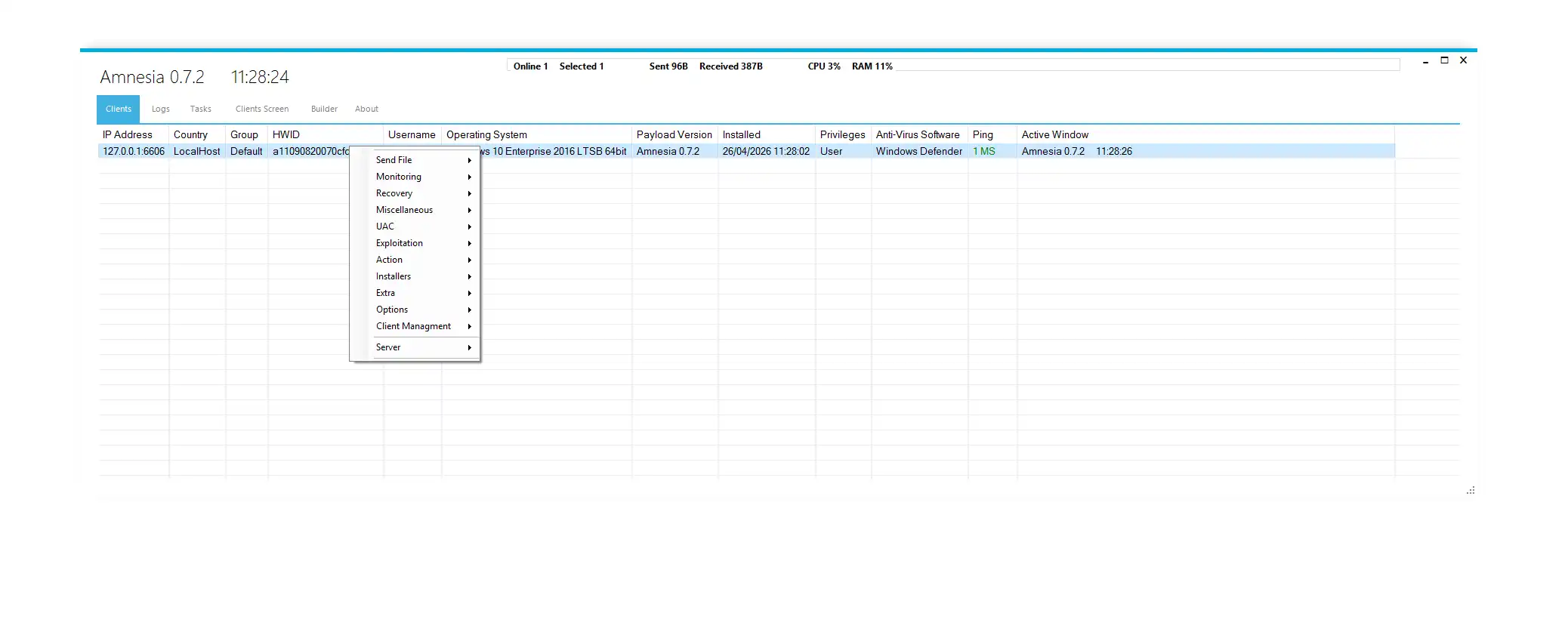
Amnesia 0.7.2
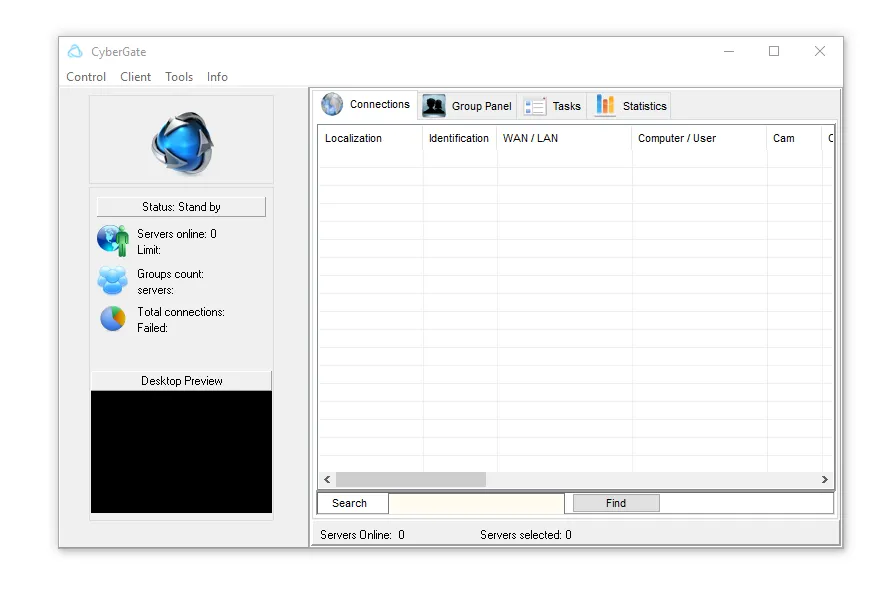
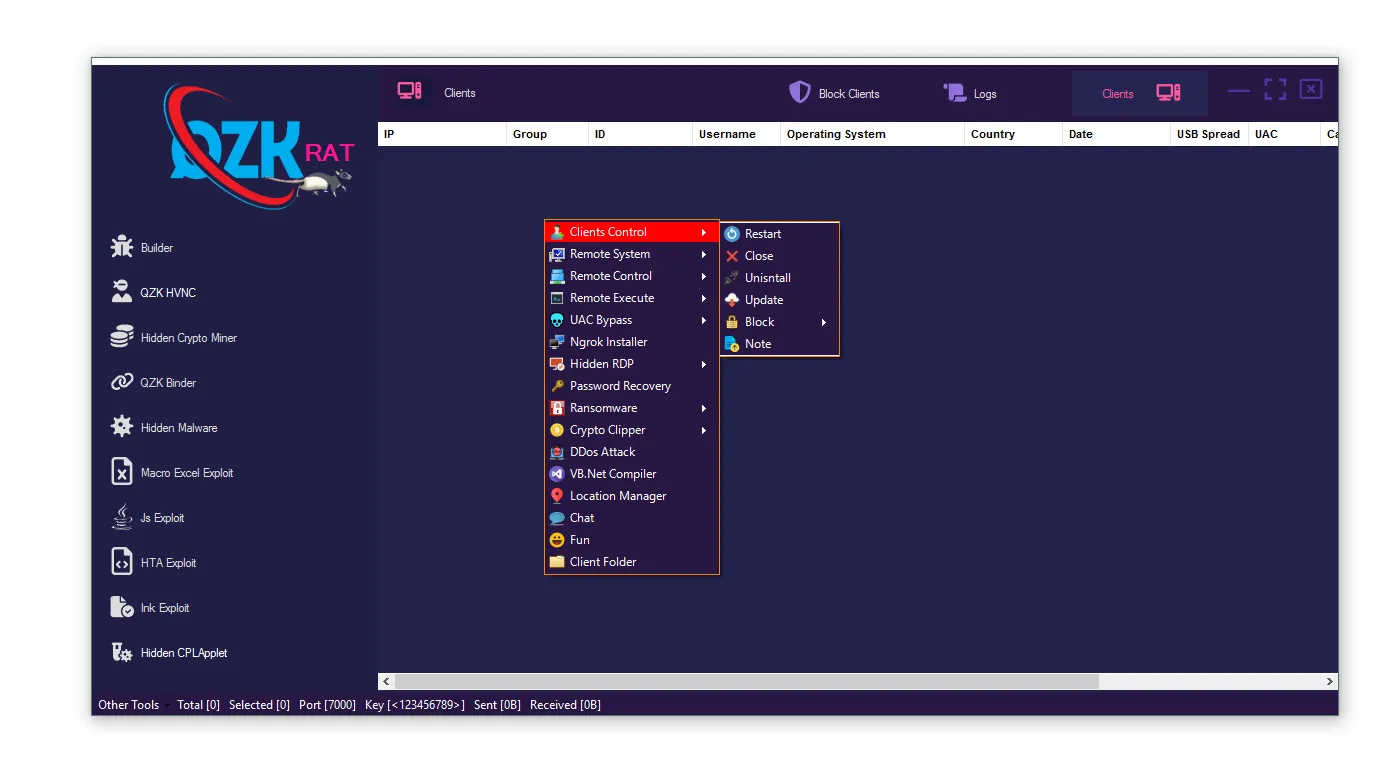
Amnesia 0.7.2 is a highly advanced Remote Access Trojan (RAT) designed for Windows operating systems. In modern cybersecurity terminology, it belongs to the category of multi-functional malware frameworks, meaning it is not limited to a single attack method but combines surveillance, exploitation, data theft, persistence, and system control in one platform.
Unlike traditional malware, Amnesia 0.7.2 operates like a full cyber operations toolkit. It enables attackers to remotely control infected machines, steal sensitive information, bypass security systems, and maintain long-term access without detection.
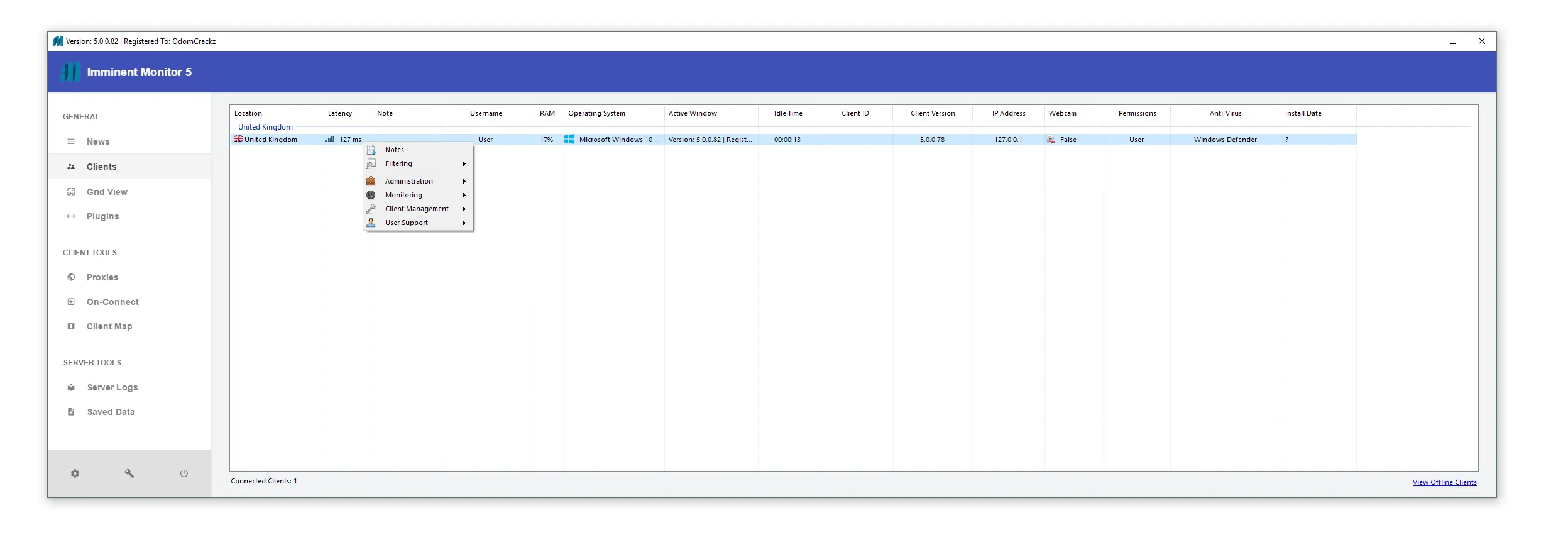
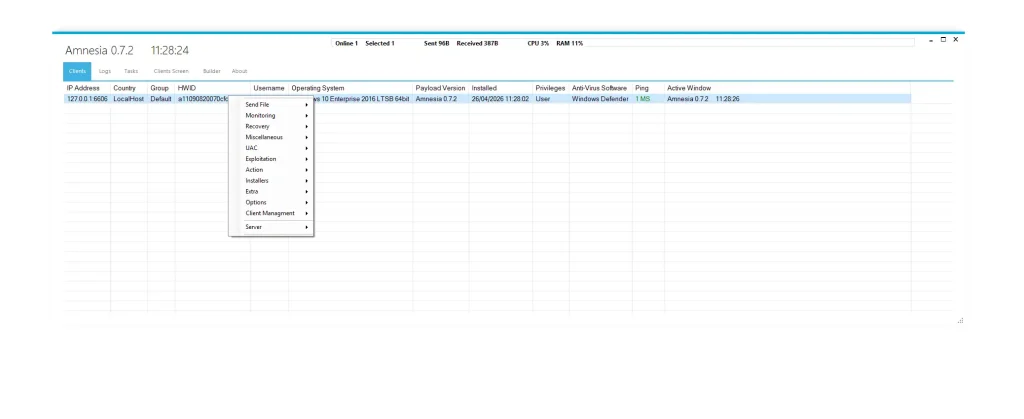
🖥️ action — Core Control Interface
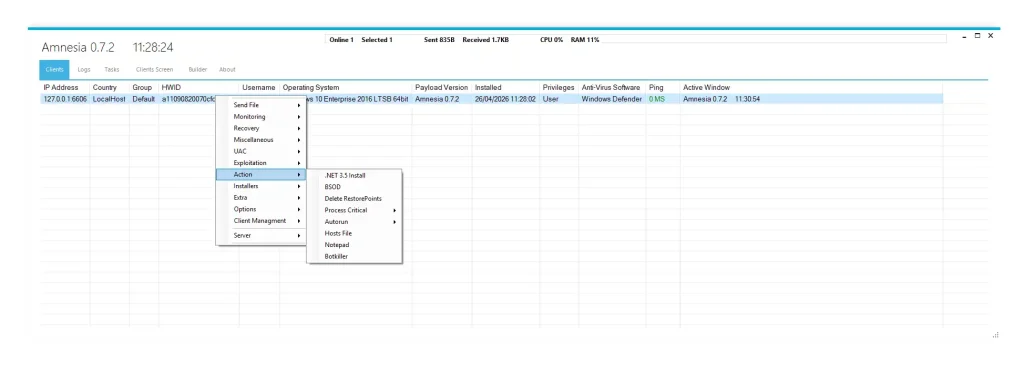
⚙️ Command-and-Control (C2) Dashboard Overview
- 🛰️ IP Address & Country Tracking:
This feature allows attackers to identify the physical and geographic location of infected systems. It helps cybercriminals segment victims based on region, industry, or value. In advanced cyber campaigns, this data is used to prioritize targets such as financial institutions or enterprise networks. It also supports global botnet mapping for large-scale operations. - 🧬 HWID Fingerprinting System:
Hardware-based identification ensures that each infected machine remains trackable even after reinstalling the operating system. This creates a persistent digital fingerprint tied to the physical device. It is commonly used in advanced persistent threat (APT) operations where long-term access is required. - 🗂️ Group-Based Device Organization:
Infected systems are grouped for easier management. Attackers can categorize devices by role, location, or infection stage. This improves scalability when controlling thousands of systems in coordinated cyberattacks. - 🧪 Local Testing Environment (localhost mode):
This feature allows attackers to test malware behavior before real deployment. It simulates infection scenarios without exposing real infrastructure. This indicates a professional-level malware development cycle similar to underground cybercrime frameworks. - 📊 Real-Time System Monitoring:
Attackers can monitor CPU usage, active windows, and system performance. This helps identify when a user is idle or active. Such behavioral intelligence is often used to time data theft or credential harvesting.
🏗️ builder & builder options — Payload Configuration System
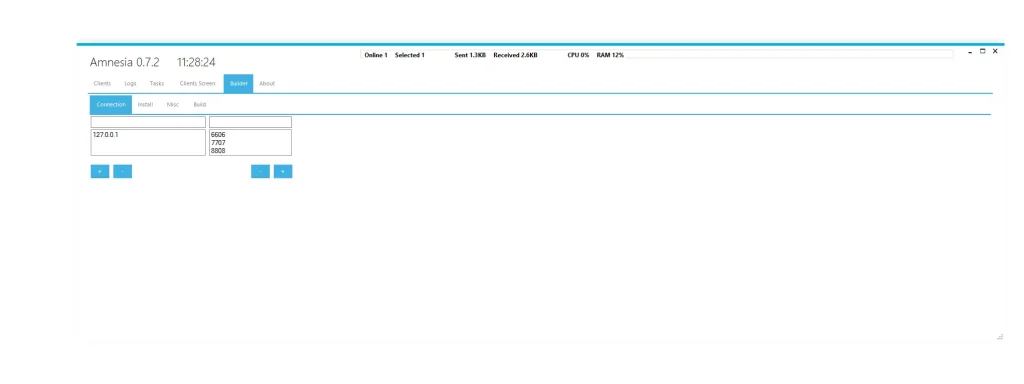
⚙️ Malware Customization Engine
- 🔌 Multi-Port C2 Configuration:
The malware supports multiple communication ports such as 6606, 7707, and 8808. This allows flexible communication between infected systems and attacker servers. It helps bypass firewall restrictions and reduces detection by network monitoring systems. - 🛡️ Windows Defender Disabling Module:
This feature modifies system registry settings to disable Windows Defender protections. It ensures malware execution without interruption from antivirus software. It is a common technique used in stealth malware campaigns.
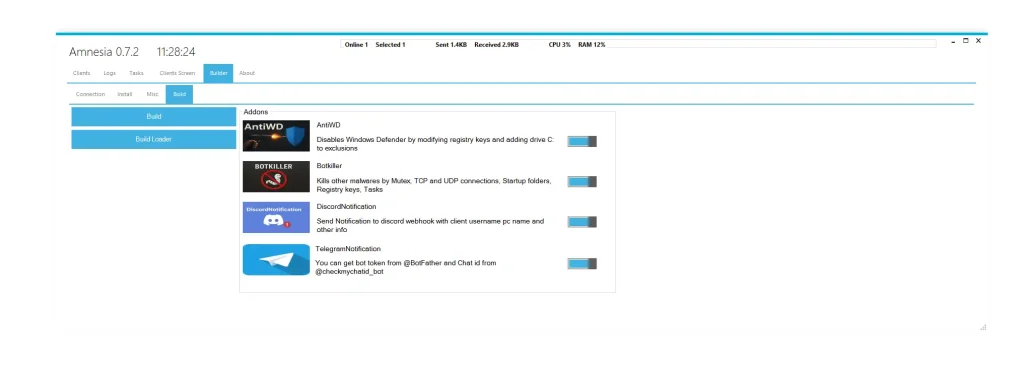
- ⚔️ Bot-Killer Functionality:
The malware removes competing threats from the infected system. It targets other RATs, keyloggers, and malicious processes. This ensures exclusive control over the compromised environment and prevents resource competition. - 📡 External Notification System:
Victim data can be sent to external platforms like Discord or Telegram. This allows attackers to receive real-time alerts about infections. It improves operational efficiency in managing multiple compromised devices. - ⚡ Lightweight Malware Design:
The system is optimized for low CPU and memory usage. This reduces detection probability by avoiding performance anomalies. Stealth optimization is a key feature in modern malware engineering.
🧑💻 client management — Host Control Panel
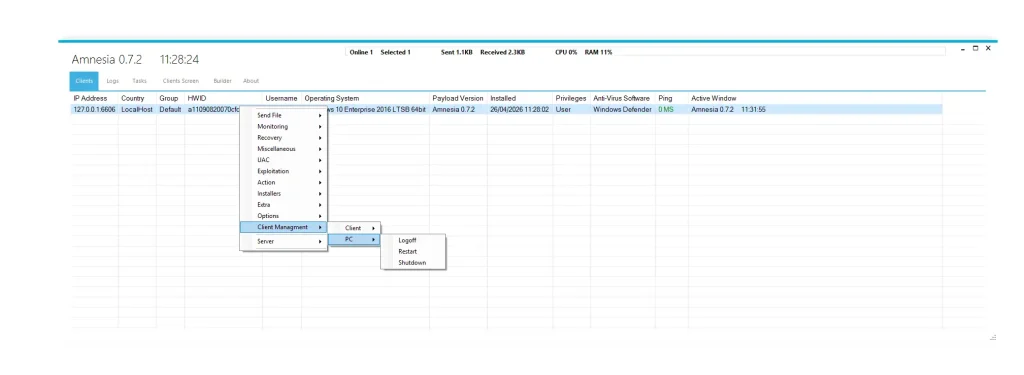
🖥️ Centralized Device Control System
- 👤 System Identity Profiling:
Displays username, operating system, and system configuration. This helps attackers understand the environment of each victim. It is useful for targeting enterprise systems with valuable data. - 🔐 Privilege Level Detection:
The system identifies whether the user has administrative access. This determines whether privilege escalation is required. It is a critical step in advanced attack chains. - 🛡️ Security Software Detection:
Installed antivirus products are automatically detected. This allows attackers to modify their attack strategy based on security defenses. It increases malware survival rate. - 📡 Real-Time Activity Tracking:
Network latency and active windows are monitored continuously. This provides behavioral intelligence about user activity. Attackers often use this data to execute attacks at optimal times. - ⚙️ Remote System Control:
Attackers can restart, shut down, or log off devices remotely. This gives complete administrative control over compromised systems.
🧨 exploitation — Security Bypass Tools
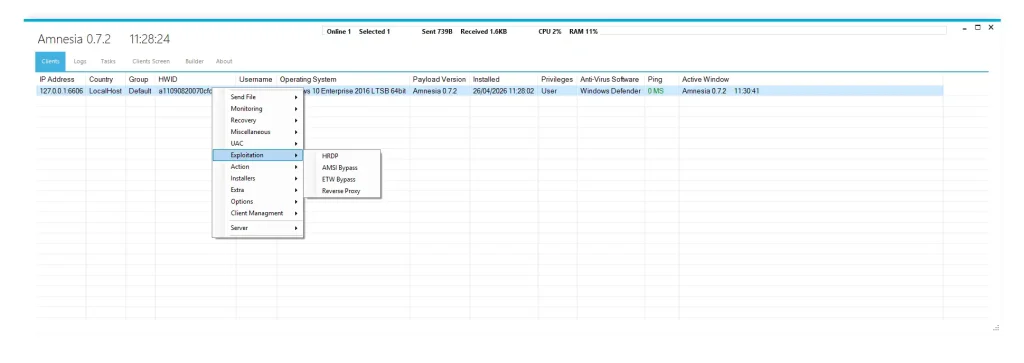
🔓 Advanced Windows Exploitation Framework
- 🧪 AMSI Bypass Technique:
Disables Windows Antimalware Scan Interface used for script scanning. This allows malicious PowerShell scripts to run undetected. It is widely used in fileless malware attacks. - 📉 ETW (Event Tracing for Windows) Disabling:
Prevents logging of system activities. This reduces forensic visibility and makes detection extremely difficult. It is a common anti-analysis technique. - 🖥️ HRDP Exploitation Module:
Enables remote desktop exploitation capabilities. Attackers can access graphical interfaces without user awareness. This simulates legitimate remote administration tools. - 🌐 Reverse Proxy Mechanism:
Allows attackers to bypass NAT and firewall restrictions. It creates a tunnel between infected systems and external servers. This enables remote access to internal networks.
🧩 extra option — Extended Malicious Functions
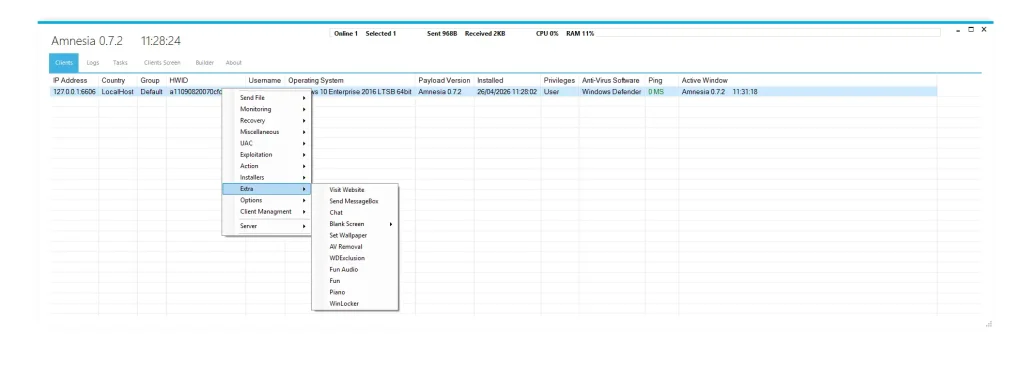
⚠️ Behavioral Manipulation Toolkit
- 🌐 Browser Redirection Attacks:
Victims are forced to visit attacker-controlled websites. This can be used for phishing campaigns or malware distribution. It manipulates user browsing behavior silently. - 💬 MessageBox Spam System:
Fake system alerts are displayed repeatedly. This creates confusion and psychological pressure on victims. It is commonly used in social engineering attacks. - 💻 Live Chat Functionality:
Enables real-time communication between attacker and victim. This can be used for ransom negotiation or intimidation. It adds a psychological attack layer. - 🖥️ Screen Blanking Feature:
Temporarily hides the victim’s screen while system remains active. This allows attackers to operate without detection. - 🎨 Desktop Manipulation:
Changes wallpaper and visual settings. This is used for harassment or control demonstration. - 🔊 Audio Control System:
Plays sounds or audio files on infected machines. It can be used for disruption or psychological manipulation. - 🔒 WinLocker Function:
Locks the victim out of their system completely. This behavior is similar to ransomware attacks.
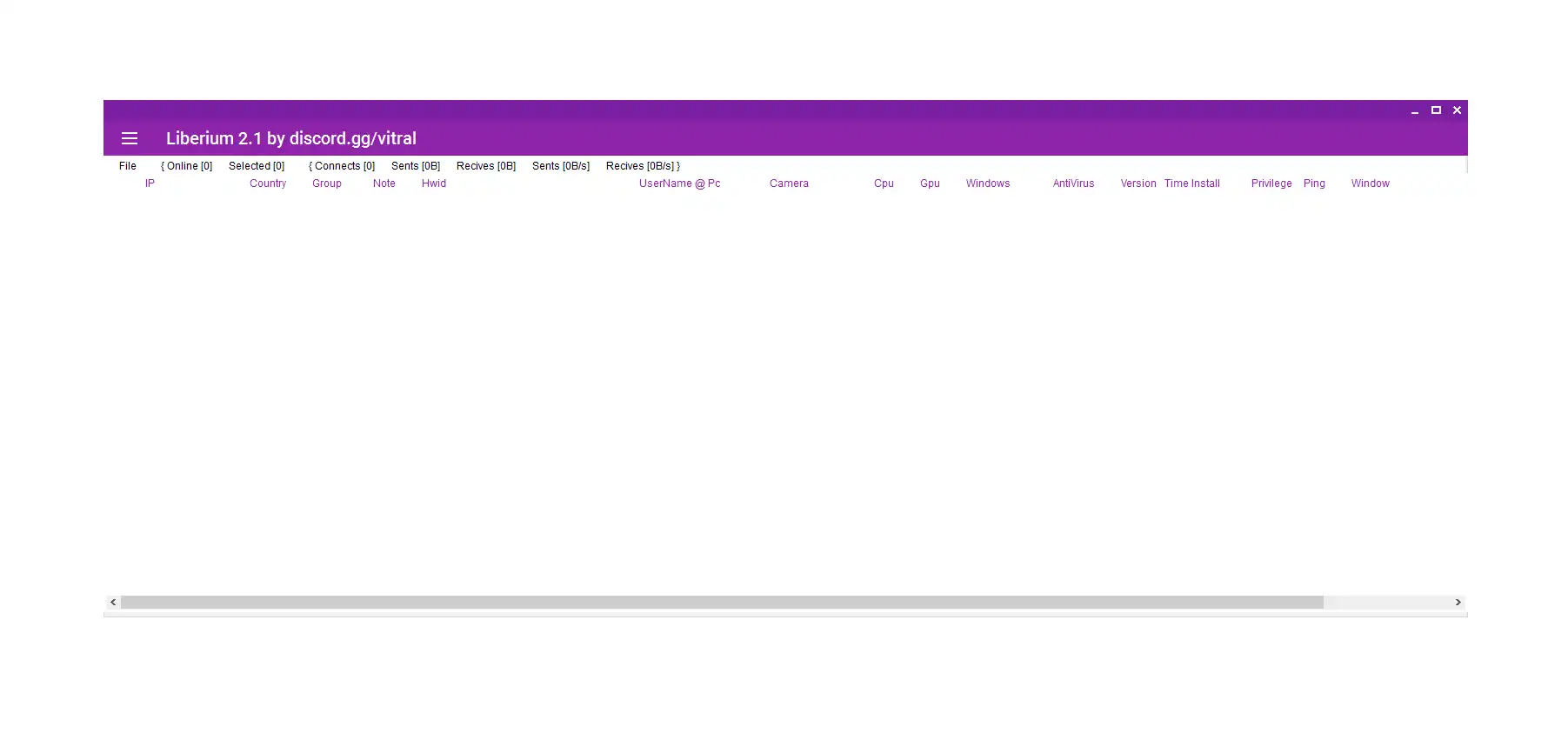
📡 feature image — Monitoring Dashboard
📊 Global Infection Tracking System
- 🟢 Online/Offline Device Monitoring:
Shows active and inactive infected systems. This helps attackers maintain botnet stability and manage global infections. - 📊 Traffic Monitoring System:
Tracks sent and received network data. This provides insights into stolen data volume and communication patterns. - ⚙️ Performance Analytics:
Displays CPU and RAM usage of infected devices. This ensures malware remains undetected by avoiding system overload.
⚙️ installer — Software Deployment System
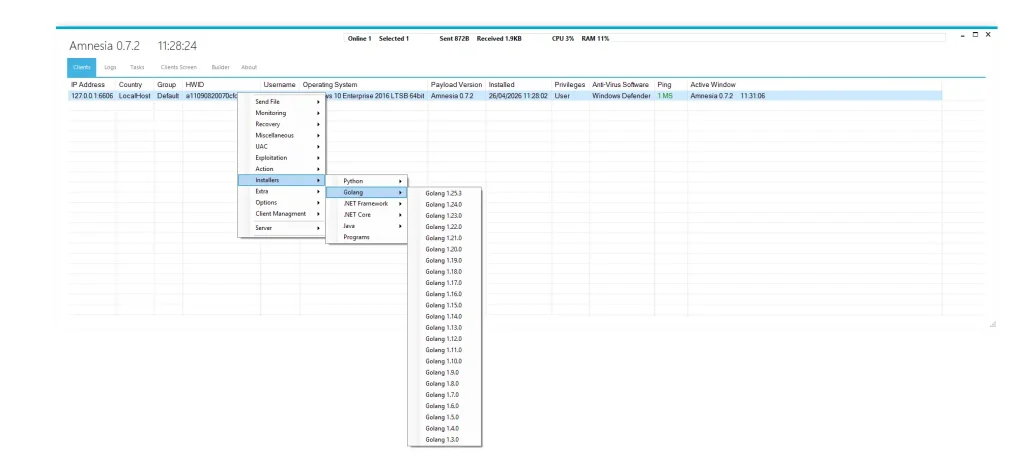
🧰 Remote Environment Installation
- 🐍 Programming Runtime Installation:
Supports Python, Java, .NET, and Golang installation. This converts infected systems into development environments. It can be used for secondary payload execution. - 🤖 Botnet Expansion Capability:
Installed tools help expand attack infrastructure. Infected systems become part of a distributed cyber network. - ⛏️ Cryptocurrency Mining Setup:
Systems can be configured for mining operations. This allows attackers to monetize victim hardware resources.
💣 miscellaneuous — Advanced Attack Toolkit
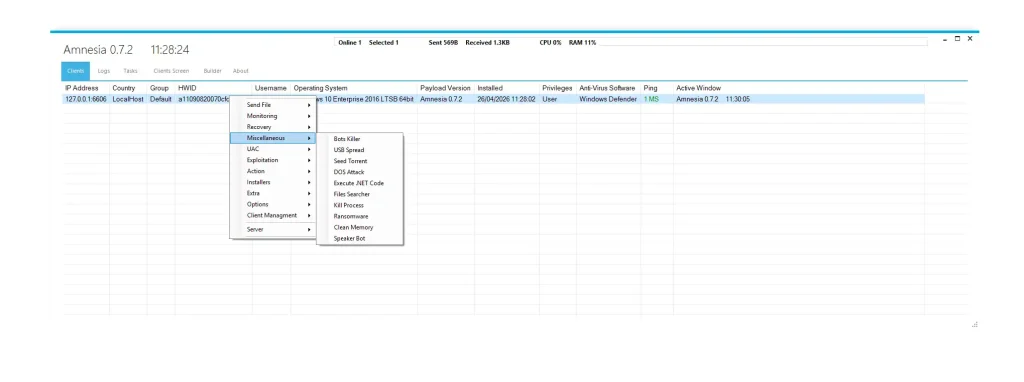
🔥 Offensive Cyber Operations Module
- 🔌 USB Propagation System:
Malware spreads through removable drives. This enables offline infection chains in restricted environments. - 🌐 DDoS Attack Capability:
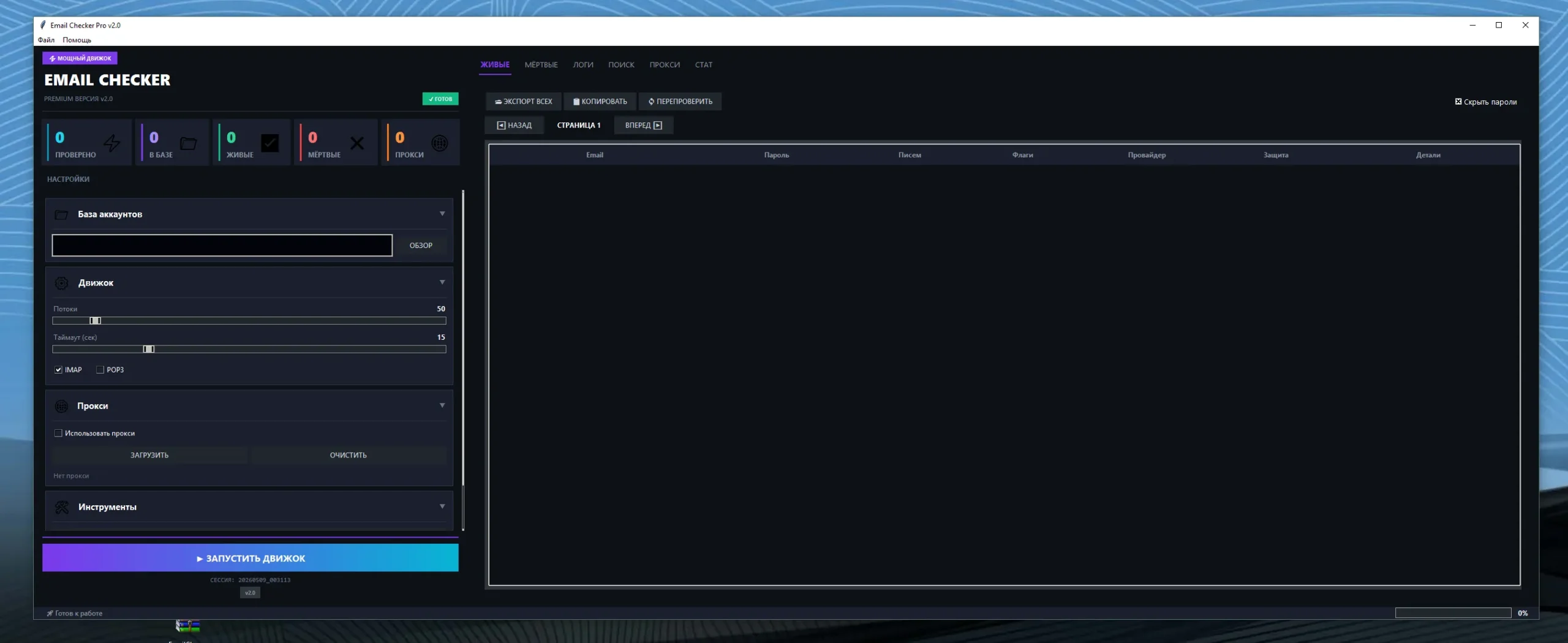
Infected systems are used to flood target servers with traffic. This causes service disruption or downtime. - 📁 File Theft Engine:
Automatically locates and extracts sensitive files. This includes documents, credentials, and system logs. - 🔐 Ransomware Module:
Encrypts files and demands ransom for decryption. This is a major cybercrime monetization method.
🕵️ monitoring — Surveillance Capabilities
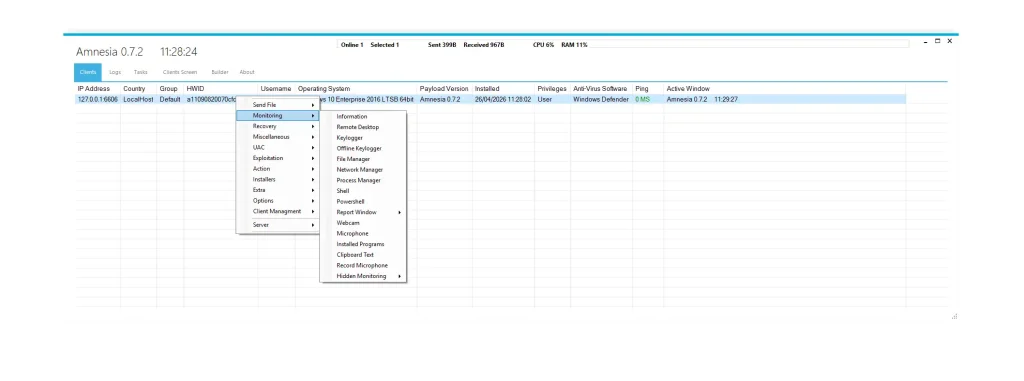
👁️ Full Spyware Functionality
- ⌨️ Keylogger System:
Records all keyboard inputs including passwords and messages. It is one of the most dangerous spyware features. - 📷 Webcam & Microphone Access:
Enables silent audio and video recording. This creates severe privacy risks for victims. - 📂 File System Control:
Allows full browsing, editing, and deletion of files. This gives attackers complete data control. - 🕶️ Stealth Monitoring Mode:
Operates without visible indicators. Users remain unaware of surveillance activity.
⚙️ options — System Manipulation
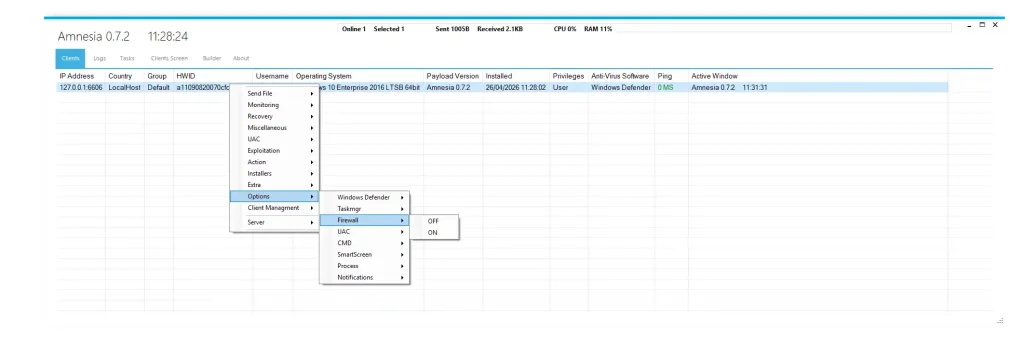
🛑 Security Disabling Mechanism
- 🛡️ Windows Defender Disabling:
Removes built-in antivirus protection. This allows unrestricted malware execution. - 🔥 Firewall Deactivation:
Disables network filtering protections. This opens communication channels for attackers. - ⚙️ UAC Bypass:
Removes system permission prompts. This enables silent privilege escalation. - 🚫 System Protection Removal:
Disables SmartScreen and security alerts. This weakens overall system defense.
🔄 recovery — Remediation Blocking
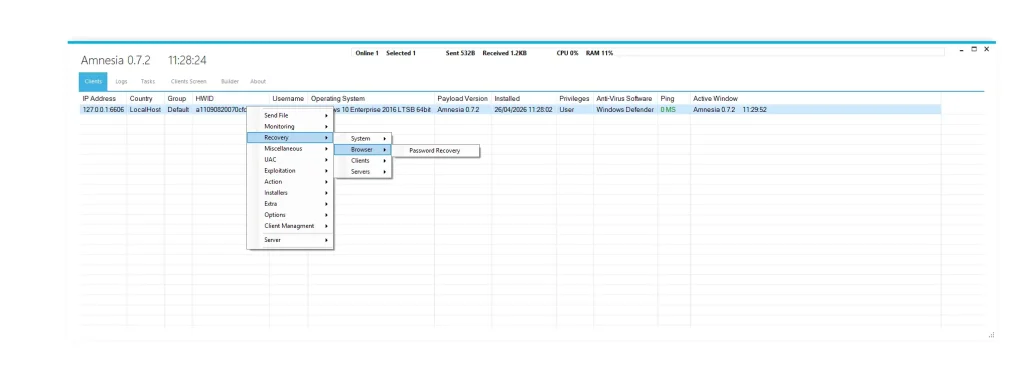
🚫 System Recovery Prevention
- 🧯 Safe Mode Blocking:
Prevents users from accessing recovery environments. This limits malware removal options. - ♻️ Restore Point Deletion:
Removes system rollback capabilities. This ensures persistent infection. - 💾 Recovery Partition Blocking:
Disables built-in OS recovery tools. This forces full system reinstall.
📤 sendfile — File Transfer System
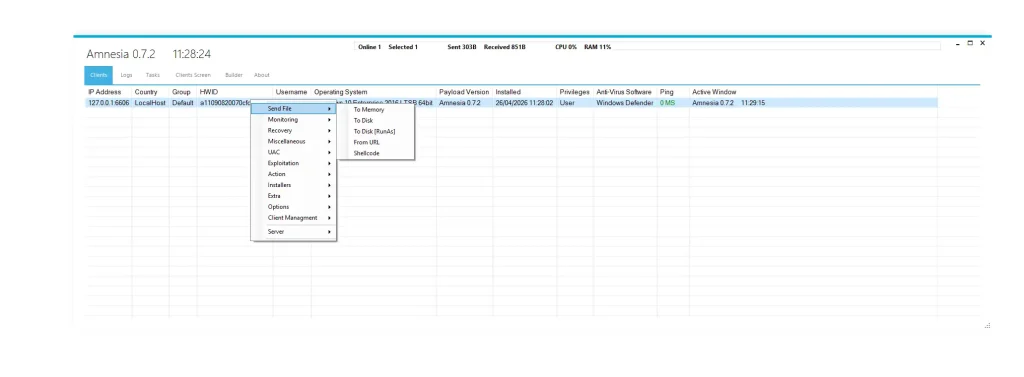
📁 Data Movement Engine
- ⬆️ Remote Upload Feature:
Allows attackers to install additional malware or tools. It supports multi-stage cyberattacks. - ⬇️ Remote Download Feature:
Enables extraction of sensitive files. This includes confidential documents and credentials. - 🕶️ Stealth Transfer Mode:
File transfers occur without user detection. This ensures silent data exfiltration.
🔐 uac — Privilege Escalation System
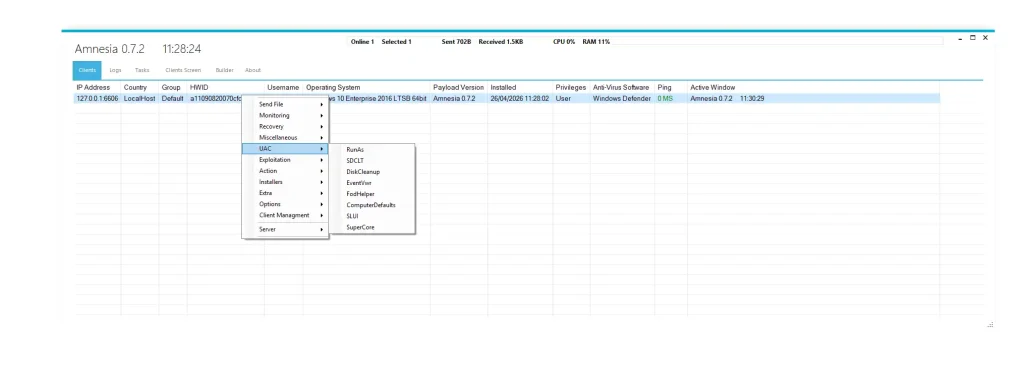
🧠 Admin Rights Bypass Techniques
- 🛠️ RunAs Exploitation:
Executes programs with elevated permissions. It bypasses normal user restrictions. - 🧩 FodHelper Abuse:
Exploits Windows feature-on-demand system. It allows silent admin access. - 📊 Event Viewer Exploitation:
Misuses system tools for privilege escalation. It bypasses security restrictions. - 🔑 SLUI & System Abuse:
Exploits activation processes for elevation. It is used in stealth escalation chains.
🛡️ Defense Recommendations
- 🧠 Endpoint Detection & Response (EDR):
Identifies abnormal behaviors like keylogging and injection attacks in real time. - 🌐 Network Monitoring:
Detects suspicious outbound connections to unknown servers. - 🔐 Privilege Control Policies:
Restricts admin access to essential users only. - 💾 Offline Backup Strategy:
Protects data from ransomware encryption attacks. - 🔌 USB Security Policies:
Prevents malware spread through removable devices.
Download Amnesia 0.7.2
Virus Total Report of Amnesia 0.7.2
https://www.virustotal.com/gui/file/7debef41d7ac938327b182593ec6a9e68003042962e571cb51dd66b52f645aba🧾 Conclusion
Amnesia 0.7.2 represents a highly advanced Remote Access Trojan built with modular architecture, stealth techniques, and full system control capabilities. It combines surveillance, exploitation, persistence, and ransomware-like behavior into a single cyber weapon framework.
From a cybersecurity perspective, understanding such malware is essential for improving detection systems, strengthening endpoint protection, and building resilient digital infrastructures against evolving cyber threats.
❓ FAQs about Amnesia 0.7.2
What is Amnesia 0.7.2 RAT used for?
Amnesia 0.7.2 is used for remote control of infected Windows systems, including spying, file theft, and system manipulation.
Is Amnesia 0.7.2 dangerous for users?
Yes, Amnesia 0.7.2 can steal data, record activity, and give attackers full control over a system.
Can antivirus detect Amnesia 0.7.2?
Some security tools can detect it, but advanced versions use evasion techniques to avoid detection.
How does Amnesia 0.7.2 infect systems?
It spreads through malicious downloads, phishing attacks, and infected USB devices.
Can Amnesia 0.7.2 steal passwords?
Yes, Amnesia 0.7.2 uses keylogging and file extraction to capture sensitive credentials.
Which systems are targeted?
Amnesia 0.7.2 primarily targets Windows operating systems in both personal and enterprise environments.
How can users protect against Amnesia 0.7.2 attacks?
By using updated antivirus tools, enabling firewall protection, and avoiding unknown downloads.
Is using Amnesia 0.7.2 RAT software legal?
No, unauthorized use of Amnesia 0.7.2 is illegal in most countries and can lead to serious penalties.