🛑 Imminent Monitor 5 RAT: A Deep Dive into Its Admin, Monitoring & Support Features
In today’s digital landscape, cybersecurity threats are evolving rapidly, and one of the most invasive threats is the Remote Access Trojan (RAT). Among these, Imminent Monitor 5 RAT stands out due to its powerful surveillance and control capabilities.
Although it is often disguised as a legitimate administrative tool, its real-world use cases reveal something far more dangerous: unauthorized access, spying, and full system exploitation.
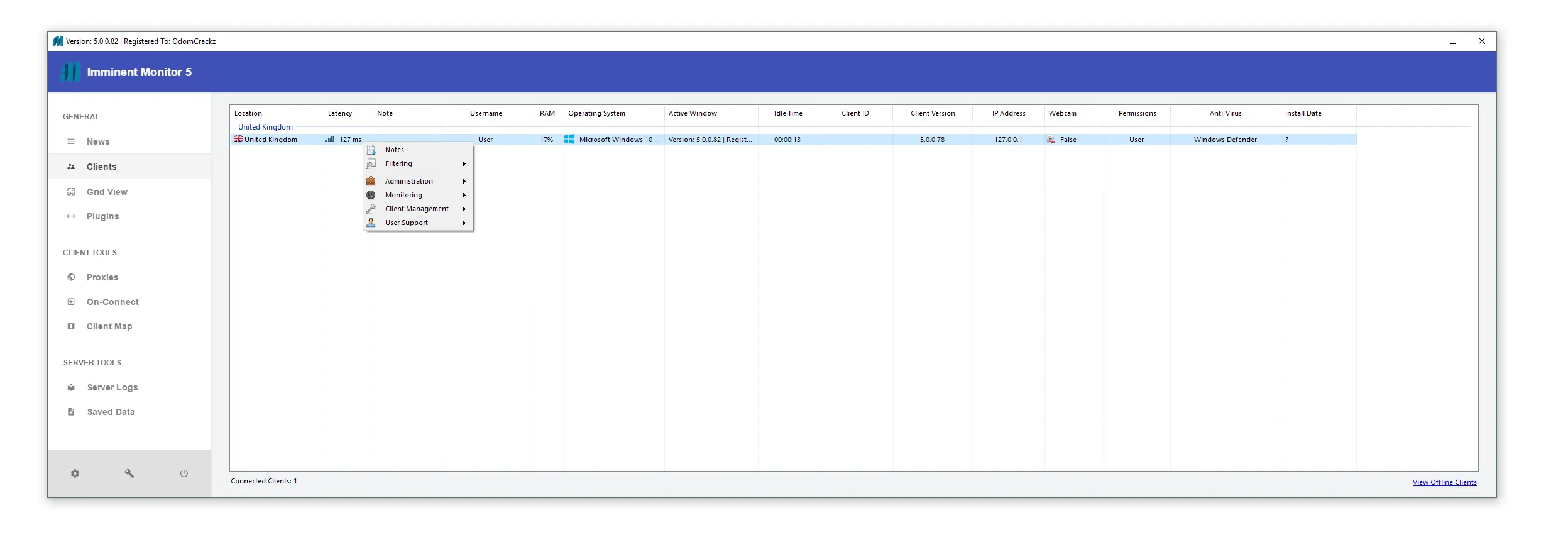
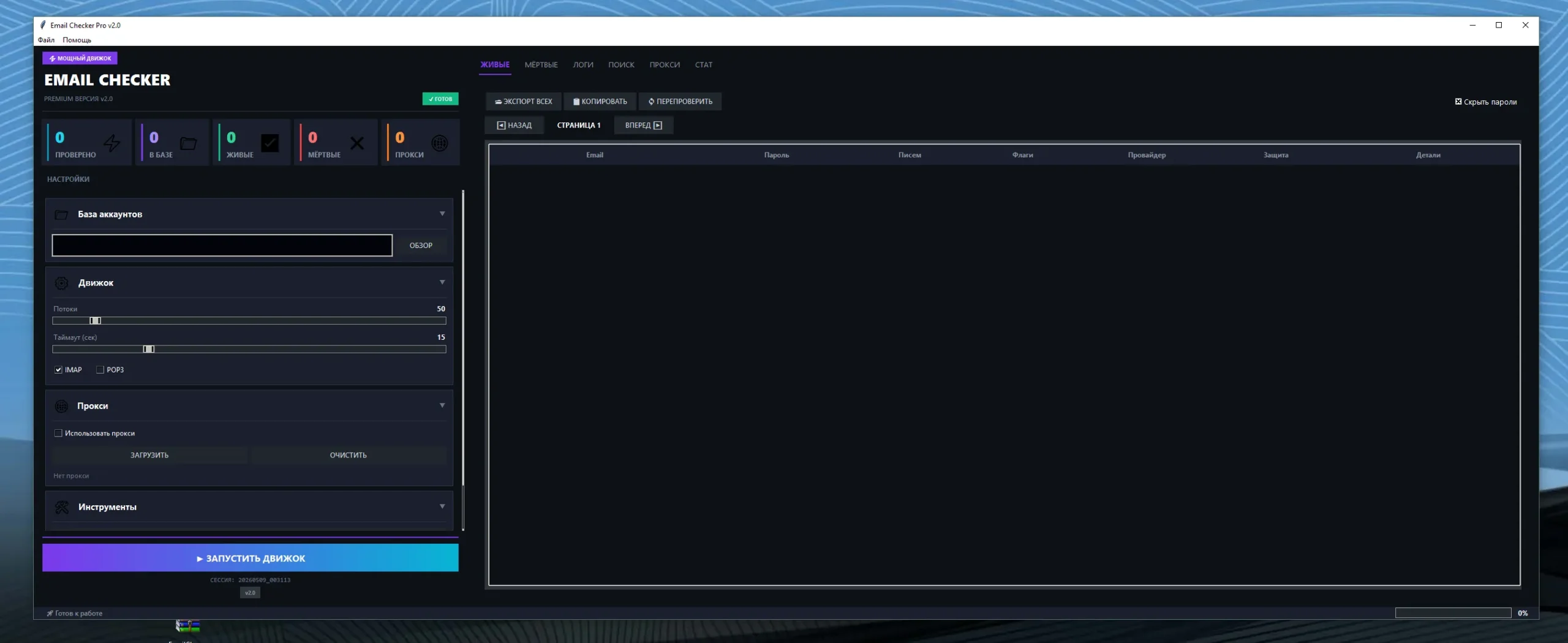
🧭 1. Administration Panel of Imminent Monitor 5 RAT
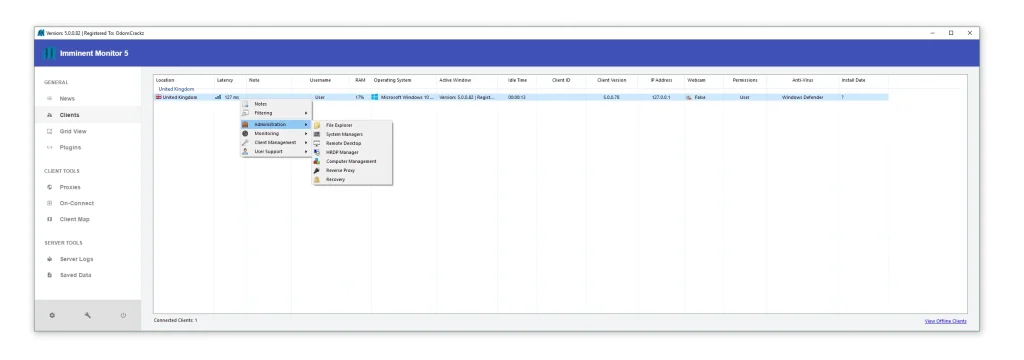
⚙️ The Attacker’s Command Center
- 🔍 Real-Time Victim Metrics:
This feature provides attackers with a live dashboard displaying critical system information of infected machines. It includes geolocation data, network latency, RAM usage, and operating system details. Such insights allow attackers to evaluate the quality and stability of the connection before executing further actions. Additionally, tracking system performance helps them avoid detection by not overloading the victim’s device. This level of visibility essentially turns each infected system into a monitored endpoint, enabling efficient large-scale operations. Attackers can prioritize targets based on system responsiveness and activity levels, making this feature crucial for maintaining control over multiple victims simultaneously. - 🛡️ Security Evasion Monitoring:
The administration panel also identifies the antivirus software installed on the victim’s machine, such as Windows Defender. This allows attackers to test whether their malware is being detected or flagged. By analyzing this information, they can modify their attack strategies, deploy updated payloads, or disable security features remotely. This adaptive capability makes the malware more resilient against detection and removal. Over time, attackers can refine their techniques based on which systems remain undetected, increasing the overall success rate of their campaigns. - 📊 Server Logs & Data Storage:
This section records every action performed by the attacker, including commands executed and data extracted. It also stores stolen information such as credentials, files, and browsing data. These logs act as a centralized record, allowing attackers to revisit past activities and extract additional value from compromised systems. Data storage ensures that even if the victim cleans their system later, the stolen information remains stored for misuse. This feature transforms the RAT into a long-term surveillance and data harvesting tool.
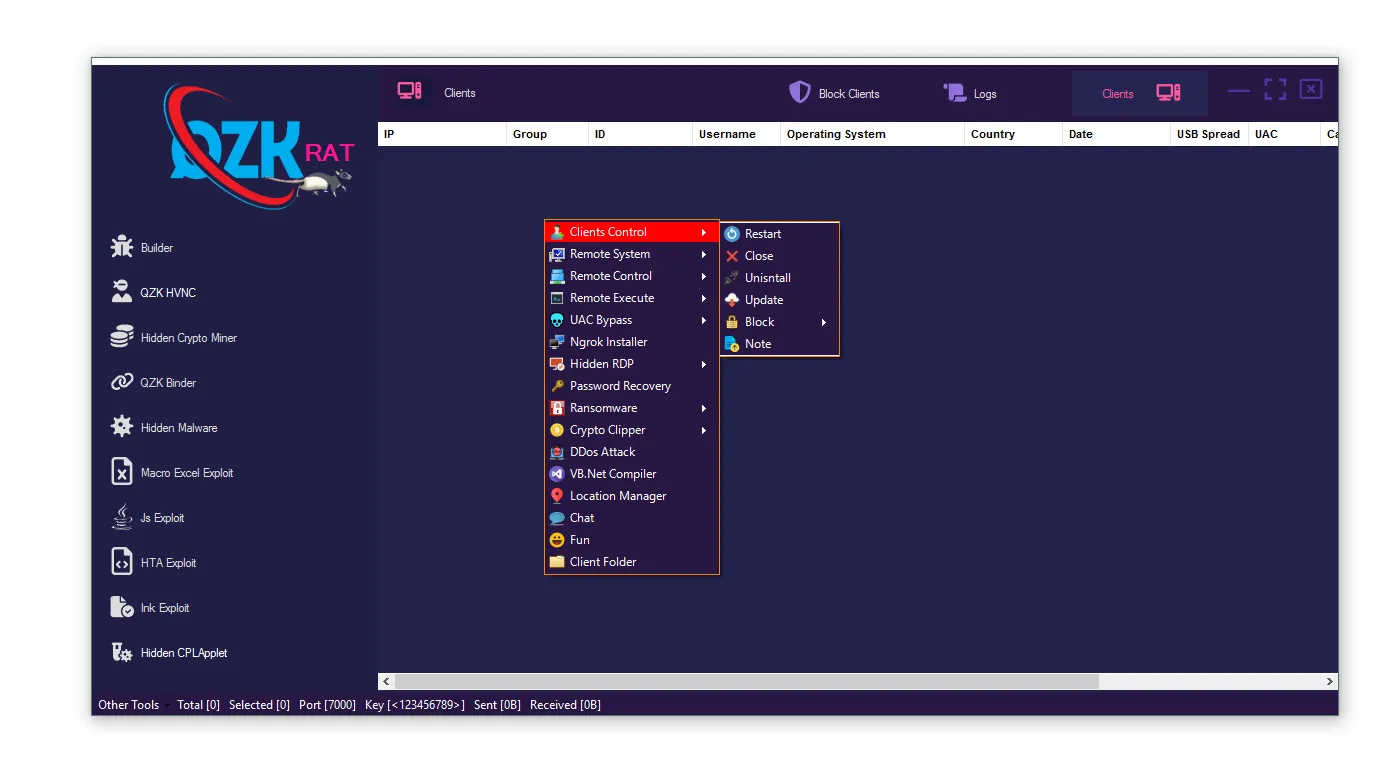
👤 2. Client Management in Imminent Monitor 5 RAT
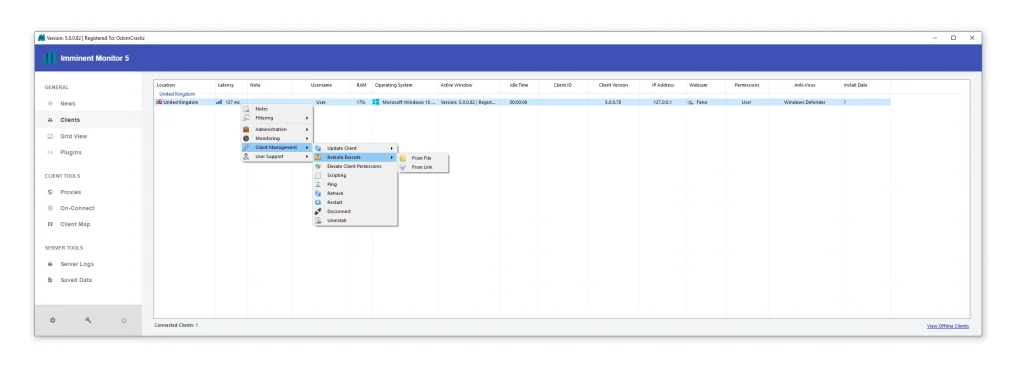
🎯 Granular Control Over Individual Victims
- 📝 Victim Notes & Profiling:
Attackers can attach custom notes to each infected system, effectively creating a profile for every victim. These notes may include sensitive observations such as financial status, presence of cryptocurrency wallets, or personal habits. This allows attackers to categorize victims based on potential value and tailor their attacks accordingly. Over time, this profiling becomes more detailed, enabling highly targeted exploitation strategies. It shifts the attack model from random infection to calculated targeting, increasing profitability and efficiency. - 🧾 System Privileges & Access Levels:
The panel displays whether the victim has administrative privileges or limited user access. This information is critical because administrative access allows deeper system control, including installing additional malware or modifying system settings. If the victim has limited access, attackers may attempt privilege escalation techniques. Understanding permission levels helps attackers decide the next steps in their attack chain, making this feature essential for strategic planning. - 📅 Install Tracking & Version Control:
Details such as installation date, client ID, and software version help attackers monitor how long a system has been infected. This information is used to determine the stability of the infection and whether updates are required. Older infections may need refreshed payloads to remain undetected. Version tracking also ensures compatibility between the attacker’s control panel and the infected client. This systematic approach allows attackers to maintain long-term persistence on victim machines.
🔎 3. Filtering
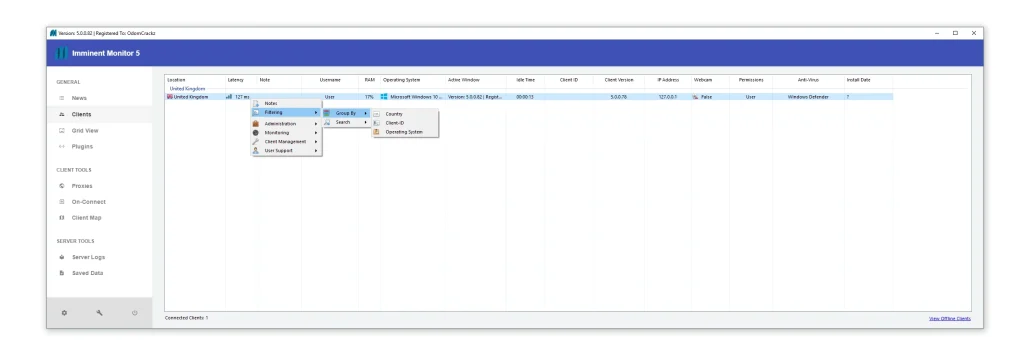
🧠 Smart Target Selection System
- 🎥 Webcam Availability Filtering:
Attackers can filter systems based on whether a webcam is present and active. This is particularly dangerous because it enables crimes like extortion and privacy invasion. Systems with webcams are often prioritized for surveillance and blackmail schemes. By narrowing down targets with this feature, attackers can focus on victims who are more vulnerable to psychological manipulation. This transforms the RAT into a tool for highly invasive cybercrimes. - 🌍 Location & System-Based Filtering:
Filtering by country, operating system, or language allows attackers to target specific regions such as the United States or Europe. This is often done to align with financial goals or avoid legal risks in certain jurisdictions. For example, attackers may prefer targets in high-income regions. This geographic targeting increases the chances of financial gain and reduces operational inefficiencies. - 🧩 Antivirus-Based Filtering:
Attackers can identify systems with weak or no antivirus protection. These systems are considered low-risk targets because they are less likely to detect or remove the malware. By focusing on such devices, attackers maximize their success rate while minimizing effort. This feature highlights the importance of strong endpoint security in preventing infections.
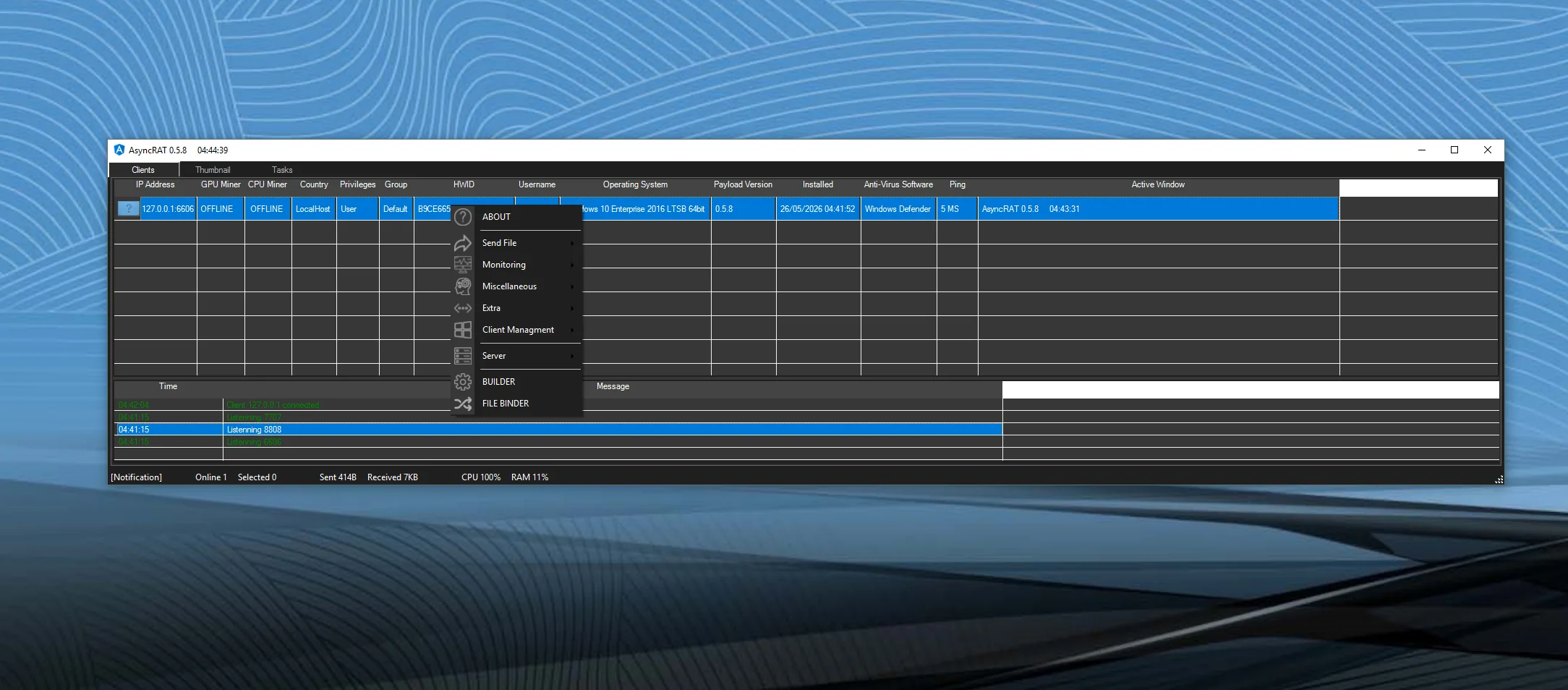
📡 4. Monitoring
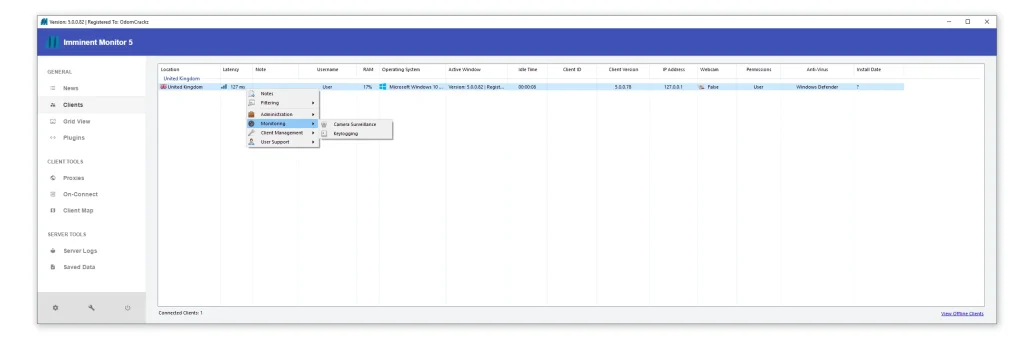
👁️ Real-Time Surveillance Mode
- 🖥️ Active Window Tracking:
This feature allows attackers to see exactly what application or document the victim is using in real time. It can capture sensitive activities such as online banking, email access, or document editing. By monitoring active windows, attackers can intercept valuable information without needing direct file access. This makes it one of the most powerful surveillance tools within the RAT. - ⏱️ Idle Time Detection:
Idle time tracking shows how long the user has been inactive. This helps attackers determine the best time to execute actions without being noticed. For example, they may deploy additional malware or access files when the user is away. This strategic timing reduces the risk of detection and increases operational success. - ⌨️ Behavioral Monitoring & Data Capture:
Although not always visible, monitoring typically includes keylogging and screen recording. These capabilities allow attackers to capture passwords, messages, and other sensitive data. Combined with other features, this creates a comprehensive surveillance system that compromises both privacy and security.
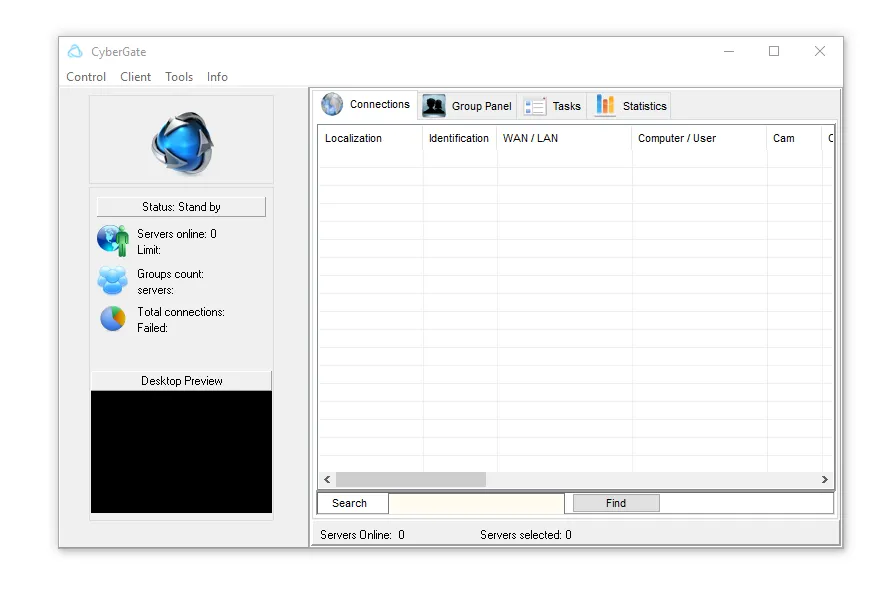
🎧 5. User Support
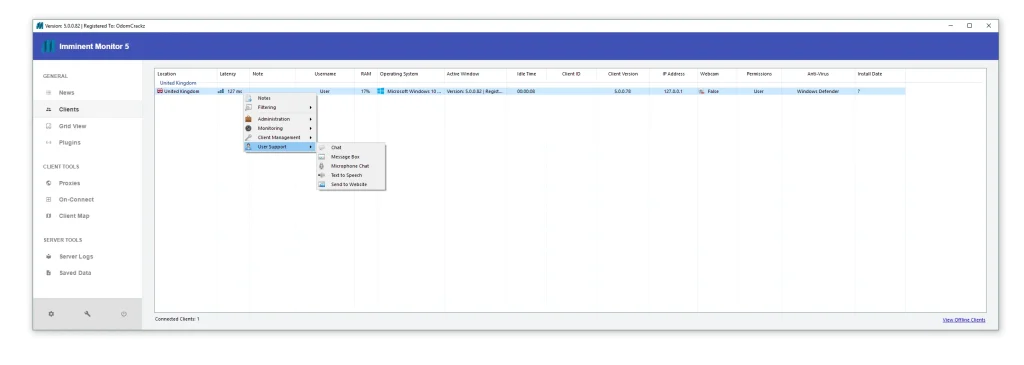
🎭 Social Engineering & Scam Tools
- 💬 Fake Messaging System:
Attackers can send pop-up messages directly to the victim’s screen, often posing as technical support. These messages are designed to create panic and urgency, convincing users to take immediate action. This psychological manipulation is a key component of many scams. - 🔊 Text-to-Speech Manipulation:
The RAT can generate voice messages through the victim’s system, making warnings sound more realistic. Hearing a computer speak can create fear and confusion, increasing the likelihood of compliance. This adds another layer of deception to the attack. - 🎙️ Microphone Access & Interaction:
Attackers can listen to the victim’s environment through the microphone. This not only invades privacy but can also provide additional context for social engineering attacks. For example, attackers may gather personal information to make scams more convincing.
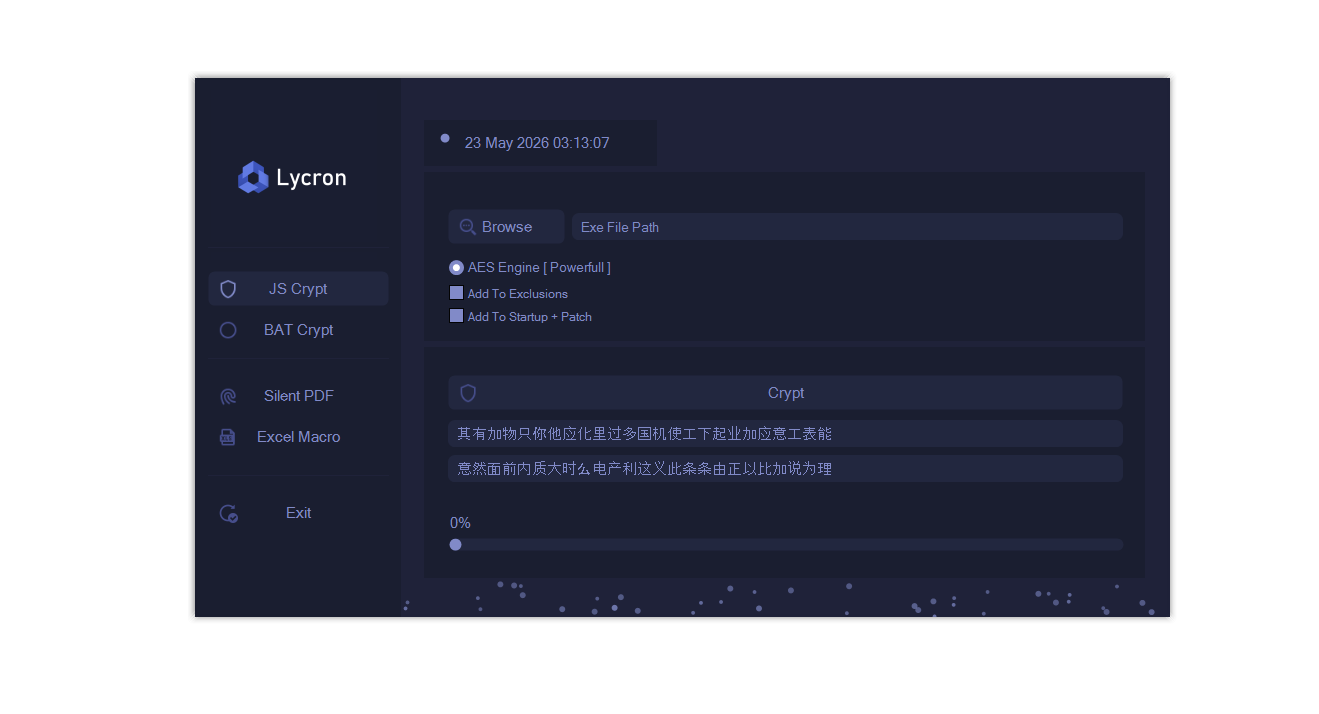
⚠️ 6. Feature Image
🧪 Data Interruption Handling
- 📉 Missing Data Indicators:
When the RAT cannot retrieve certain information, it displays “Not Found” fields. This may occur due to system restrictions, partial removal, or sandbox environments. These indicators help attackers understand the status of the infection. - 🔧 Infection Health Monitoring:
By analyzing missing or incomplete data, attackers can decide whether to repair, update, or abandon the infection. This ensures efficient resource management and maximizes operational effectiveness.
Download Imminent Monitor 5 RAT
Virus Total Imminent Monitor 5 RAT
https://www.virustotal.com/gui/file/f6724fb0cef0640c6f8044120bcbf30d17097699a6fabbb9979469b4d9fe4a47✅ Conclusion: Why This Analysis Matters
Imminent Monitor 5 RAT is not a legitimate tool—it is a high-risk cybersecurity threat designed for surveillance, exploitation, and financial gain.
Its features clearly demonstrate capabilities for:
- Unauthorized system control
- Data theft and identity fraud
- Real-time spying and monitoring
- Social engineering and scams
Understanding how this malware works is essential for protecting personal and organizational systems.
❓ FAQs about Imminent Monitor 5 RAT
❓ What is Imminent Monitor 5 RAT?
Imminent Monitor 5 RAT is a Remote Access Trojan that allows attackers to control and monitor infected computers without the user’s knowledge.
❓ Is Imminent Monitor 5 RAT legal software?
No, it is commonly associated with illegal activities such as hacking, spying, and data theft.
❓ How does Imminent Monitor 5 RAT infect systems?
It spreads through malicious downloads, phishing emails, fake updates, and cracked software.
❓ Can Imminent Monitor 5 RAT access webcams and microphones?
Yes, it can access both, enabling surveillance and potential privacy violations.
❓ How do I remove a Imminent Monitor 5 RAT from my computer?
You should disconnect from the internet, run a full antivirus scan, remove suspicious programs, and change all passwords from a secure device.
❓ Why is Imminent Monitor 5 RAT malware dangerous?
Because it provides attackers with full control over a system, allowing them to steal data, spy on users, and perform fraudulent activities.