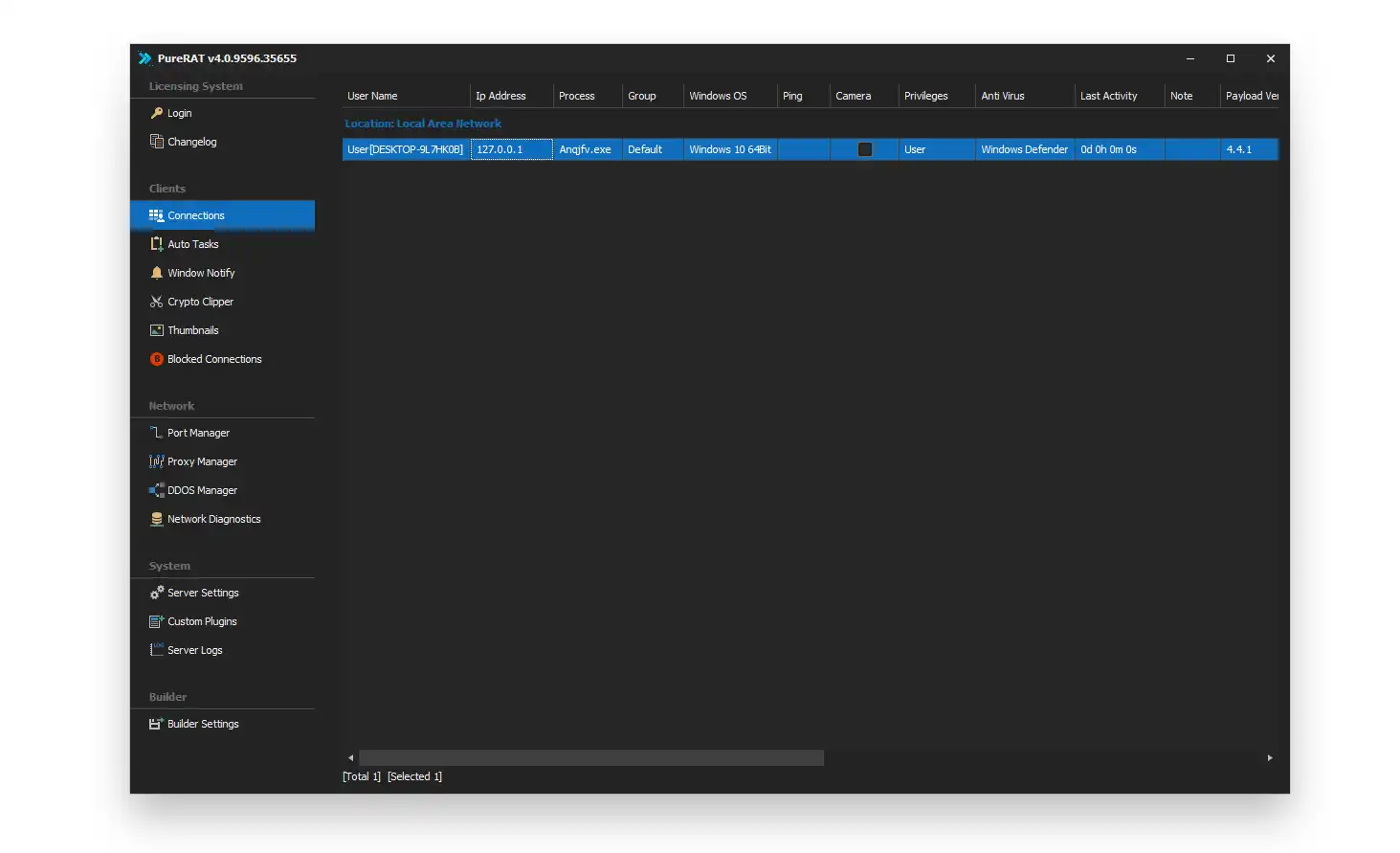
PureRAT 2026 Cracked
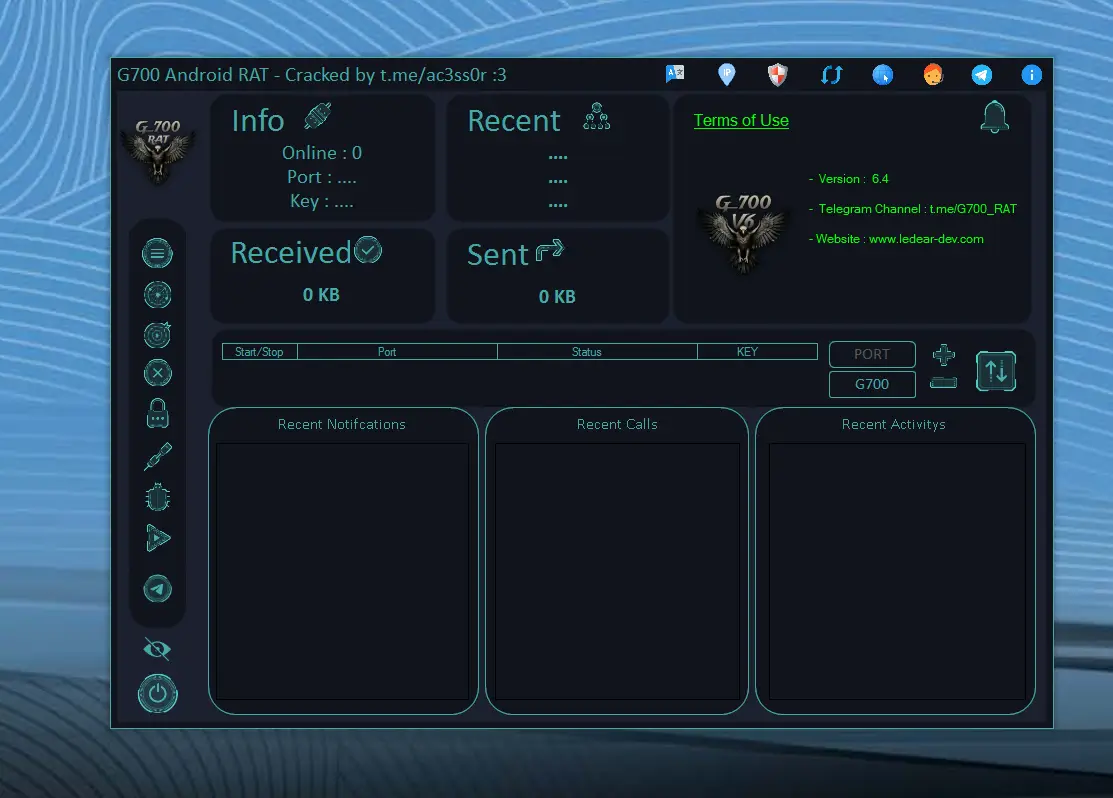
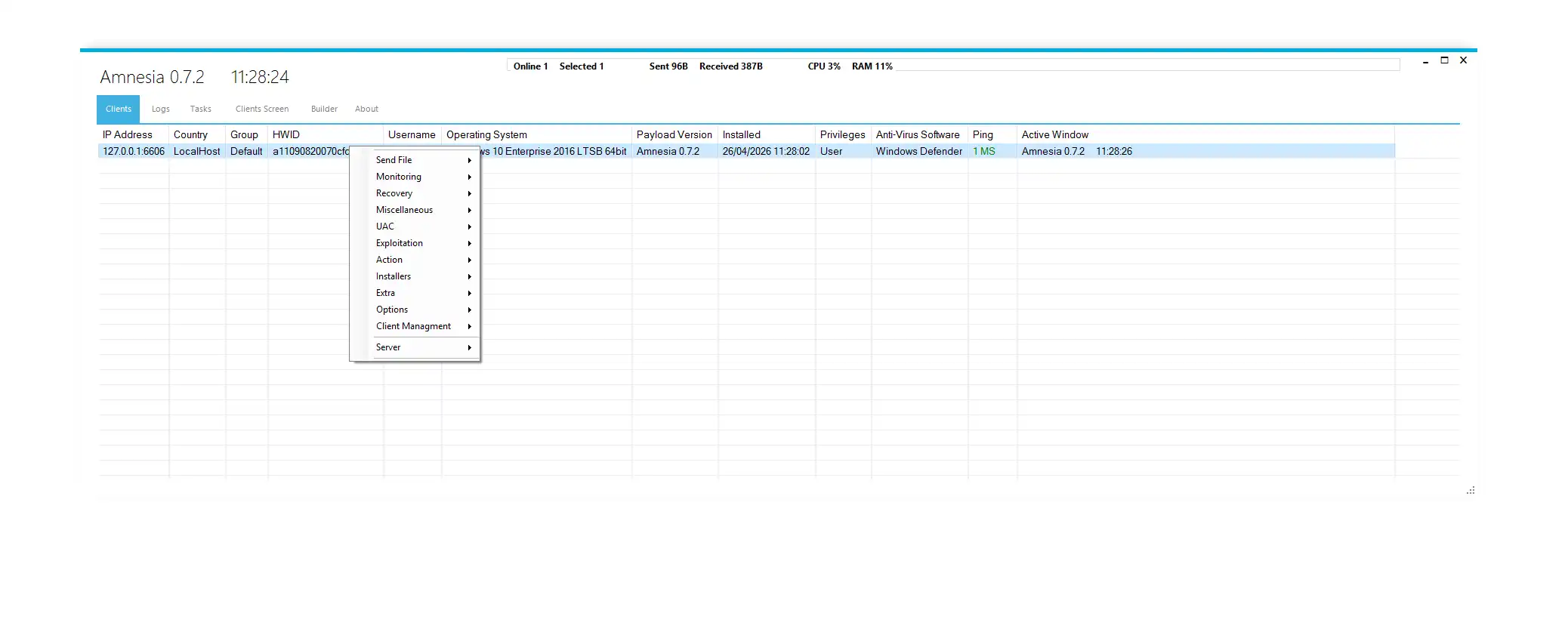
PureRAT 2026 Cracked is analyzed in cybersecurity research as a modular Remote Access Trojan (RAT) that integrates surveillance, persistence, botnet coordination, and remote system control into a unified architecture.
Unlike traditional malware, it operates as a multi-layer distributed control system, enabling long-term access, stealth execution, and system-wide manipulation across infected Windows environments.
This report provides a full breakdown of every module, feature, and subsystem from a defensive cybersecurity perspective.
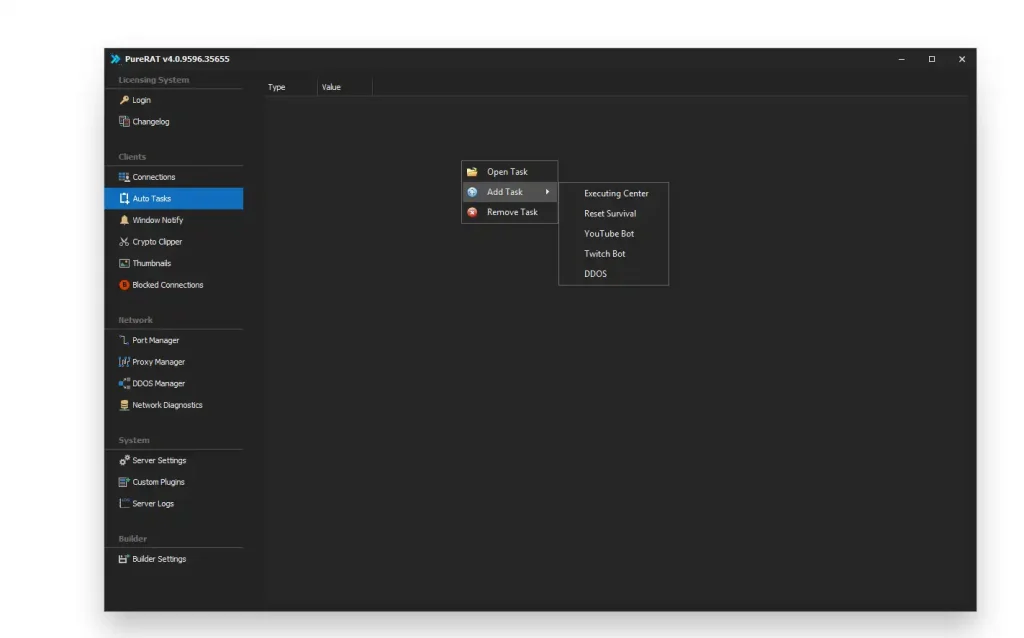
⚙️ auto task – Automated Task Execution System in PureRAT 2026 Cracked
The auto task module represents a core automation layer within the malware architecture. It is designed to execute predefined operations on infected systems without requiring continuous manual control from the operator. This system ensures that tasks can run periodically or based on triggers defined in the malware configuration. It supports long-term persistence by continuously repeating operations even after system reboot or interruption. From a cybersecurity standpoint, this reflects a time-based automation mechanism often seen in advanced threats. It also allows background execution of surveillance and system modification activities. This reduces dependency on active command sessions. It increases operational stability of the malware framework. It is a key indicator of structured automation in malicious systems.
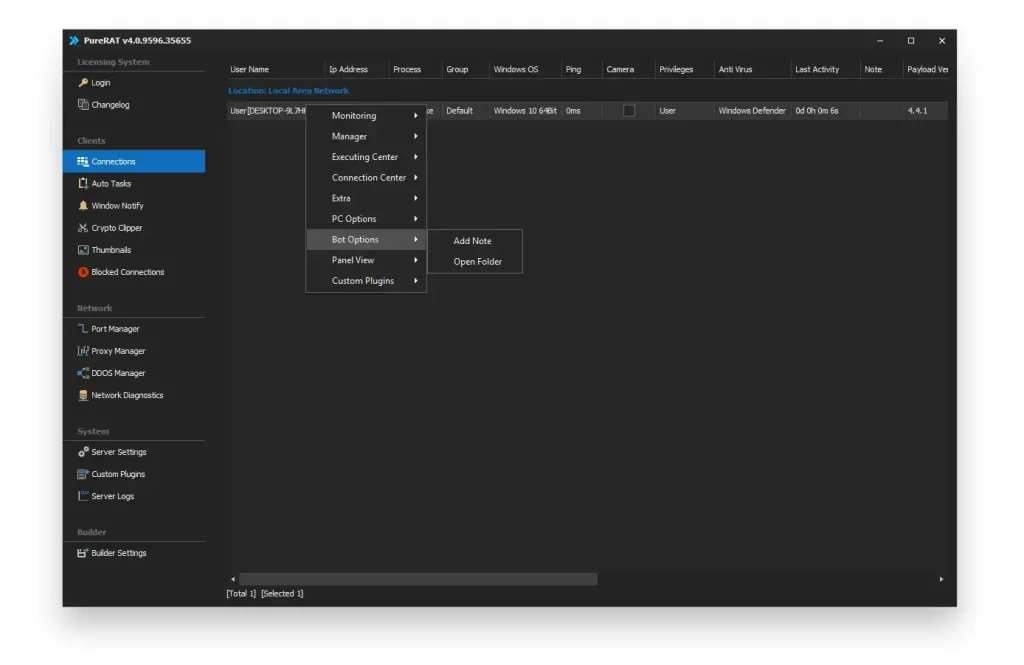
🖥️ bot options – Central Bot Management Interface in PureRAT 2026 Cracked
The bot options module serves as the central control dashboard for managing all infected systems. It provides a structured view of active bots, including system metadata, status information, and network details. This interface allows classification of infected machines based on their behavior or system characteristics. It also supports real-time visibility into bot activity. From a cybersecurity perspective, this module functions like a command console for distributed systems. It helps organize large-scale infected environments efficiently. It enables tracking of system-level changes across multiple machines. It improves operational awareness for the controlling entity. It represents a centralized botnet management system.
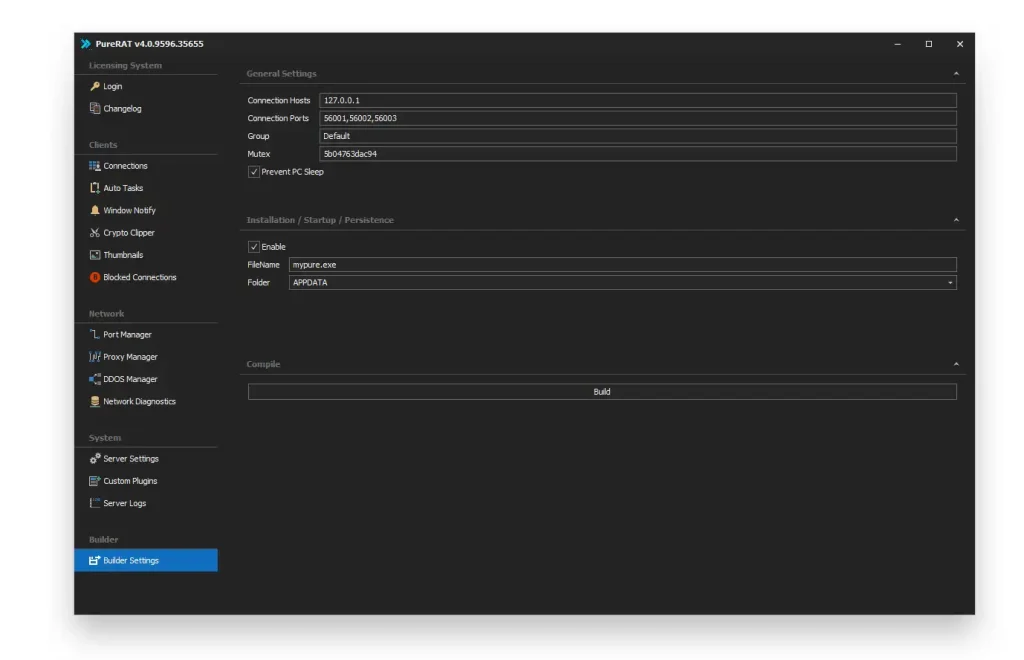
🛠️ bot settings – System Configuration Control Layer of PureRAT 2026 Cracked
The bot settings module controls how infected systems behave after deployment. It allows modification of execution rules, system interaction logic, and communication behavior. This module ensures that malware can adapt to different environments dynamically. It also controls how files are stored and executed within the system. From a threat analysis perspective, it represents the configuration engine of the malware. It supports customization for different target environments. It ensures consistency in execution behavior. It also helps maintain system stability across infected hosts. It is essential for scalable malware deployment.
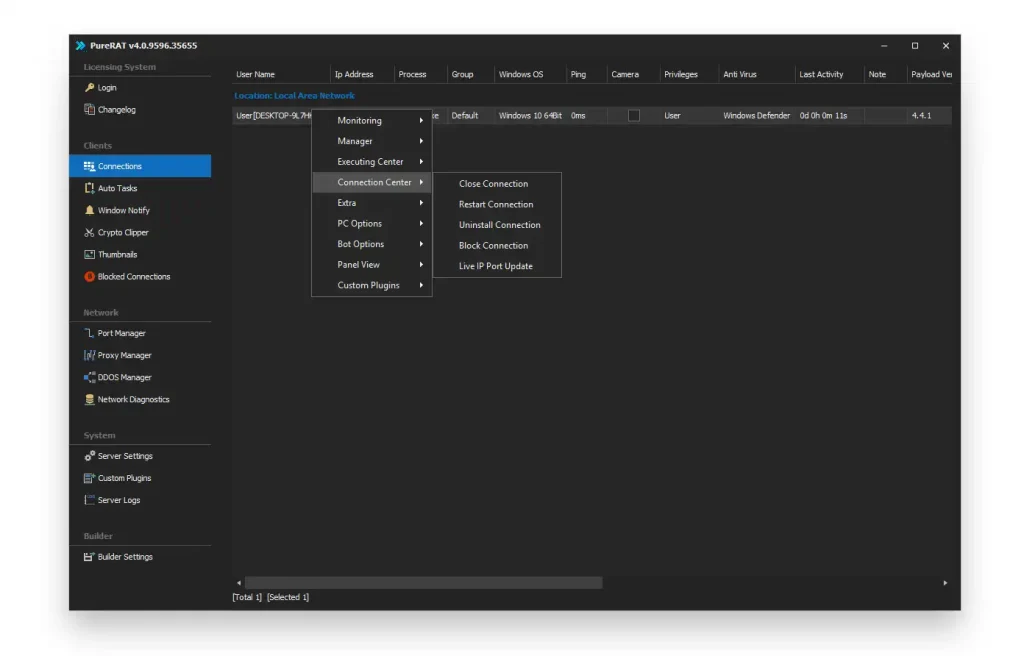
🔗 connection center – Communication Management System PureRAT 2026 Cracked
The connection center is responsible for maintaining communication between infected systems and the command infrastructure. It manages active sessions, ensures connectivity, and handles reconnection logic in case of disruption. It also allows isolation or removal of specific infected machines from the network. This improves control over the botnet structure. From a cybersecurity perspective, it represents the communication backbone of the malware system. It ensures stable data exchange between components. It also supports infrastructure switching when needed. It increases resilience against disconnection. It is critical for maintaining botnet stability.
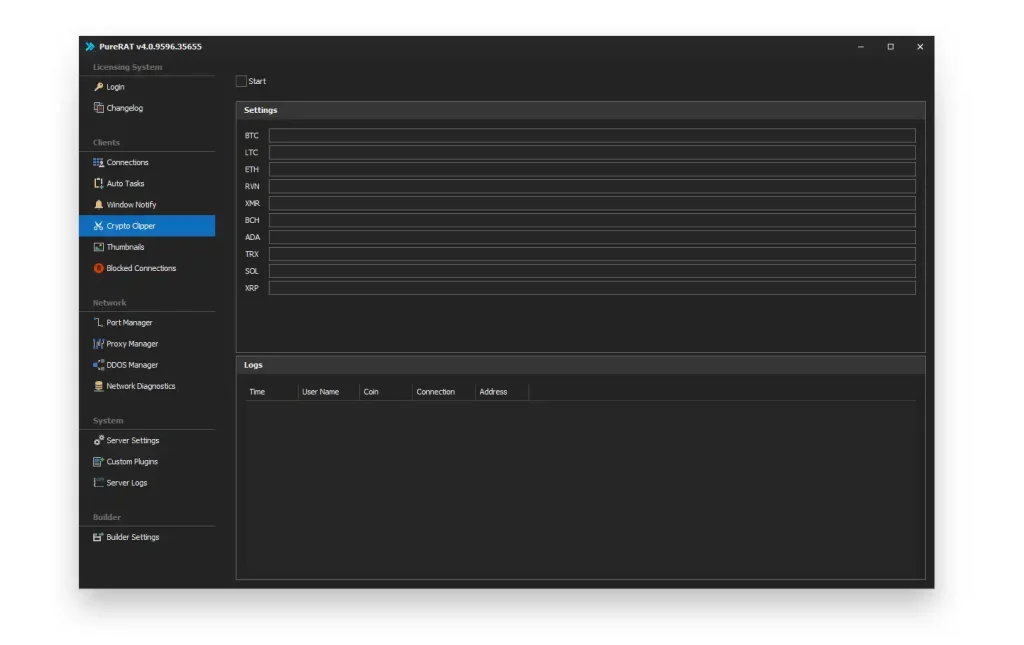
💰 crypto clipper – Financial Data Manipulation Module PureRAT 2026 Cracked
The crypto clipper module is designed to monitor clipboard activity for cryptocurrency-related data. It detects wallet addresses copied by the user and silently modifies them before transaction execution. This results in unintended redirection of digital funds. It operates in the background without user awareness. From a cybersecurity perspective, it is classified as a financial manipulation mechanism. It targets cryptocurrency transactions specifically. It supports multiple blockchain formats and wallet types. It increases financial exploitation potential. It is a high-risk data interception module.
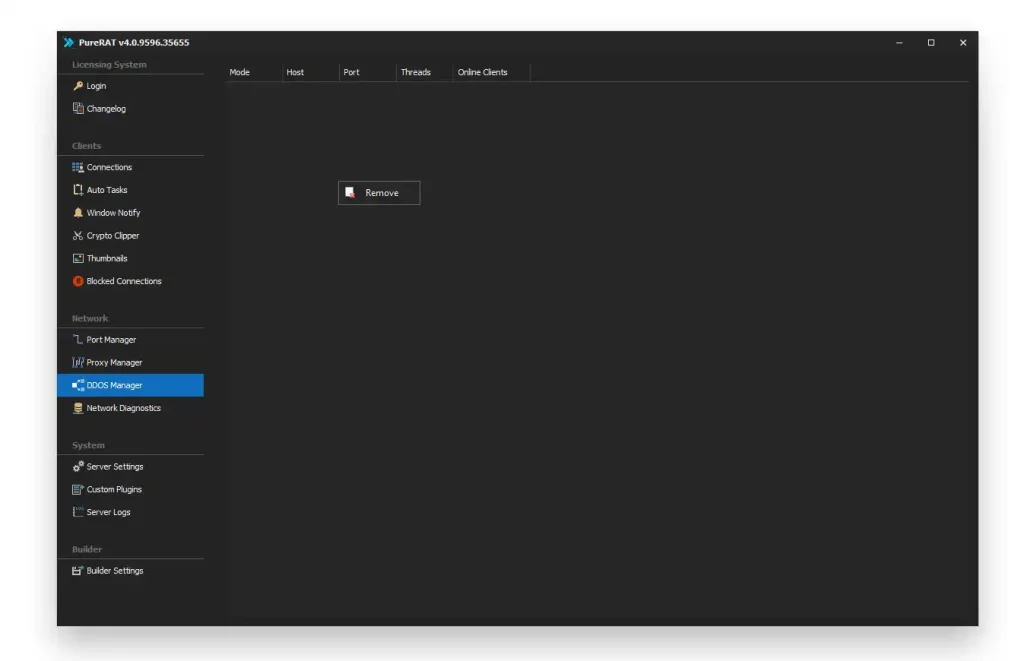
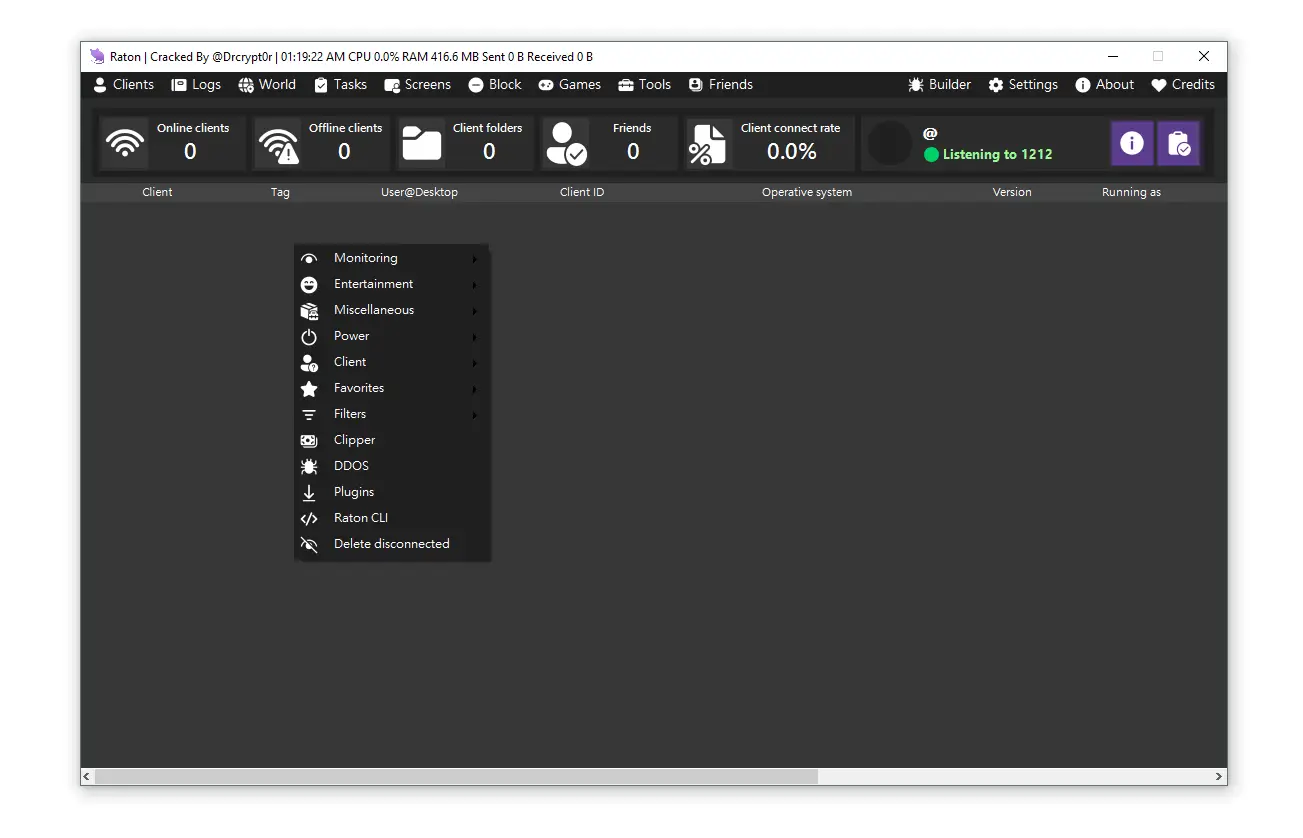
🌐 ddos manager – Distributed Traffic Attack System PureRAT 2026 Cracked
The DDoS manager module enables coordinated traffic generation from multiple infected systems. It is designed to overwhelm target servers with excessive network requests. This results in service disruption or downtime. It allows configuration of attack intensity and duration. From a cybersecurity standpoint, it represents a distributed denial-of-service control system. It synchronizes multiple machines for unified execution. It increases scalability of network attacks. It supports multiple attack modes. It is a core botnet functionality component.
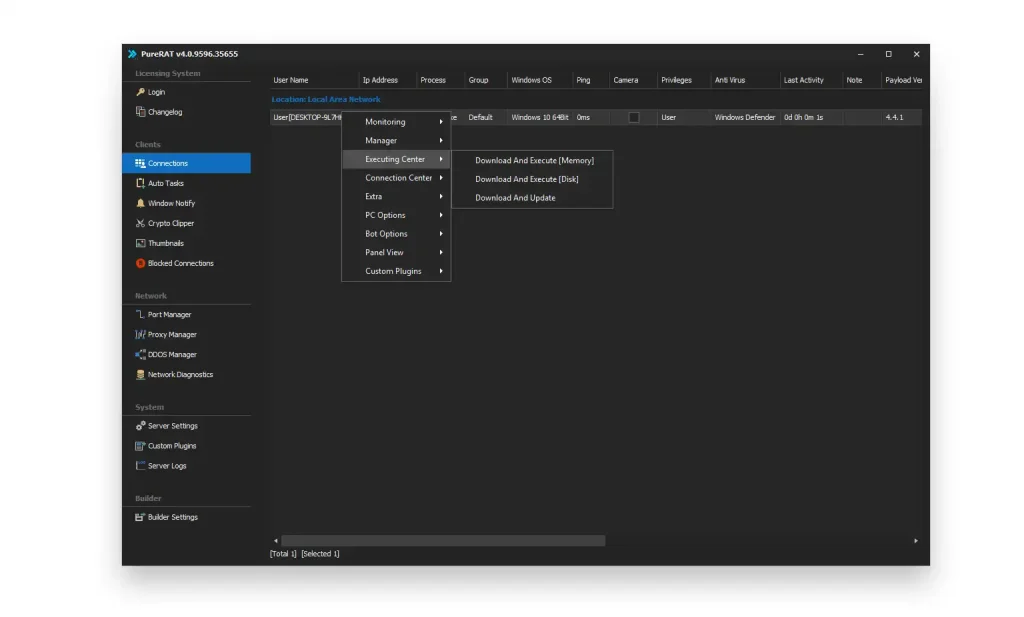
⚙️ executing center – Remote Execution Engine PureRAT 2026 Cracked
The executing center module allows execution of additional processes on infected systems. It supports remote deployment of payloads either in memory or on disk. It enables updating or modifying malware components dynamically. From a threat intelligence perspective, it is a remote execution engine. It supports system-level command deployment. It increases flexibility of malware operations. It allows continuous evolution of the infection. It is essential for maintaining long-term control over systems. It enhances operational adaptability.
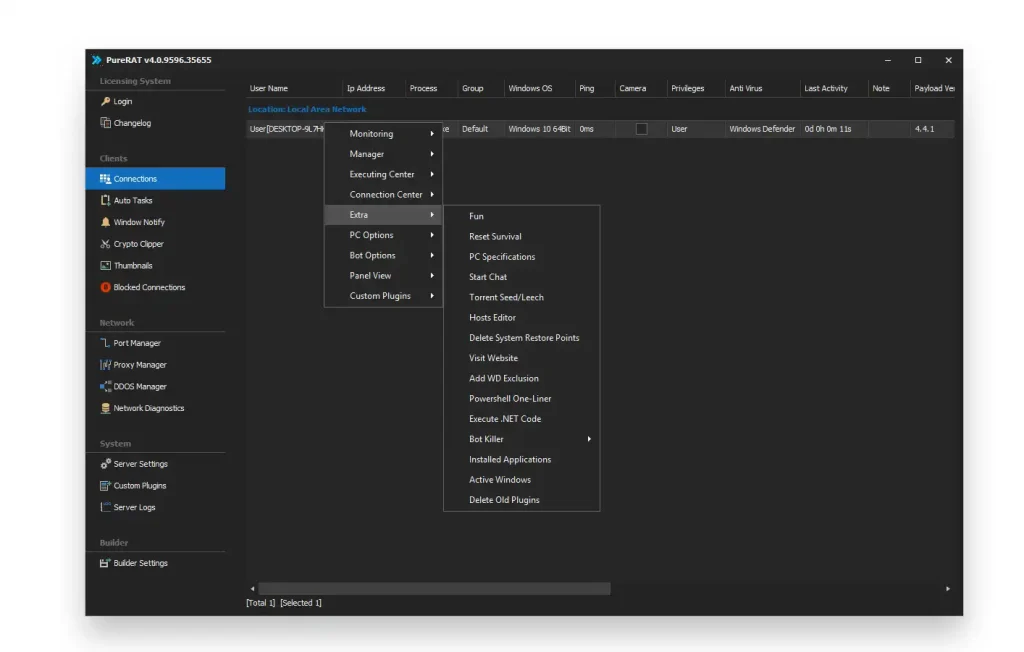
🔧 extra options – Auxiliary Control Module PureRAT 2026 Cracked
The extra options module provides additional system-level functionalities that extend malware capabilities. It may include system manipulation, service control, or auxiliary execution tools. It supports interaction with system resources beyond core modules. From a cybersecurity perspective, it acts as an extension layer. It enhances operational versatility. It may support automation of secondary tasks. It increases control depth over infected systems. It integrates advanced system modification features. It expands overall malware functionality.
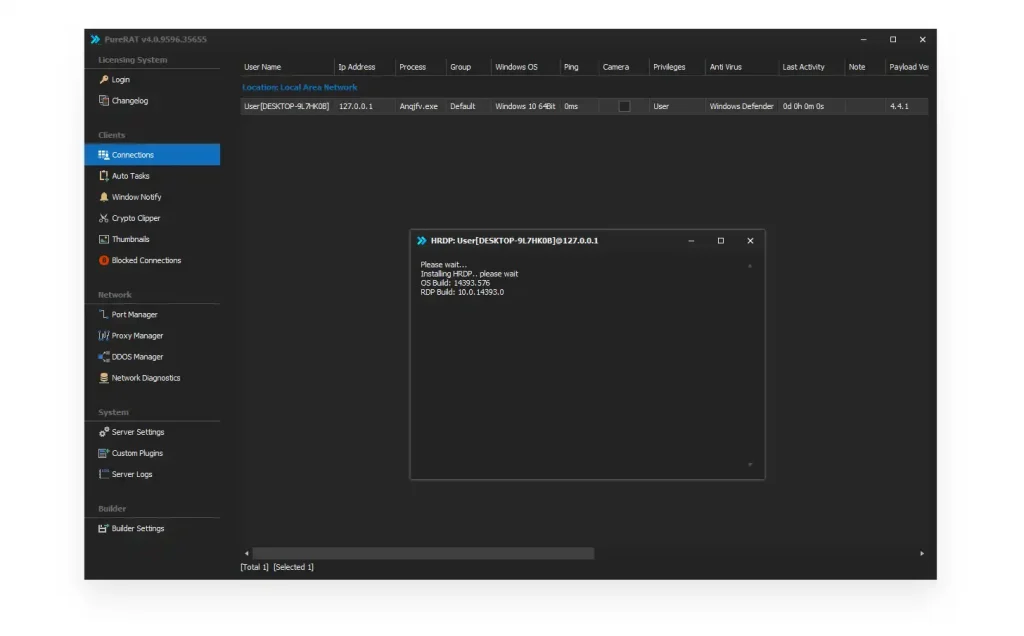
🖥️ hidden rdp – Invisible Remote Desktop System
The hidden RDP module enables remote desktop access without visible user awareness. It creates a hidden session that allows full system interaction. The user does not see the remote activity occurring in parallel. From a cybersecurity perspective, this is a stealth remote access mechanism. It enables graphical system control without detection. It supports full system navigation and interaction. It bypasses normal user interface visibility. It is often associated with advanced surveillance frameworks. It is a high-risk stealth control feature.
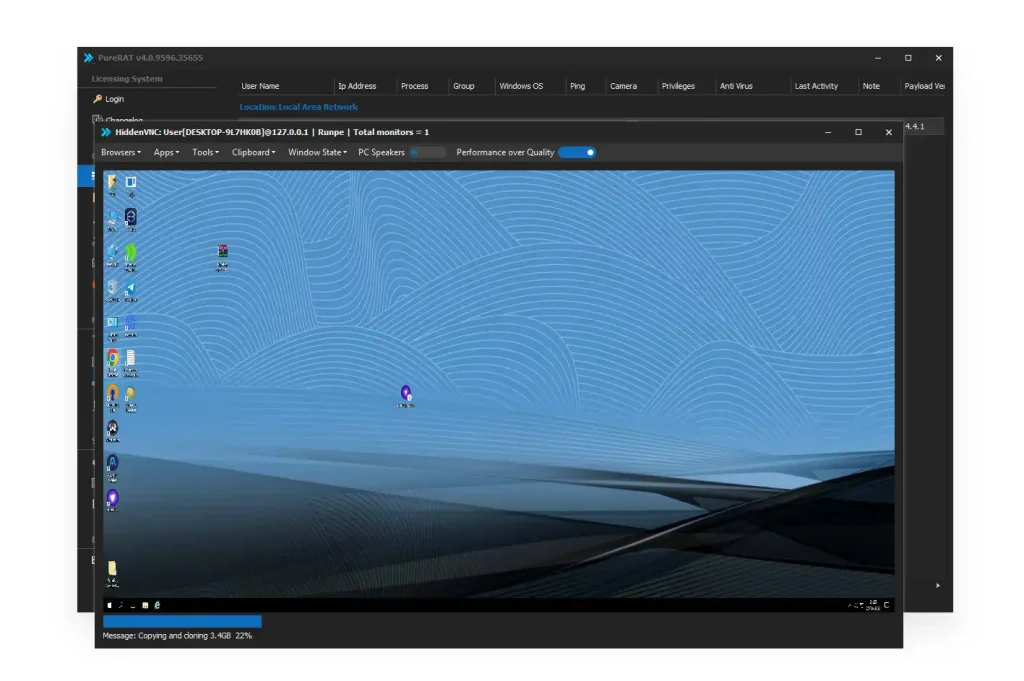
🧠 hvnc – Hidden Virtual Network Computing System PureRAT 2026 Cracked
The HVNC module creates a completely hidden desktop environment separate from the user session. It allows attackers to interact with the system in an isolated virtual interface. The victim does not see any activity occurring. It is considered one of the most advanced stealth technologies in malware. It supports independent application execution. It allows hidden browsing and system interaction. It bypasses normal desktop monitoring. It enables full invisible control. It is a key surveillance module in modern RAT systems.
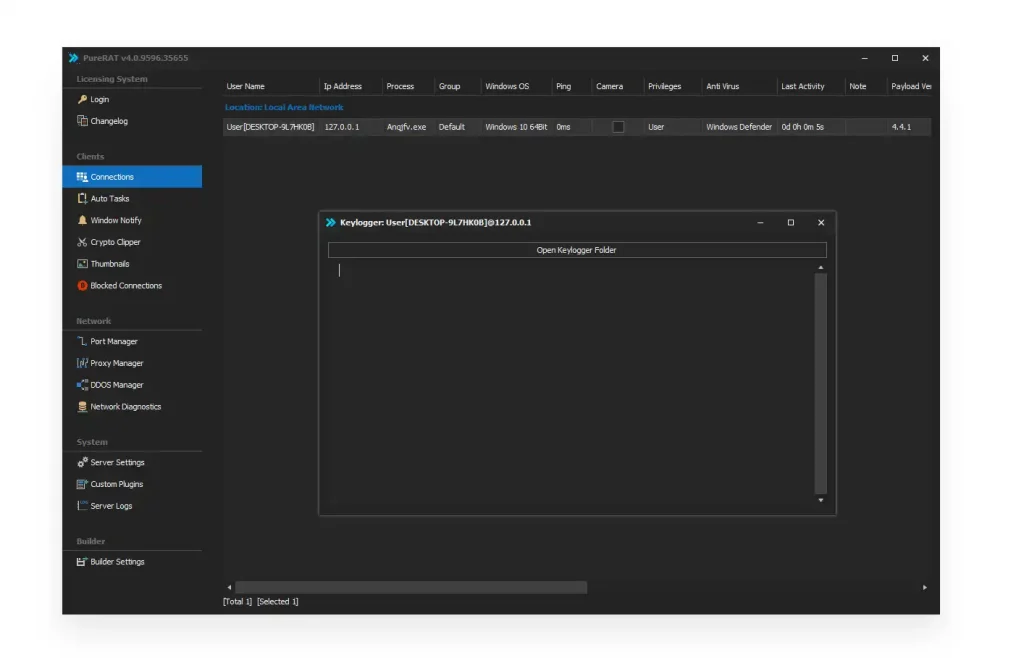
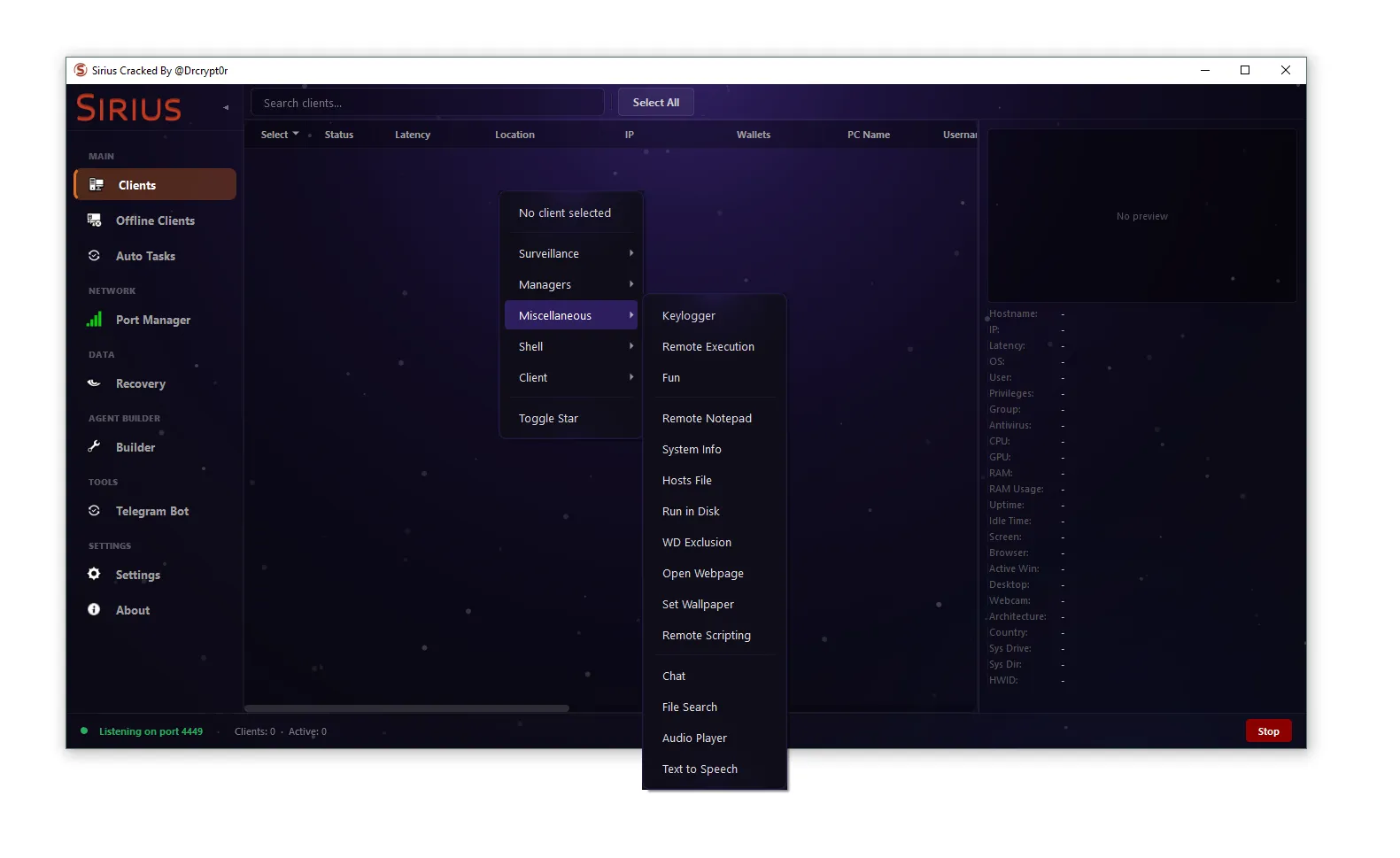
⌨️ keylogger – Input Capture Engine PureRAT 2026 Cracked
The keylogger module records all keyboard inputs from infected systems. It captures sensitive information such as passwords, messages, and login credentials. It operates at a low system level to ensure complete capture coverage. From a cybersecurity perspective, it is a primary data extraction mechanism. It continuously logs user behavior. It supports structured input recording. It enables credential harvesting. It is widely used in surveillance-based malware. It is a core threat component.
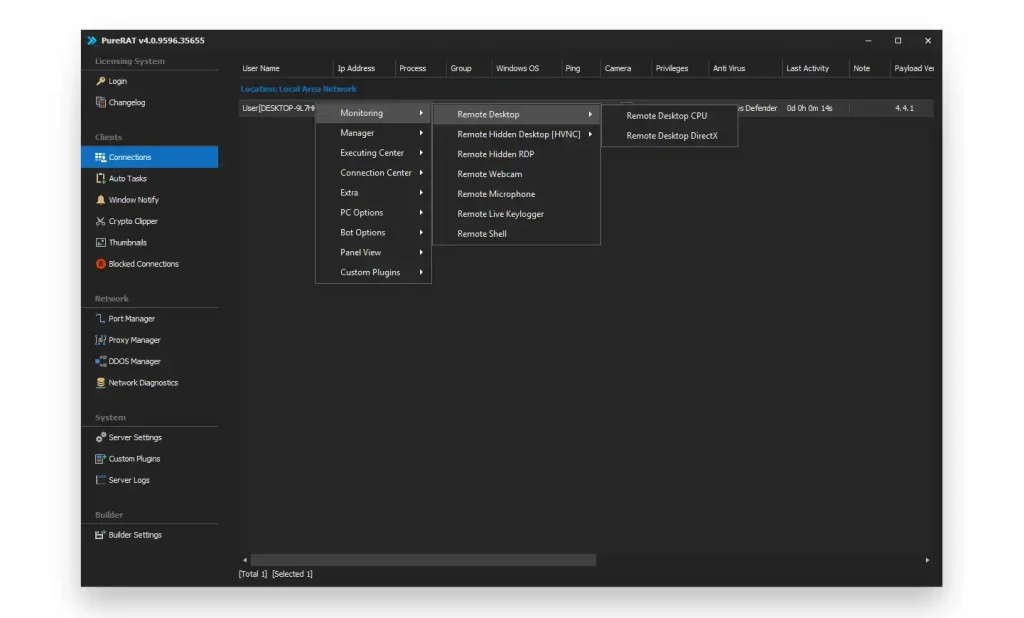
👁️ monitoring – Activity Surveillance System PureRAT 2026 Cracked
The monitoring module tracks system activity in real time. It observes user actions, system processes, and application behavior. It provides continuous visibility into infected machines. From a cybersecurity standpoint, it is a surveillance engine. It supports behavioral tracking. It enables activity logging. It enhances system awareness for attackers. It is essential for monitoring compromised environments. It improves operational intelligence.
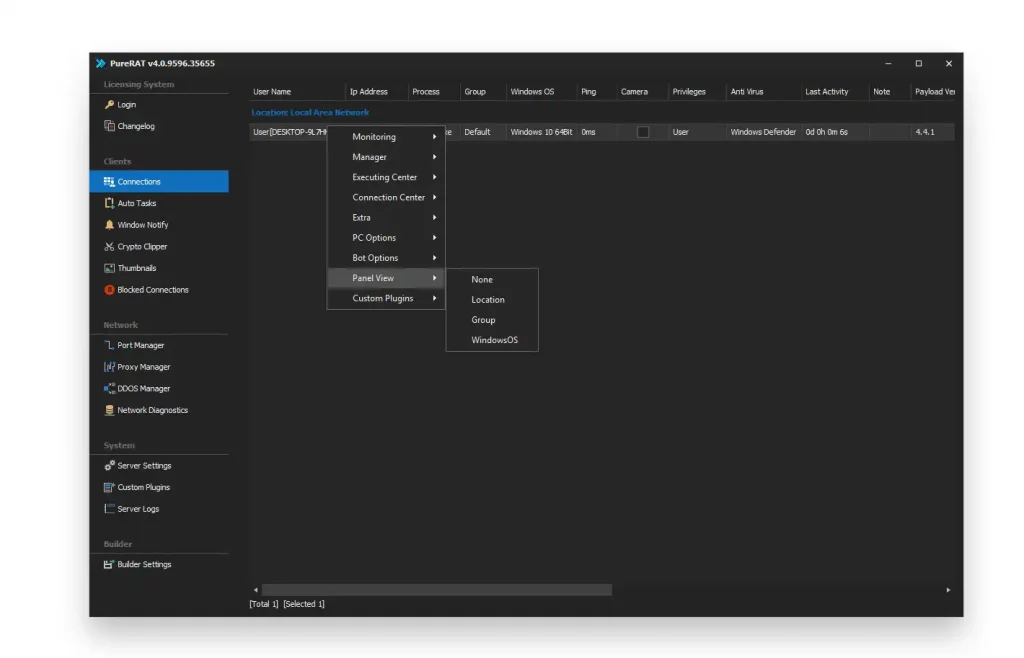
🧭 panel view – Central Interface Navigation System PureRAT 2026 Cracked
The panel view module manages the main interface of the malware control system. It allows switching between different views such as bots, sessions, and monitoring tools. It organizes system data visually for easier control. From a cybersecurity perspective, it is a UI management layer. It improves usability of the control system. It supports structured navigation. It organizes complex botnet data. It enhances operational efficiency. It acts as the dashboard controller.
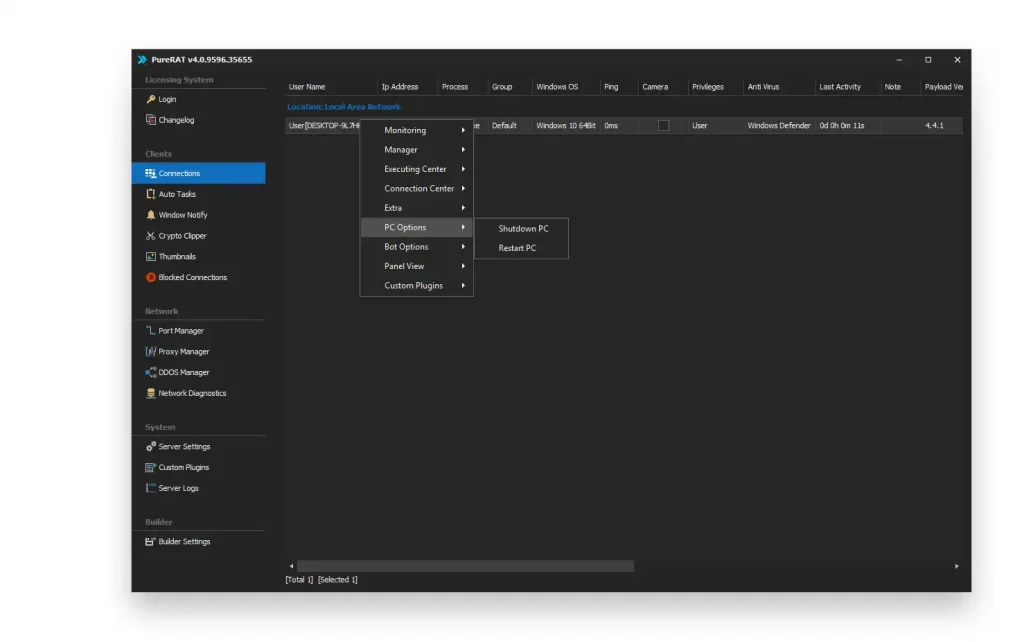
🔌 pc options – System Power Control Module PureRAT 2026 Cracked
The pc options module allows execution of system-level power actions. It can trigger shutdown, restart, or system interruption commands. It affects the stability of infected machines. From a cybersecurity perspective, it is a disruption control system. It enables direct system manipulation. It can be used to interrupt user activity. It supports administrative-level control. It enhances system disruption capabilities. It is part of system management features.
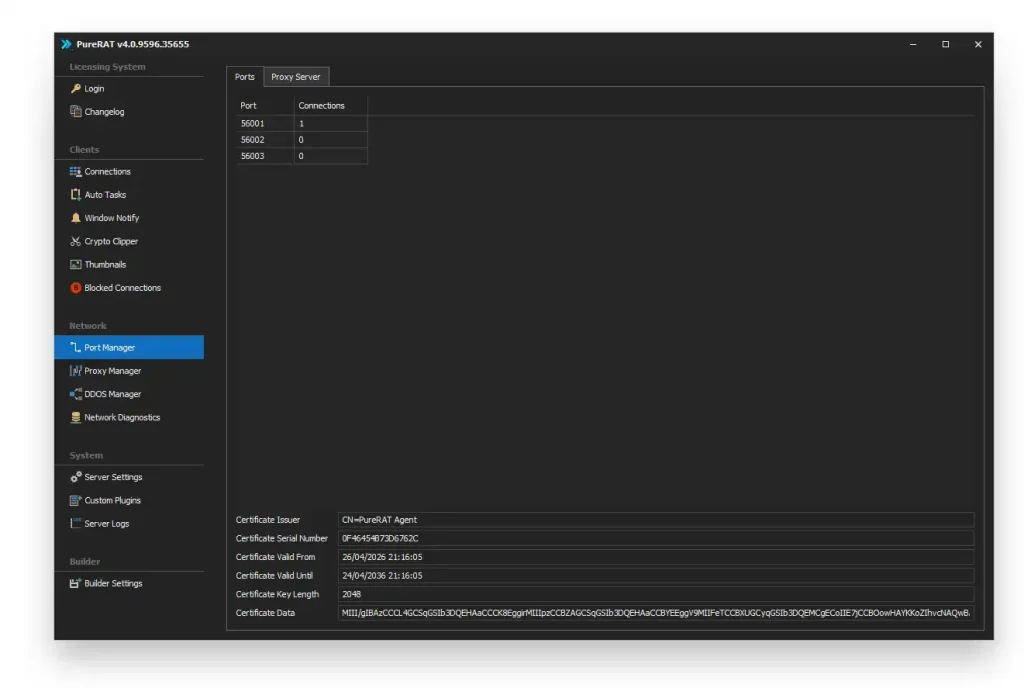
🌐 port manager – Network Configuration System
The port manager module controls communication ports used by infected systems. It defines how data is transmitted between bots and control servers. It also manages encryption certificates and connection parameters. From a cybersecurity perspective, it is a network configuration engine. It ensures stable communication channels. It supports secure data transmission. It allows infrastructure-level control. It is essential for maintaining connectivity. It enhances network architecture stability.
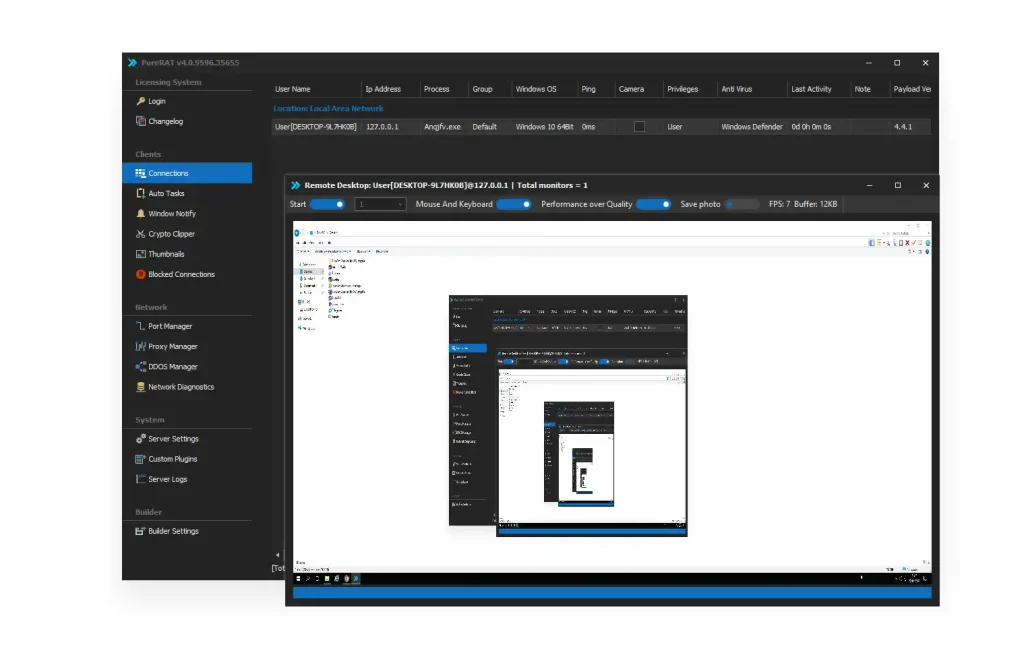
🖥️ remote desktop – Graphical Control System
The remote desktop module enables full graphical control of infected systems. It allows real-time viewing and interaction with the victim’s screen. It supports mouse and keyboard control remotely. From a cybersecurity perspective, it is a full remote administration tool. It enables system navigation. It allows application interaction. It supports real-time system manipulation. It is a core control feature in RAT systems. It provides full visual access.
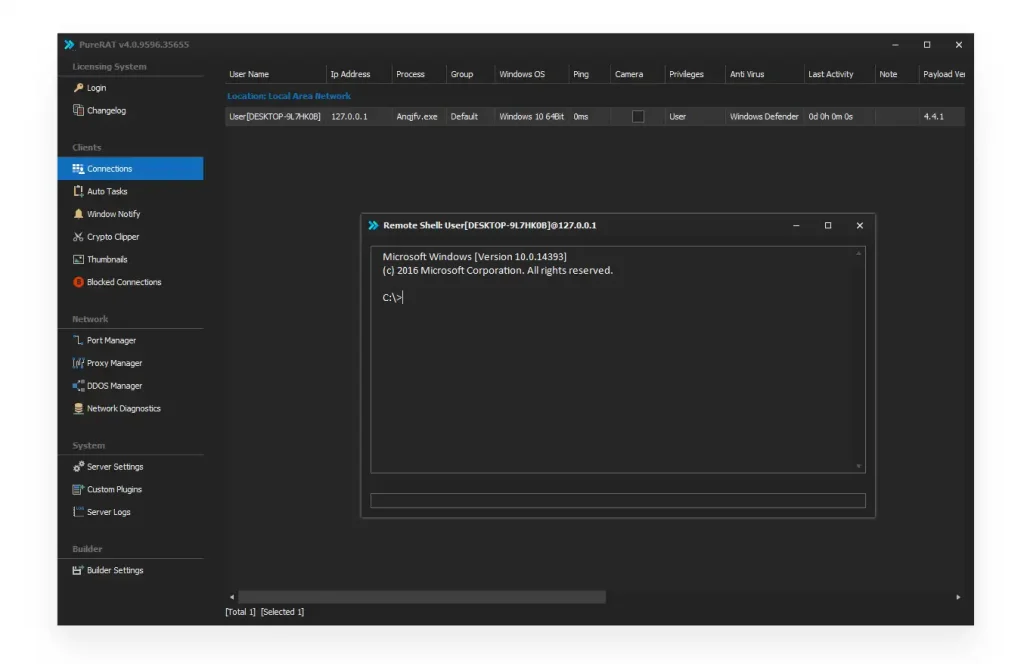
💻 remote shell – Command Execution Interface
The remote shell module provides command-line access to infected systems. It allows execution of system commands remotely. It supports administrative-level operations. From a cybersecurity perspective, it is a system control interface. It enables deep system manipulation. It supports process execution and file operations. It allows direct OS interaction. It is a high-privilege access module. It enhances system control depth.
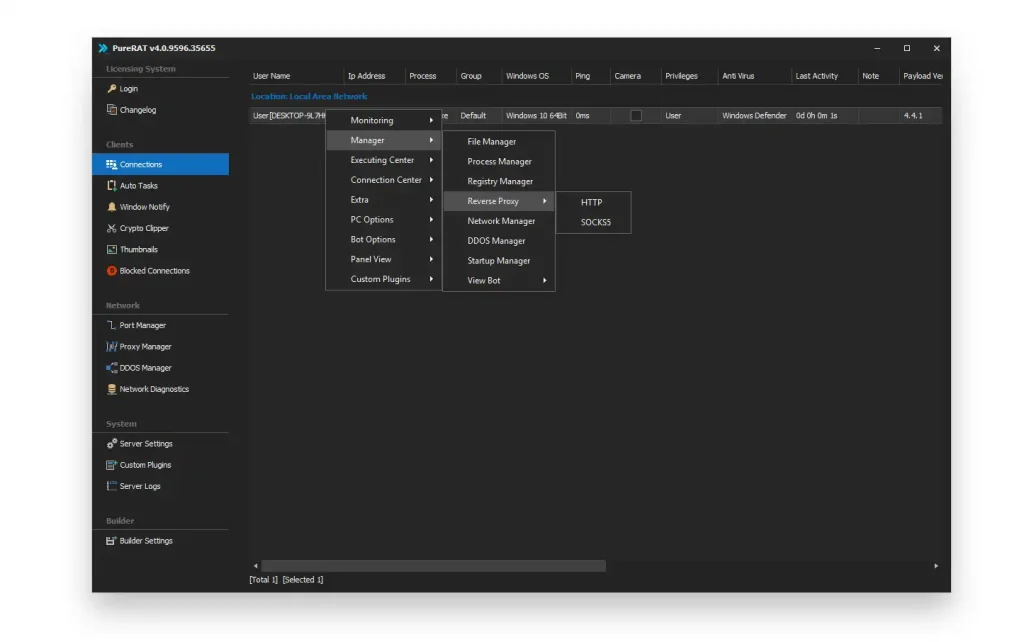
🌐 reverse proxy – Network Obfuscation Layer
The reverse proxy module hides communication between infected systems and control servers. It routes traffic through intermediate layers. It masks the original source of network activity. From a cybersecurity perspective, it is an anonymity and obfuscation system. It improves infrastructure concealment. It reduces traceability. It supports encrypted routing. It enhances operational security. It is critical for hiding command infrastructure.
Download PureRAT 2026 Cracked
Virus Total Report of PureRAT 2026 Cracked
https://www.virustotal.com/gui/file/cbb7054729aa980965d4b65495b2a89c1896f739d1c311d714dbcafd027d34af?nocache=1📌 CONCLUSION
PureRAT 2026 Cracked demonstrates a highly modular cybersecurity threat architecture combining automation, surveillance, remote control, and network obfuscation. Each module contributes to a distributed system designed for persistence and long-term system control.
Understanding these components is essential for building modern cybersecurity defenses, endpoint protection systems, and threat intelligence frameworks.
❓ FAQ
❓ What is PureRAT 2026 Cracked?
It is a modular Remote Access Trojan analyzed in cybersecurity research.
❓ What is HVNC in malware analysis?
It creates hidden desktop sessions for stealth system control.
❓ How does a keylogger work?
It captures all keyboard input from infected systems.
❓ What is the role of a botnet?
It enables centralized control of multiple infected machines.
❓ Can PureRAT be detected?
Yes, behavioral security systems can detect suspicious activity.