CraxsRat V7.7 Cracked
In the ever-evolving landscape of cybersecurity, tools like CraxsRat V7.7 Cracked have become a focal point for both ethical researchers and malicious actors. As a sophisticated Remote Access Trojan (RAT) designed for Android devices, CraxsRat V7.7 Cracked offers extensive control features that can be leveraged for penetration testing—or unfortunately, for scams and fraud. If you’re exploring CraxsRat V7.7 features, risks, or detection methods, this comprehensive guide breaks it down. We’ll cover everything from its origins to practical tips for staying safe in 2025.
Whether you’re a cybersecurity professional conducting ethical hacking or a user concerned about mobile threats, understanding CraxsRat V7.7 is crucial. Let’s dive in.
What is CraxsRat V7.7 Cracked?
CraxsRat V7.7 is the latest iteration of the CraxsRat malware family, a Remote Access Trojan (RAT) primarily targeting Android operating systems. Evolving from earlier versions like V7.4 and V7.6, this tool grants attackers—or authorized testers—full remote control over infected devices.
Originally derived from Spymax RATs, CraxsRat has gained notoriety in underground forums and Telegram channels for its adaptability. The V7.7 update, spotted in mid-2025, amplifies stealth and functionality, making it a go-to for fake app scams and banking fraud campaigns. While marketed as a “remote administration tool” in some circles, its misuse in cybercrime underscores the fine line between legitimate security testing and illegal activities.
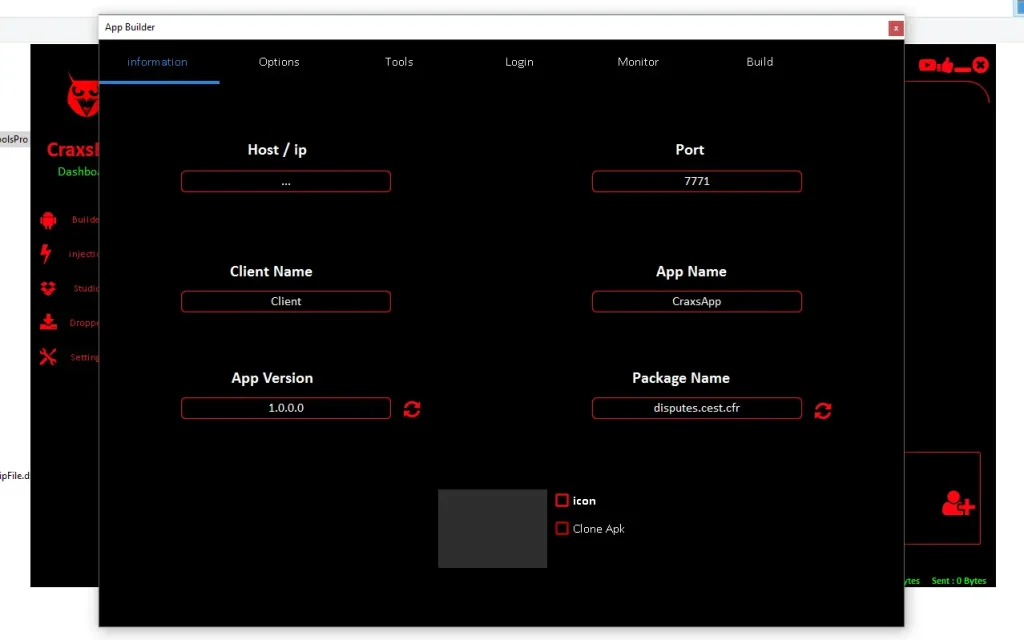
Key takeaway: CraxsRat V7.7 download sources are often found on dark web repositories or cracked versions on GitLab topics, but engaging with them poses severe legal and security risks.
Key Features of CraxsRat V7.7 Cracked
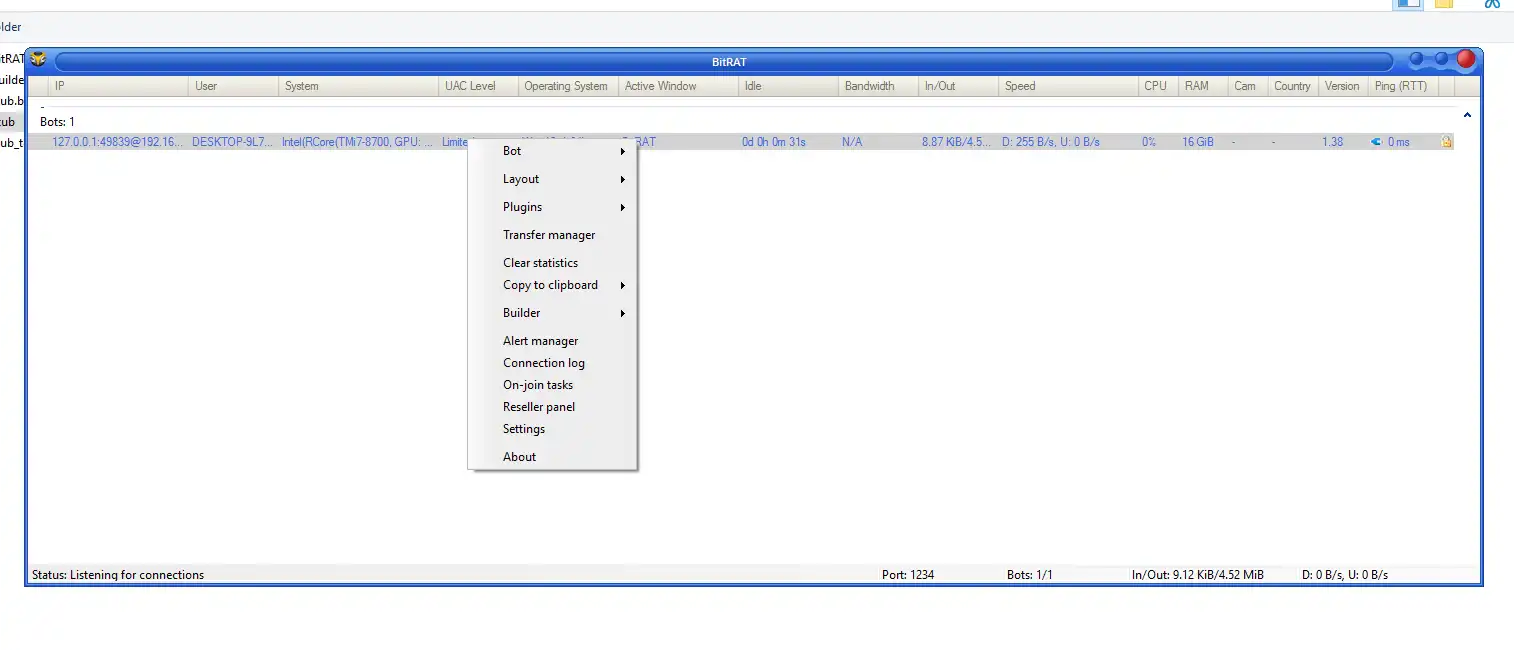
What sets CraxsRat V7.7 apart from its predecessors? This version introduces enhanced customization and evasion techniques, allowing builders to tailor payloads for specific attacks. Here’s a breakdown of its core capabilities:
1. Remote Device Control
- Full access to compromised Android devices, including navigation, app launching, and command execution.
- Supports dropper modules for stealthy installation, mimicking legitimate app updates.
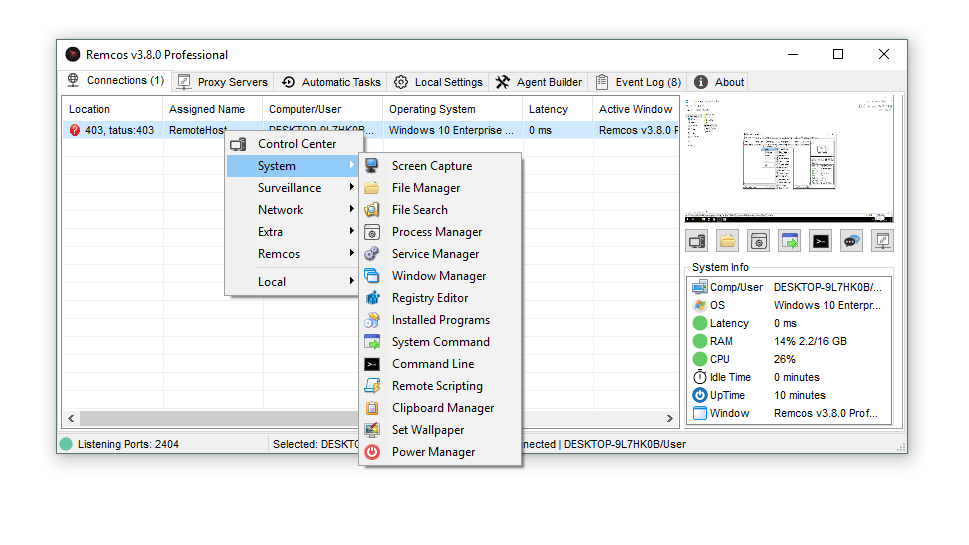
2. Surveillance and Data Theft
- Camera and Microphone Access: Live feeds for spying without user consent.
- Keylogging and Call Interception: Captures SMS, calls, and keystrokes for credential harvesting.
- File Management: Uploads, downloads, and deletes files remotely.
3. Stealth Operations
- Runs silently in the background, evading basic antivirus scans.
- Screenshot capture and location tracking for real-time monitoring.
- Customizable builders (free/paid) enable variants tailored for banking trojans or ad fraud.
4. Advanced Evasion Tactics
- Integration with Telegram channels for updates and command-and-control (C2) servers.
- Support for multi-language tutorials, including Chinese, boosting its global threat actor adoption.
These CraxsRat V7.7 features make it a powerful tool for ethical penetration testing when used legally, but its proliferation in 2025 has led to a spike in Android-targeted attacks.
| Feature | Description | Potential Risk Level |
|---|---|---|
| Remote Control | Full device navigation | High (Data Exfiltration) |
| Camera/Microphone | Live surveillance | Critical (Privacy Invasion) |
| Keylogging | Credential capture | High (Financial Fraud) |
| File Management | Data theft/deletion | Medium (Ransomware Tie-in) |
| Stealth Mode | Background operation | High (Detection Evasion) |
The Risks: How CraxsRat V7.7 Cracked Powers Cybercrime
CraxsRat V7.7 risks extend far beyond technical specs—it’s a linchpin in organized fraud. According to cybersecurity reports, threat actors use it to deploy fake apps that mimic banking or shopping platforms, leading to widespread scams.
In 2025, we’ve seen a surge in its use by Syrian and Chinese-linked groups, with Telegram channels like EVLF distributing cracked versions. Common attack vectors include:
- Phishing via Malicious APKs: Disguised as game mods or utility apps.
- Banking Fraud: Intercepts OTPs and session tokens for account takeovers.
- Ad Fraud and Spyware: Generates fake clicks or sells stolen data on underground markets.
The malware’s demand in forums highlights its profitability—operators charge for premium builders, fueling a cybercrime economy. For users, infection can result in identity theft, financial loss, or device bricking. Ethical hackers must obtain explicit permission to avoid legal repercussions.
How to Detect and Mitigate CraxsRat V7.7 Cracked
Spotting CraxsRat V7.7 detection early is key to protection. While its stealth is advanced, behavioral anomalies often give it away:
Detection Tips
- Unusual Battery Drain or Data Usage: RATs like this consume resources for C2 communication.
- Antivirus Scans: Tools like Malwarebytes or ESET flag RAT signatures; enable real-time protection.
- App Permissions Review: Watch for apps requesting excessive camera/mic access without reason.
- Network Monitoring: Tools like Wireshark can reveal suspicious outbound traffic to Telegram-linked servers.
Mitigation Strategies
- Update Android Regularly: Patch vulnerabilities that RATs exploit.
- Use Reputable App Stores: Avoid sideloading from untrusted sources.
- Enable Google Play Protect: It scans for malware like CraxsRat.
- Two-Factor Authentication (2FA): Adds a layer against intercepted credentials.
- For Enterprises: Deploy Mobile Device Management (MDM) solutions for endpoint monitoring.
If infected, perform a factory reset after backing up data—and report to authorities like the FBI’s IC3.
Ethical Uses and Legal Considerations
For white-hat hackers, CraxsRat V7.7 Cracked ethical use in controlled environments (e.g., bug bounties) can simulate real threats. Always secure written consent and comply with laws like the CFAA in the US. Resources like YouTube tutorials (e.g., on Infinity Hacks) demonstrate safe testing.
Conclusion: Stay Vigilant Against CraxsRat V7.7 Cracked Threats
CraxsRat V7.7 Cracked exemplifies the dual-edged sword of modern cybersecurity tools—innovative yet dangerous. By understanding its features, risks, and defenses, you can better safeguard your Android ecosystem. In a world where mobile threats evolve daily, proactive education is your best defense.
Have you encountered CraxsRat variants? Share your experiences in the comments below. For more on Android RATs 2025 and malware trends, subscribe to our newsletter.
This article is for educational purposes only. Unauthorized use of RATs is illegal. Consult legal experts for ethical hacking guidance.