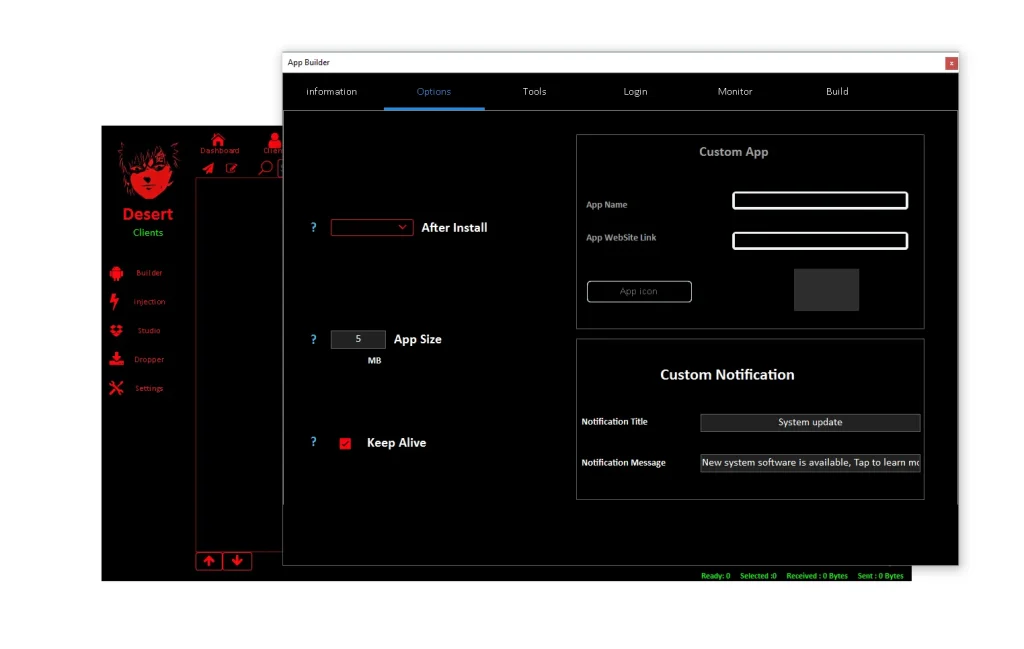
📌 Deep Technical Explanation:
- ⚙️: Configures malware behavior settings:
- Customizes notifications and fake alerts:
- Controls payload execution flow:
- Enables social engineering customization:
- Adjusts stealth parameters:
- Supports geographic targeting:
- Enhances deception effectiveness:
- Improves infection success rate:
🧰 Builder Tools System:
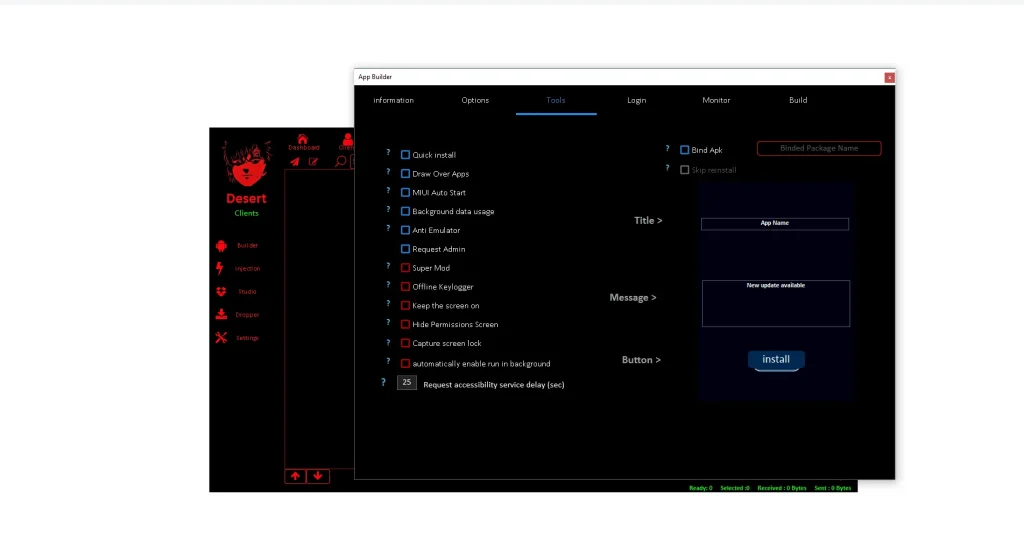
📌 Deep Technical Explanation:
- 🧰: Advanced malware functionality toolkit:
- Enables persistence mechanisms:
- Controls overlay attack features:
- Manages system permissions:
- Automates background execution:
- Supports remote command functions:
- Enhances malware stability:
- Expands operational flexibility:
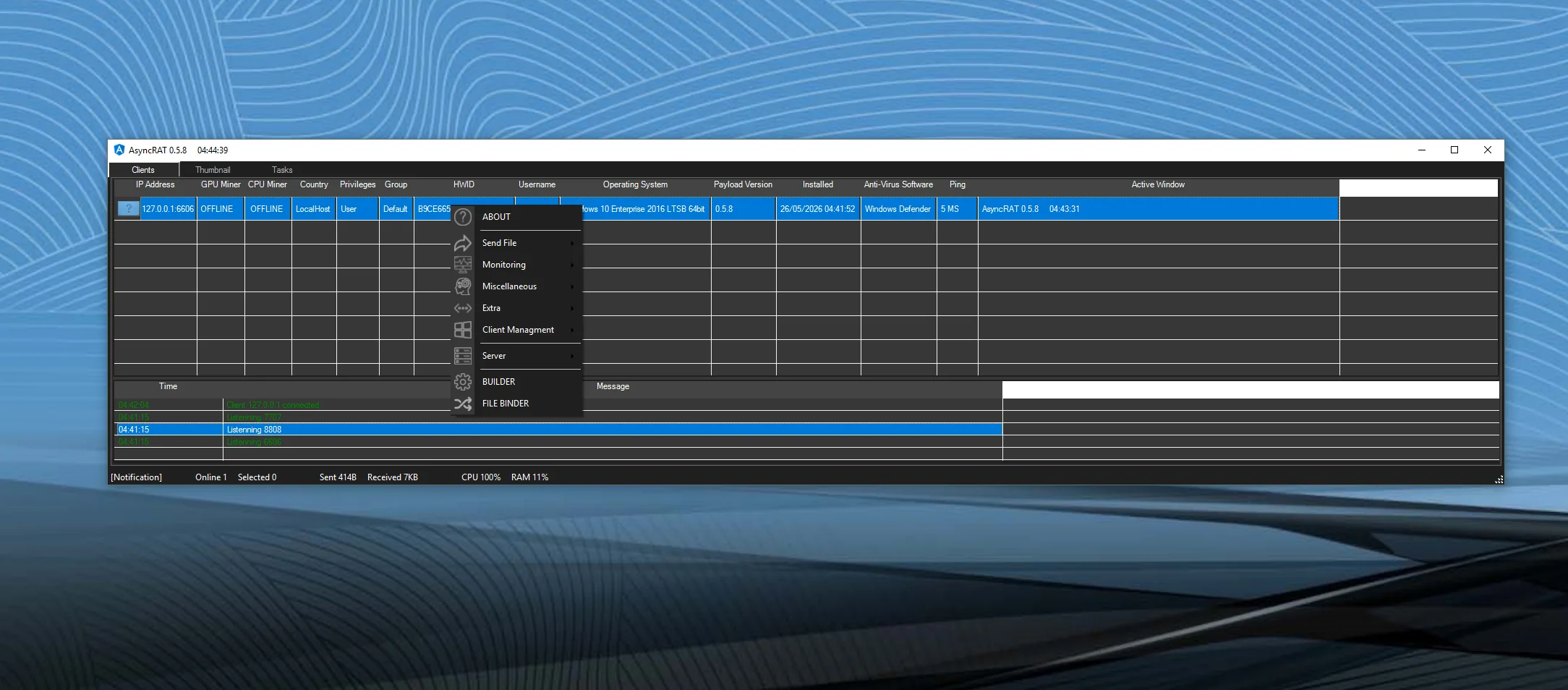
📡 📱 Client System (Post-Infection Control Layer of Desert Rat 2026)
📂 Client Manager System:
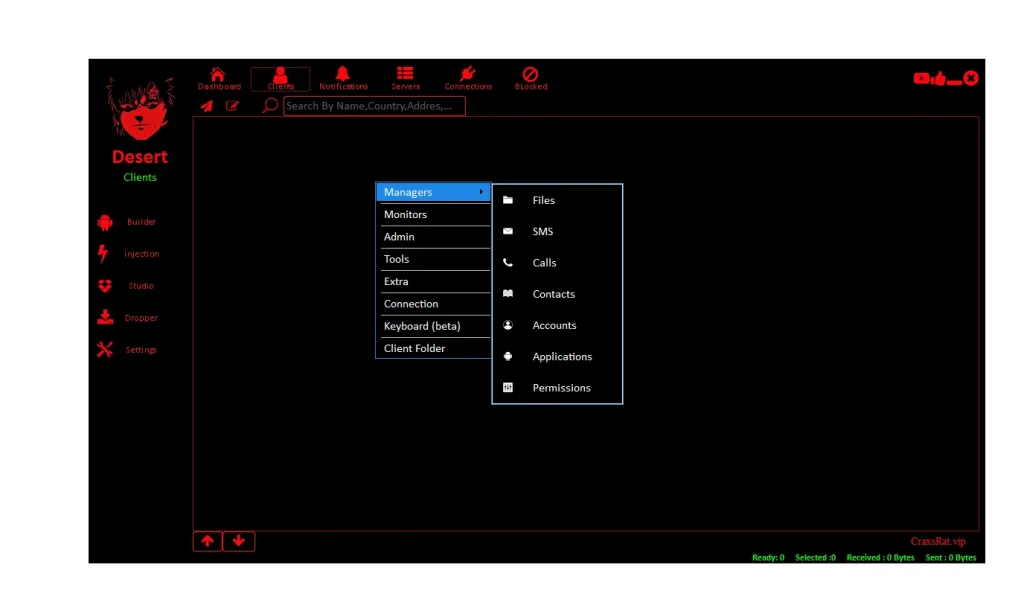
📌 Deep Technical Explanation:
- 📂: Central control dashboard for infected devices:
- Enables file browsing and extraction:
- Manages applications remotely:
- Accesses device storage data:
- Supports multiple device control:
- Extracts sensitive information:
- Acts as command center:
- Enables full remote administration:
🛠️ Client Tools System:
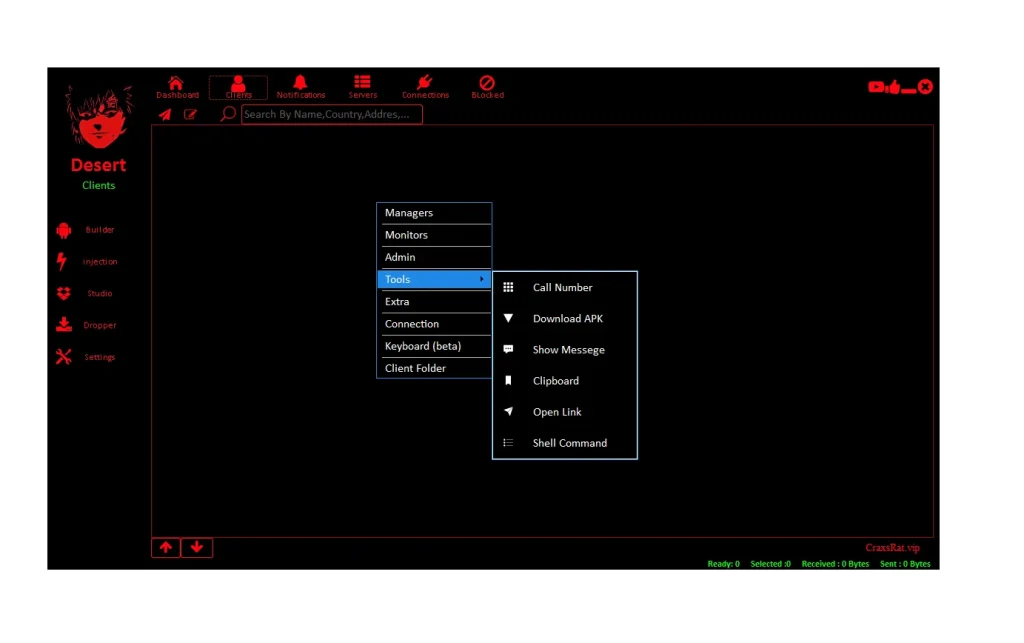
📌 Deep Technical Explanation:
- 🛠️: Remote execution engine:
- Sends commands to infected devices:
- Opens URLs remotely:
- Controls clipboard data:
- Executes system actions:
- Manipulates applications:
- Enables live exploitation:
- Provides real-time control:
👁️ Client Monitor System:
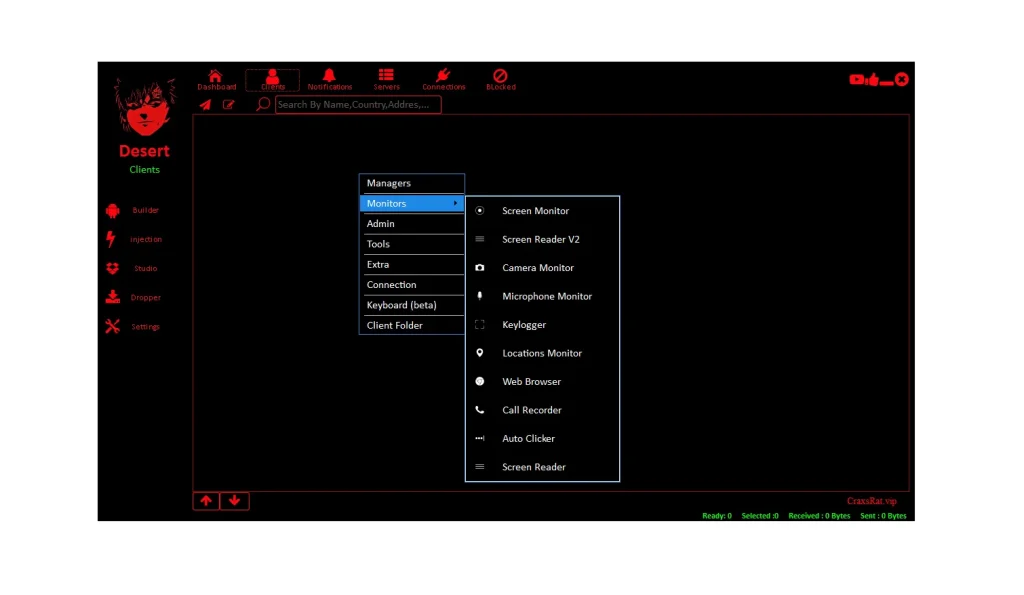
📌 Deep Technical Explanation:
- 👁️: Surveillance and tracking engine:
- Captures screen activity:
- Tracks GPS location:
- Monitors application usage:
- Collects behavioral data:
- Records user interactions:
- Enables continuous monitoring:
- Provides full device visibility:
📡 Client Extra System:
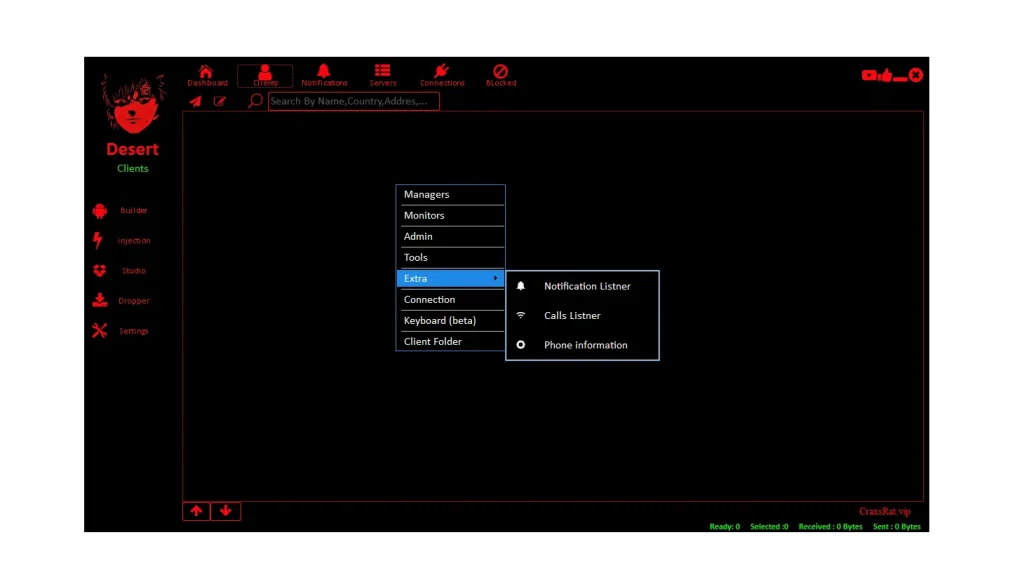
📌 Deep Technical Explanation:
- 📡: Extended intelligence collection system:
- Reads notifications and alerts:
- Captures call logs and metadata:
- Extracts system information:
- Tracks communication behavior:
- Enhances surveillance depth:
- Supports identity intelligence gathering:
- Strengthens long-term monitoring:
🧬 🔗 Injection System (Deep Compromise Layer of Desert Rat 2026)
🎯 Injection Target System:
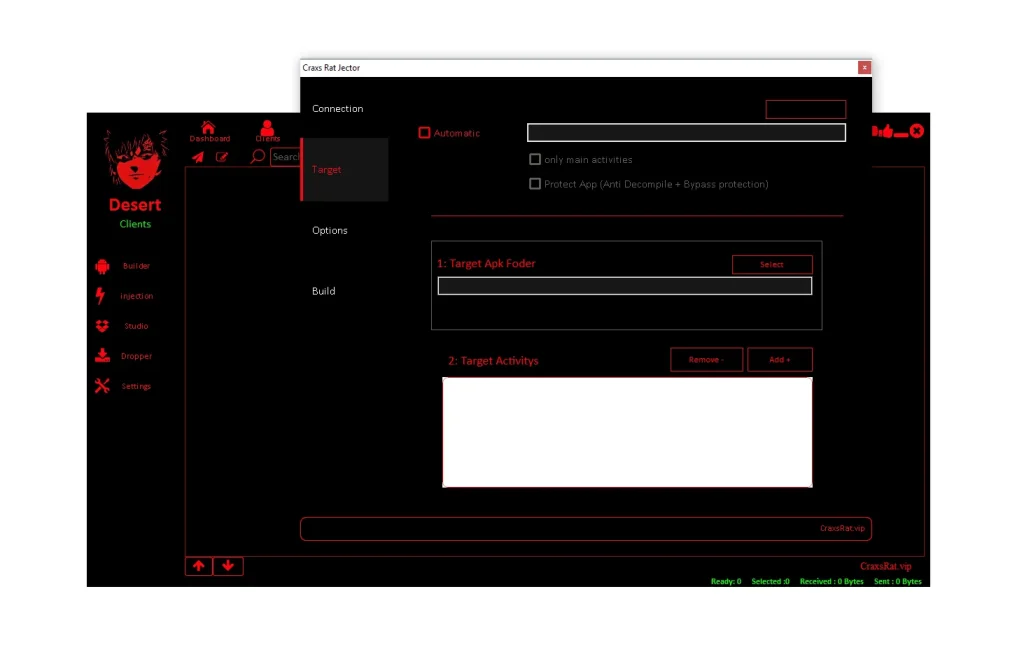
📌 Deep Technical Explanation:
- 🎯: Selects legitimate applications for infection:
- Uses trusted apps as malware carriers:
- Expands distribution reach:
- Exploits user trust in known software:
- Targets popular applications:
- Integrates into supply chain attack model:
- Increases infection probability:
- Maximizes stealth distribution:
⚙️ Injection Execution System:
📌 Deep Technical Explanation:
- ⚙️: Embeds malware into application structure:
- Modifies internal application logic:
- Maintains normal functionality:
- Enables hidden execution:
- Integrates deeply into system processes:
- Ensures long-term compromise:
- Avoids detection during usage:
- Strengthens persistence mechanisms:
🛡️ Injection Protection Layer:
📌 Deep Technical Explanation:
- 🛡️: Prevents detection and analysis:
- Blocks reverse engineering attempts:
- Encrypts injected components:
- Prevents modification or removal:
- Protects attacker infrastructure:
- Extends malware lifecycle:
- Reduces forensic visibility:
- Enhances operational security:
🔓 Permission Automation System:
📌 Deep Technical Explanation:
- 🔓: Automates Android permission management:
- Grants accessibility access silently:
- Escalates privileges without user consent:
- Reduces user interaction requirements:
- Bypasses manual approval systems:
- Enables full device compromise:
- Increases infection efficiency:
- Supports complete system takeover:
Download Desert Rat 2026
🧾 Final Conclusion
Desert Rat 2026 represents a fully modular Android malware ecosystem designed for infection, surveillance, modification, and remote control.
Its architecture includes:
- APK Dropper (infection layer)
- APK Studio (modification engine)
- Builder System (command center)
- Client System (post-infection control)
- Injection System (deep compromise layer)
This makes Desert Rat 2026 one of the most advanced and structured Android malware frameworks in modern cybersecurity analysis.
❓ FAQs about Desert Rat 2026 Android Malware
❓ What is Desert Rat 2026 in cybersecurity?
📌 Desert Rat 2026 is a modular Android Remote Access Trojan (RAT) designed to compromise mobile devices by combining infection, surveillance, and remote control capabilities. It operates as a multi-stage malware framework that can silently access files, messages, and system functions without user awareness. It is studied in cybersecurity research as a high-risk mobile threat model.
❓ How does Desert Rat 2026 infect Android devices?
📌 It typically infects devices through disguised APK files that appear as legitimate applications. Once installed, the malware activates hidden services in the background. These services connect to remote servers and begin data collection. Infection often relies on social engineering techniques such as fake updates or cloned applications.
❓ Why is Desert Rat 2026 considered dangerous?
📌 It is dangerous because it combines multiple attack capabilities in a single framework. It can steal credentials, monitor user activity, track location, record screen data, and execute remote commands. Its modular structure allows attackers to control nearly every function of an infected device, making full compromise possible.
❓ Can Desert Rat 2026 be detected by antivirus software?
📌 Detection depends on the variant and obfuscation level. Advanced versions use encryption, code obfuscation, and anti-analysis techniques to avoid detection. However, modern mobile security tools and behavioral monitoring systems can still identify suspicious activity such as unauthorized accessibility access or background data exfiltration.
❓ What is the role of the Builder system in Desert Rat 2026?
📌 The Builder system acts as the central control panel for attackers. It allows configuration of malware settings, monitoring of infected devices, and generation of custom malicious APKs. It essentially functions as the command-and-control interface that manages all infected endpoints.
❓ How does Desert Rat 2026 steal data from devices?
📌 It uses multiple methods including keylogging, screen capture, accessibility service abuse, notification monitoring, and file extraction. It can also intercept SMS messages, call logs, and stored credentials. All collected data is sent back to attacker-controlled servers in real time.
❓ Can users protect themselves from Desert Rat 2026?
📌 Yes, users can reduce risk by avoiding third-party APK installations, disabling unknown app sources, reviewing app permissions carefully, and keeping Google Play Protect enabled. Using trusted mobile security software and avoiding suspicious links or downloads also significantly improves protection.
❓ Is Desert Rat 2026 a real-world threat or theoretical malware?
📌 It is based on real-world RAT architecture concepts commonly seen in Android malware ecosystems. While specific variants may differ, the described structure reflects techniques used in active cybercrime tools and mobile spyware frameworks.