🛡️ CyberGate v3.4.2.2: A Look at a Historic Remote Access Trojan
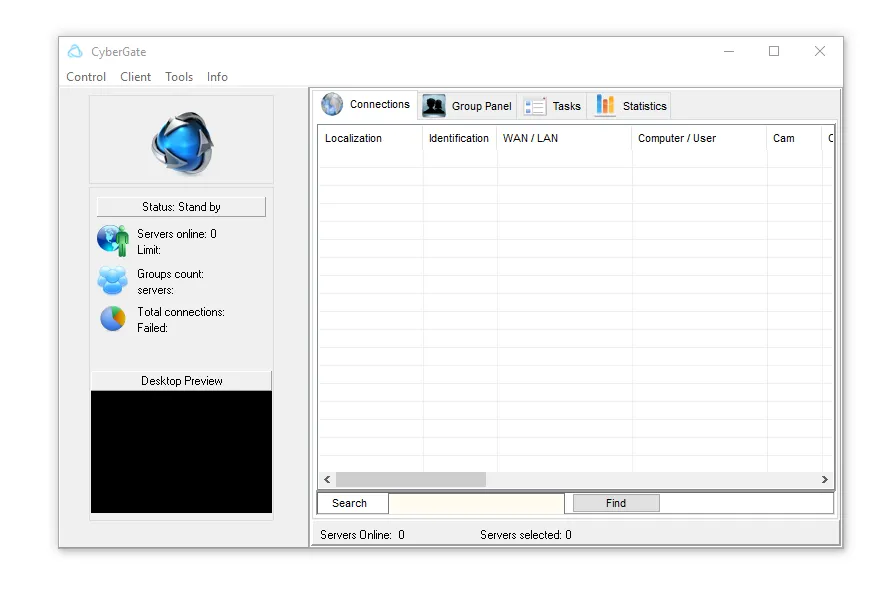
CyberGate v3.4.2.2 became one of the most recognized Remote Access Trojans (RATs) during the early era of modern cybercrime operations. The malware gained attention in underground communities because of its powerful remote control functions, user-friendly interface, and extensive spying capabilities targeting Microsoft Windows systems.
At the time, many cybersecurity researchers classified CyberGate as a dangerous Windows RAT malware due to its ability to silently control infected computers from remote locations. The software was widely discussed across cybersecurity forums because it combined credential theft, surveillance tools, and remote administration features inside a single malware framework.
CyberGate also represented a turning point in malware development because it allowed inexperienced attackers to use advanced cyber intrusion techniques without requiring deep programming knowledge. This accessibility helped expand the spread of RAT malware worldwide and influenced many later cyber threats seen across Europe and the United States.
🔍 What Was CyberGate v3.4.2.2?
CyberGate was categorized as a Remote Access Trojan, commonly known as a RAT. This type of malware allows attackers to remotely interact with an infected computer while remaining hidden from the victim. Once installed, the malware could provide full administrative access to the attacker through a remote control panel.
The main objective of CyberGate was to provide stealth-based remote control capabilities over Windows operating systems. It became particularly dangerous because it combined multiple cyberattack features into one centralized platform.
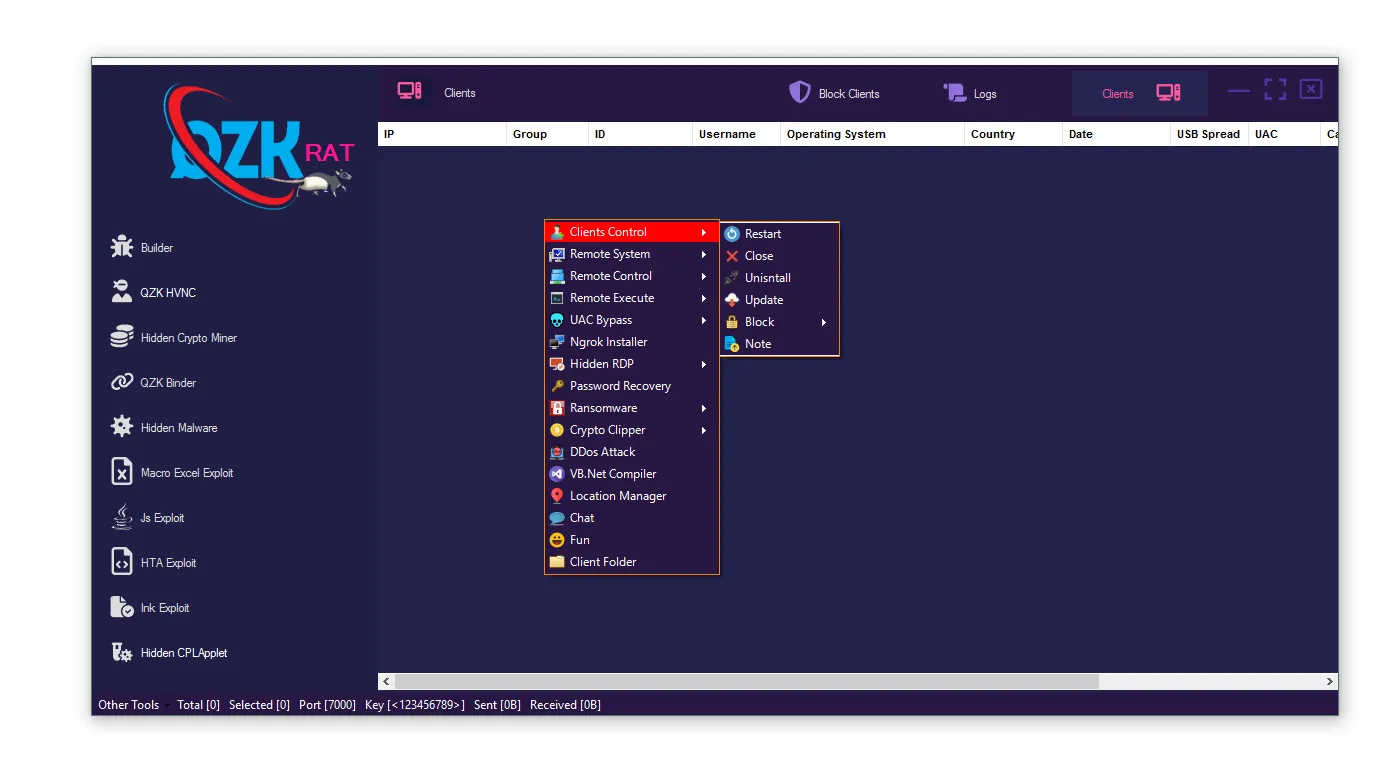
⚙️ Core Functions of CyberGate v3.4.2.2
- 🖥️ Remote Desktop Viewing:
CyberGate allowed attackers to remotely observe a victim’s desktop activity in real time. This feature enabled cybercriminals to monitor browsing habits, private conversations, and confidential work activities without physical access to the system. - 📂 File Management:
The malware included remote file browsing and management tools that allowed attackers to upload, download, rename, or delete files. This capability increased the risk of sensitive data theft and unauthorized data manipulation. - 🎥 Webcam and Microphone Access:
CyberGate could activate connected webcams and microphones remotely. This surveillance functionality raised major privacy concerns because attackers could secretly monitor users inside homes, offices, or workplaces. - ⌨️ Keylogging:
The built-in keylogger recorded keyboard activity, including usernames, passwords, emails, and financial information. This feature made CyberGate highly dangerous for banking security and online account protection. - 🔑 Password Theft:
CyberGate targeted stored credentials inside browsers and applications. Saved login sessions, browser passwords, and authentication information could potentially be extracted from infected systems. - ⚙️ Process and Service Management:
Attackers could start, stop, or monitor running system processes and Windows services remotely. This helped maintain malware persistence and allowed attackers to disable certain security applications. - 🗂️ Registry Editing:
The malware included remote Windows Registry access, enabling attackers to modify startup settings and system configurations. This increased long-term persistence inside compromised systems. - 💻 Remote Shell Execution:
CyberGate supported remote command execution using Windows command-line functionality. Attackers could perform administrative tasks or deploy additional malicious payloads through this feature. - 🔒 Persistence Mechanisms:
The RAT attempted to remain active after system restarts by modifying startup entries and system settings. Persistence features helped attackers maintain continuous remote access over long periods.
🚨 Common Distribution Methods
CyberGate v3.4.2.2 spread through several common malware delivery techniques that were widely used during its peak popularity.
- 📧 Malicious Email Attachments:
Attackers often distributed infected files through phishing emails disguised as invoices, documents, or software updates. Once opened, the malware silently installed itself on the victim’s computer. - 💿 Cracked Software Downloads:
Pirated applications and unofficial software installers became one of the largest infection sources. Users searching for free premium software were frequently exposed to infected executables. - 🌐 Fake Software Installers:
Cybercriminals created fake applications or misleading download pages that secretly installed CyberGate in the background during the setup process. - ⚠️ Social Engineering Campaigns:
Attackers manipulated users into trusting malicious files by using fake alerts, misleading advertisements, or urgent security warnings designed to trigger user interaction.
⭐ Why CyberGate v3.4.2.2 Became Popular
CyberGate became extremely popular within underground cybercrime communities because it combined simplicity, stealth, and advanced malware functions inside a single platform.
🎛️ 1. Easy-to-Use Interface
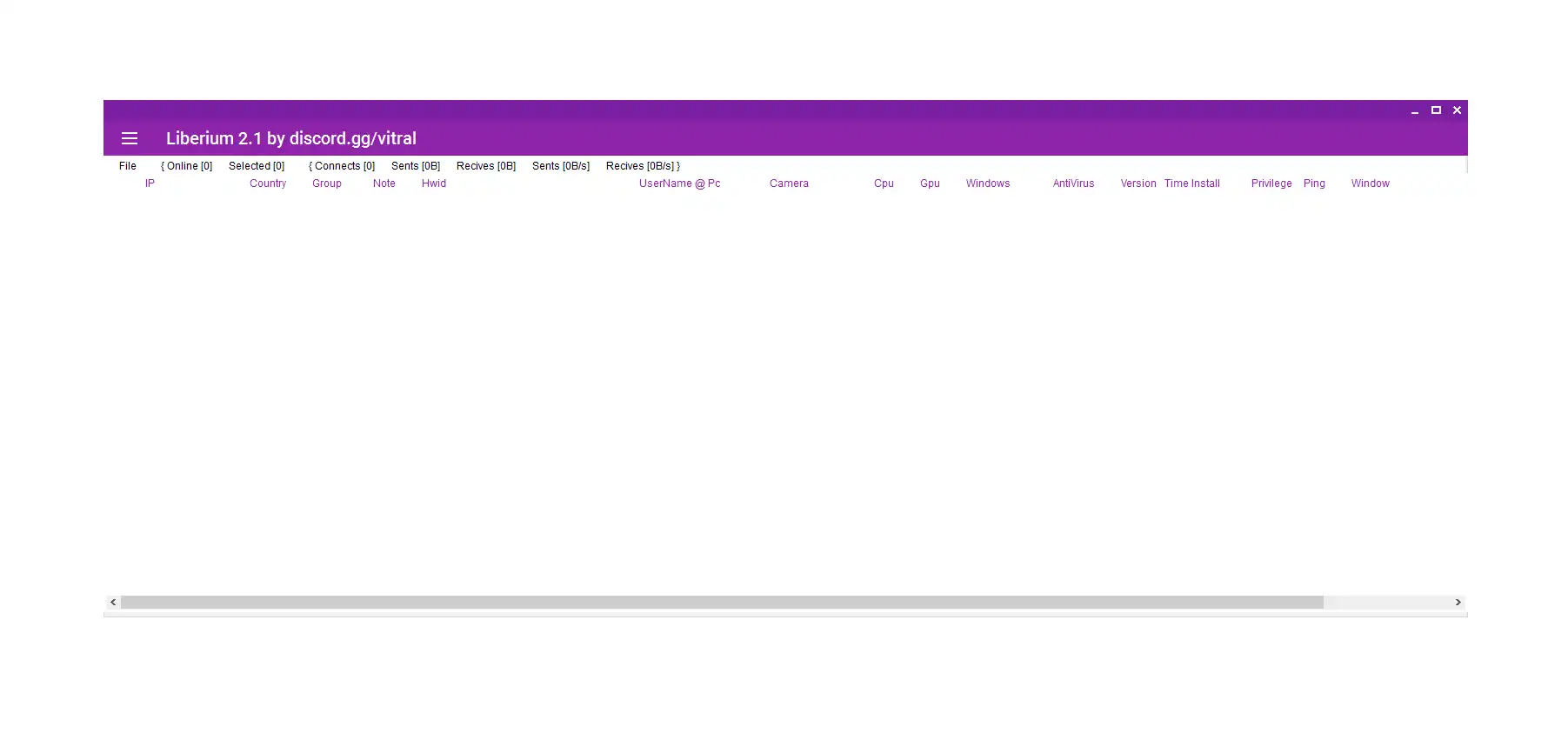
One of CyberGate’s biggest advantages was its graphical user interface. Even inexperienced users could control infected systems through a dashboard that simplified complex remote administration tasks.
The visual management panel allowed attackers to organize victims, monitor system activity, and execute commands without requiring advanced technical skills. This accessibility increased the malware’s adoption rate significantly.
🛠️ 2. Builder Functionality
CyberGate included a customizable builder system that allowed attackers to create modified malware payloads according to their operational needs.
- ⚙️ Connection Settings:
Attackers could configure network communication settings that connected infected systems to remote control servers. These settings helped maintain stable communication channels between victims and operators. - 🖥️ Startup Persistence:
The builder allowed malware operators to configure automatic startup behavior. This ensured the malware remained active after system reboots and increased long-term control capabilities. - 🕵️ Obfuscation Methods:
Certain versions attempted to hide malicious activity through obfuscation techniques designed to reduce detection by antivirus software and security scanners. - 🧩 Anti-Analysis Options:
Some builds included mechanisms that attempted to avoid detection inside virtual machines or analysis environments commonly used by cybersecurity researchers.
🔥 3. Wide Feature Set
CyberGate v3.4.2.2 combined surveillance tools, credential theft functions, and remote administration capabilities into a single malware package. This all-in-one structure made it attractive for cybercriminal operations targeting individuals and businesses.
The malware supported multiple attack scenarios, including espionage, account theft, privacy invasion, and unauthorized system control.
📈 4. Cracked Versions
Unauthorized copies of CyberGate circulated heavily across underground forums and malware-sharing communities. The widespread availability of cracked versions significantly increased its global distribution.
This uncontrolled spread contributed to its reputation as one of the most recognized RAT malware families during its era.
⚠️ Security Risks and Impact
CyberGate v3.4.2.2 infections created serious cybersecurity risks for both personal users and organizations.
🔑 Credential Theft
The malware targeted login credentials stored in browsers and applications. Stolen passwords could potentially provide attackers access to email accounts, financial services, social media platforms, and business systems.
💰 Financial Loss
CyberGate v3.4.2.2-related credential theft increased the risk of banking fraud and unauthorized transactions. Financial information collected from infected systems could be abused for cybercrime activities.
🎥 Privacy Violations
Remote webcam and microphone access allowed attackers to secretly monitor victims in real-world environments. This created severe privacy and surveillance concerns.
📂 Data Exfiltration
Attackers could remotely transfer sensitive files from compromised computers. Personal documents, business records, and confidential information became vulnerable to theft.
🌐 Botnet Participation
Infected systems could become part of larger malicious networks controlled remotely by attackers. These networks were sometimes used for coordinated cybercrime campaigns.
🧪 Technical Characteristics
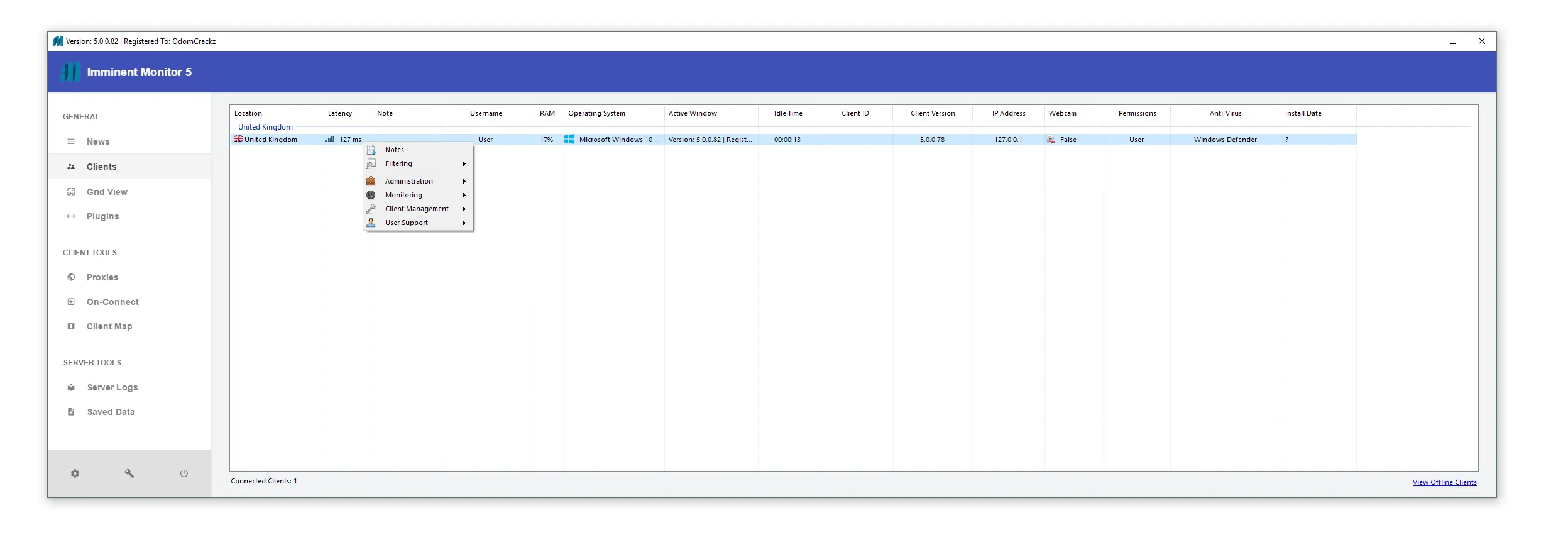
CyberGate v3.4.2.2 mainly targeted Microsoft Windows operating systems and operated using a client-server architecture model.
🖥️ Server Component
The server-side payload was installed on victim systems and operated silently in the background. This component handled communication with the remote attacker while collecting system information.
💻 Client Control Panel
Attackers used a graphical control interface to manage infected systems remotely. The dashboard simplified monitoring, command execution, and victim management.
🛡️ Antivirus Evasion Techniques
Certain CyberGate v3.4.2.2 variants attempted to bypass security detection mechanisms.
- 🔄 Packers:
Executable packers compressed or modified malware files to make signature detection more difficult for antivirus engines. - 🕵️ Obfuscation:
Code obfuscation techniques attempted to hide malicious instructions and confuse malware analysis tools. - ⚙️ Process Injection:
Some variants injected malicious code into legitimate Windows processes to avoid detection and blend with normal system activity. - 🔒 Startup Persistence:
The malware attempted to survive system restarts through registry entries and startup folder modifications.
🛡️ Detection and Defense
Although CyberGate v3.4.2.2 is considered an older malware family today, many of its techniques still appear in modern cyber threats. Strong cybersecurity practices remain essential for protection.
🔄 Keep Windows Updated
Regular Windows updates help patch security vulnerabilities that malware may attempt to exploit. Updated operating systems reduce exposure to known attack vectors.
🛡️ Use Reputable Antivirus Software
Modern security solutions can detect many older RAT malware signatures and suspicious behaviors associated with remote access trojans.
🚫 Avoid Cracked Software Downloads
Pirated applications remain one of the most common malware infection sources worldwide. Downloading software from official sources greatly reduces infection risks.
📧 Be Careful With Email Attachments
Users should avoid opening suspicious email attachments or clicking unknown download links. Phishing remains a major malware distribution method.
🔐 Enable Multi-Factor Authentication
Multi-factor authentication adds an additional security layer for online accounts. Even if passwords are stolen, MFA can help prevent unauthorized access.
📡 Monitor Network Activity
Organizations often monitor unusual outbound network traffic to identify suspicious communications between infected systems and remote command servers.
📚 Historical Importance
CyberGate v3.4.2.2 remains historically important in cybersecurity research because it demonstrated how advanced malware capabilities became increasingly accessible to inexperienced cybercriminals.
The malware influenced later RAT families and contributed to the evolution of modern cybercrime ecosystems. Researchers frequently study CyberGate to better understand the development of remote administration malware and attacker behavior patterns.
Today, CyberGate mainly appears in:
- Cybersecurity education
- Malware research archives
- Threat intelligence studies
- Digital forensics investigations
- Historic malware analysis reports
Its legacy continues to shape modern malware detection and defensive security strategies used throughout Europe and North America.
Download CyberGate v3.4.2.2
Download Link 2
Download Link 3
Virus Total Report
https://www.virustotal.com/gui/file/1713dc00a8573685838379ce680f6ee1ffbb4a3231ccc0ad4cf45fd9f3b3f837✅ Conclusion
CyberGate v3.4.2.2 became one of the most recognized Remote Access Trojans in the history of Windows malware. Its combination of remote administration tools, credential theft capabilities, surveillance functions, and easy-to-use design helped it spread rapidly across underground cybercrime communities.
Although the malware is now considered outdated compared to modern cyber threats, its influence on the evolution of RAT malware remains significant. Many of the techniques introduced or popularized by CyberGate later appeared in newer malware families targeting businesses and individual users worldwide.
Understanding historic malware families like CyberGate helps cybersecurity professionals, researchers, and everyday users recognize how cyber threats evolve over time. Continuous security awareness, safe browsing habits, and modern endpoint protection remain essential defenses against both historic and modern remote access trojans.
❓ FAQs About CyberGate v3.4.2.2
❓ What is CyberGate v3.4.2.2?
CyberGate v3.4.2.2 is a historic Windows-based Remote Access Trojan (RAT) that allowed attackers to remotely control infected systems using a graphical administration panel.
❓ Was CyberGate considered dangerous?
Yes. CyberGate v3.4.2.2 included surveillance tools, password theft capabilities, keylogging functions, and remote administration features that created serious privacy and cybersecurity risks.
❓ Which operating systems did CCyberGate v3.4.2.2 target?
CyberGate mainly targeted Microsoft Windows operating systems and was designed specifically for Windows-based environments.
❓ How did CyberGate usually spread?
The malware commonly spread through phishing emails, fake software installers, malicious downloads, cracked software packages, and social engineering attacks.
❓ Can modern antivirus software detect CyberGate?
Most modern antivirus and endpoint security solutions can detect known CyberGate variants because the malware family is relatively old compared to current threats.
❓ Why is CyberGate important in cybersecurity history?
CyberGate played an important role in the evolution of Remote Access Trojans by combining advanced spying and remote control features into an easy-to-use platform accessible to inexperienced attackers.
❓ What lessons can modern users learn from CyberGate?
CyberGate demonstrates the importance of:
- Downloading software only from trusted sources
- Using strong passwords
- Enabling multi-factor authentication
- Keeping operating systems updated
- Practicing safe email and browsing habits
These security measures remain critical against modern malware threats today.