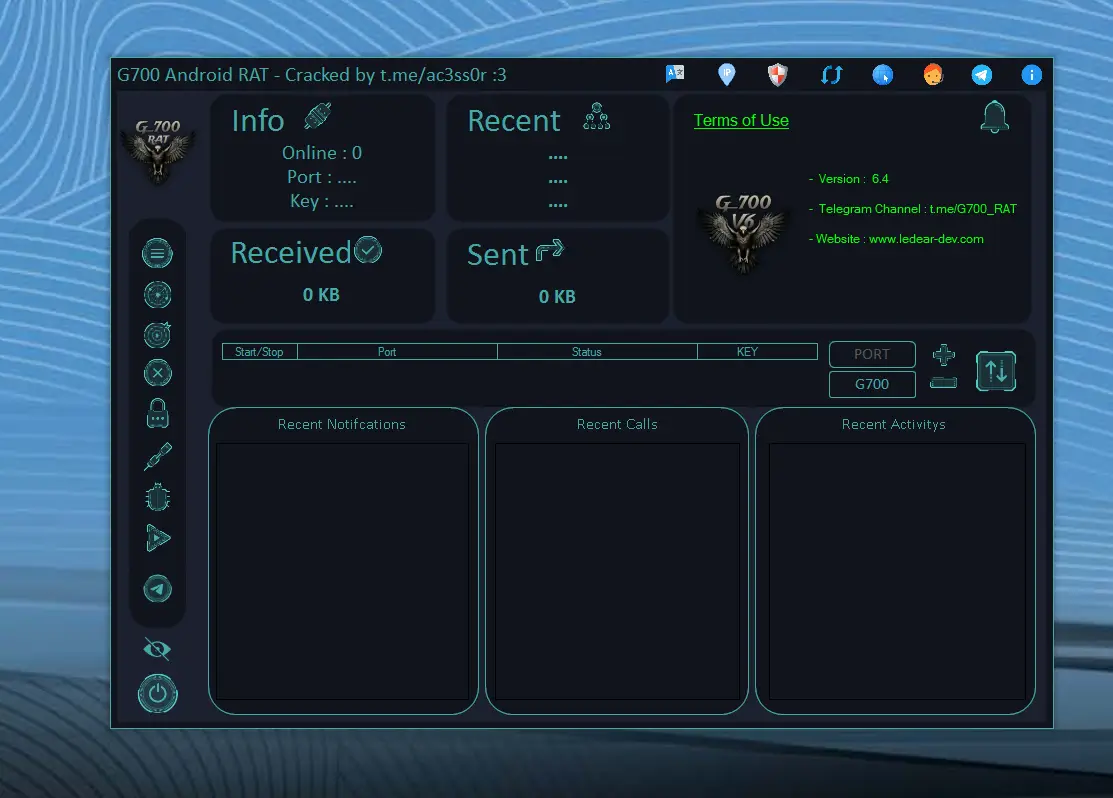
In the modern digital ecosystem across the United States and Europe, smartphones are no longer just communication tools—they are personal data hubs containing financial details, private conversations, and sensitive business information. As mobile usage increases, so do cybersecurity threats targeting these devices. One such advanced and dangerous threat is G700 RAT 6.4.
G700 RAT 6.4 is a sophisticated Remote Access Trojan (RAT) that silently infiltrates Android devices and gives cybercriminals complete remote control. Unlike traditional malware, it operates stealthily, making detection extremely difficult for average users.
This in-depth guide will help you understand everything about G700 RAT 6.4, including its features, risks, distribution methods, removal techniques, and prevention strategies—all optimized for modern search engine standards.
🔍 What Is a Remote Access Trojan (RAT)?
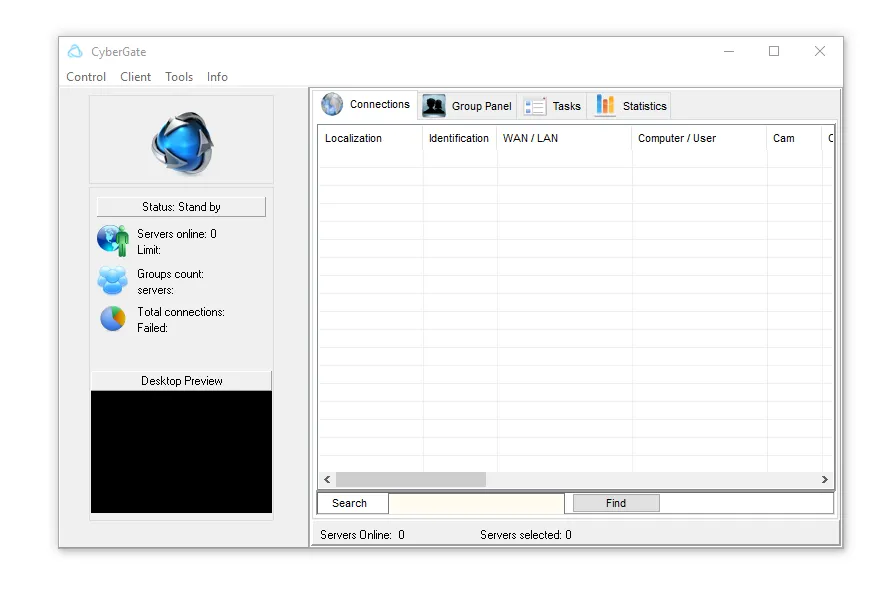
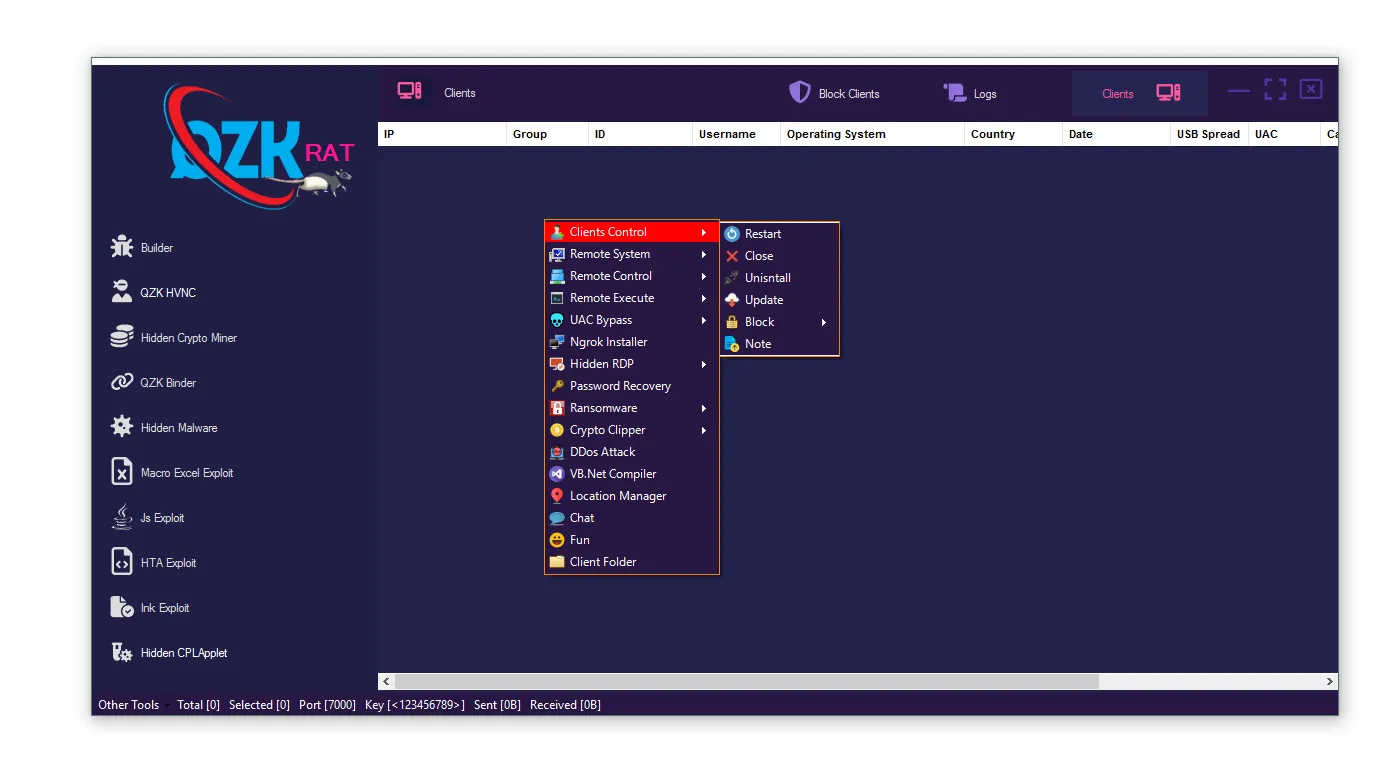
A Remote Access Trojan (RAT) is a type of malicious software that allows hackers to remotely control a device without user consent. Once installed, it creates a hidden backdoor that attackers can use to monitor and manipulate the device in real time.
RAT malware is commonly used in cybercrime activities such as surveillance, identity theft, and financial fraud. It is especially dangerous because it often disguises itself as legitimate software.
⚠️ What Is G700 RAT 6.4?
G700 RAT 6.4 is an advanced Android-targeting malware that belongs to the G700 RAT family. It is specifically designed to bypass security systems and provide attackers with unrestricted access to infected devices.
This version includes enhanced spying capabilities, stronger persistence mechanisms, and improved evasion techniques, making it more dangerous than earlier variants.
🚨 Key Features of G700 RAT 6.4
🎯 Full Remote Device Control
- 🔹 Complete System Access: G700 RAT 6.4 allows attackers to fully control the infected smartphone, including accessing apps, modifying system settings, and executing commands remotely. This means the hacker can operate the device as if they physically own it, making it extremely dangerous for both personal and professional use.
- 🔹 Real-Time Command Execution: Once connected, cybercriminals can send commands instantly, enabling them to perform actions such as opening applications, deleting files, or installing additional malware without the user’s knowledge.
- 🔹 Hidden Administrative Privileges: The malware often gains elevated permissions, which allows it to bypass user restrictions and security settings. This makes it harder to remove and increases its control over the device.
- 🔹 Remote App Management: Attackers can install or uninstall apps remotely, giving them the ability to introduce more harmful software or remove security tools that might detect the threat.
- 🔹 Persistent Access Mechanism: Even after rebooting the device, the malware remains active, ensuring continuous access for the attacker. This persistence makes it one of the most dangerous features of G700 RAT 6.4.
- 🔹 Silent Operation: All these actions occur in the background without triggering noticeable alerts, making detection nearly impossible for non-technical users.
- 🔹 Device Manipulation: Hackers can control device behavior, including locking screens or triggering system actions, potentially disrupting normal usage and causing data loss.
📂 Data Theft and Information Harvesting
- 🔹 Sensitive Data Extraction: G700 RAT 6.4 is designed to collect a wide range of personal data, including contacts, call logs, SMS messages, emails, and stored files. This information can be used for identity theft or sold on the dark web.
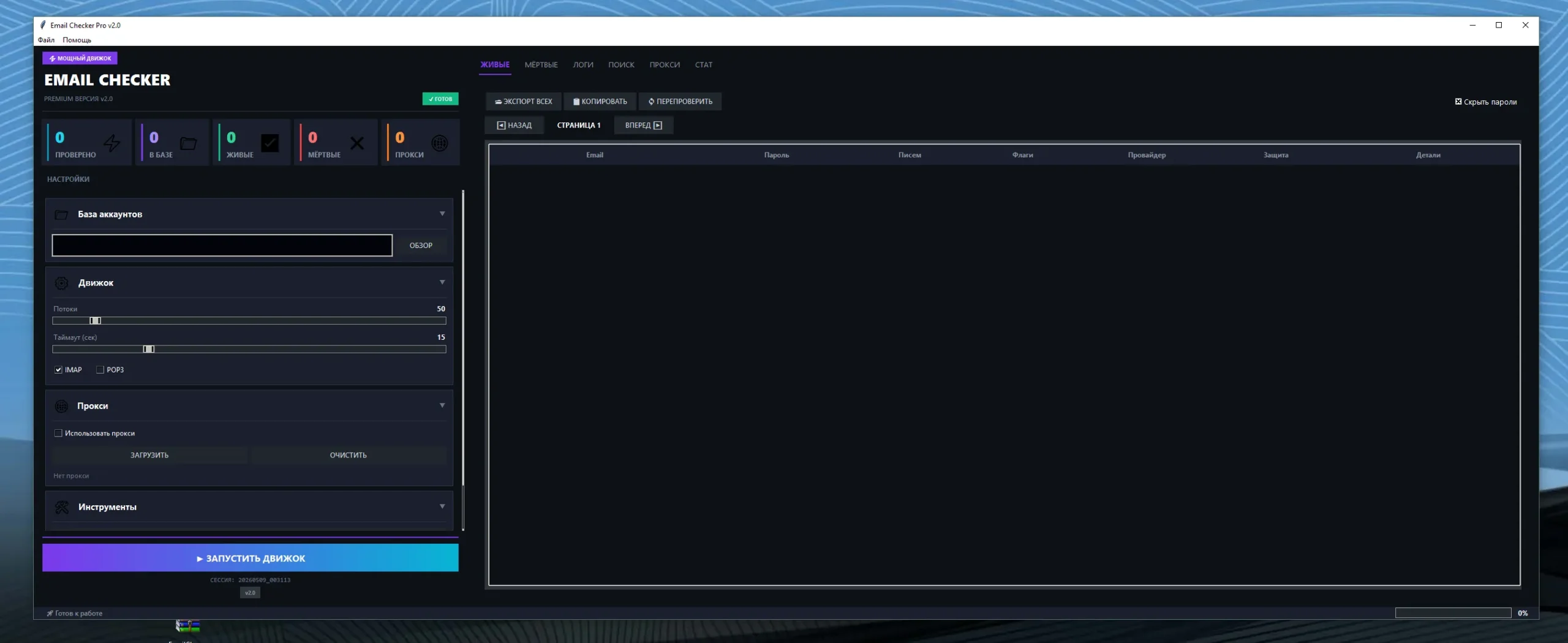
- 🔹 Credential Theft: The malware targets login credentials for banking apps, social media platforms, and email accounts, putting users at serious risk of account takeovers.
- 🔹 File Access and Downloading: Attackers can browse through files stored on the device and download sensitive documents, including photos, videos, and work-related files.
- 🔹 Clipboard Monitoring: It can monitor copied text, which is often used for passwords or financial data, making it a hidden but effective spying method.
- 🔹 Data Transmission to Servers: Collected information is sent to remote servers controlled by attackers, often without encryption, increasing exposure risks.
- 🔹 Continuous Data Collection: The malware operates continuously, gathering data over time to build a comprehensive profile of the victim.
- 🔹 Exploitation of Personal Information: Stolen data can be used for blackmail, phishing attacks, or financial fraud, making this feature extremely dangerous.
🎥 Camera and Microphone Surveillance
- 🔹 Unauthorized Camera Access: G700 RAT 6.4 can secretly activate the device’s camera to capture photos or record videos without user awareness.
- 🔹 Microphone Recording: The malware can record conversations and ambient sounds, effectively turning the device into a surveillance tool.
- 🔹 Real-Time Monitoring: Attackers can listen in live, enabling them to gather sensitive information such as business discussions or personal conversations.
- 🔹 Stealth Mode Operation: These actions occur silently without showing indicators like camera lights or notifications.
- 🔹 Privacy Violation Risks: This feature can lead to severe privacy breaches, especially if sensitive environments are recorded.
- 🔹 Data Storage and Sharing: Recorded media can be stored or shared by attackers, increasing the risk of misuse.
- 🔹 Long-Term Surveillance: Continuous monitoring over extended periods makes it highly invasive and dangerous.
⌨️ Keylogging and Credential Tracking
- 🔹 Keystroke Monitoring: G700 RAT records every key pressed on the device, capturing sensitive information like passwords and PINs.
- 🔹 Login Data Capture: This feature is particularly dangerous for banking apps and secure platforms, where login credentials can be stolen instantly.
- 🔹 Hidden Tracking Mechanism: Keylogging operates invisibly, making it difficult to detect without specialized tools.
- 🔹 Session Hijacking: Attackers can use captured credentials to access accounts in real time.
- 🔹 Multi-App Monitoring: The malware tracks input across multiple apps, increasing the amount of data collected.
- 🔹 Credential Reuse Exploitation: Since many users reuse passwords, this can lead to multiple account breaches.
- 🔹 High Financial Risk: This feature directly contributes to financial fraud and identity theft.
📍 Location Tracking and Monitoring
- 🔹 Real-Time GPS Tracking: The malware can track the exact location of the device at any given time.
- 🔹 Movement History Logging: It records travel patterns and frequently visited locations.
- 🔹 Geolocation Data Theft: This information can be used for targeted attacks or surveillance.
- 🔹 Privacy Concerns: Constant tracking poses serious risks to personal safety and privacy.
- 🔹 Integration with Other Features: Location data combined with stolen personal information increases the threat level.
- 🔹 Background Operation: Tracking occurs without visible indicators, making it hard to notice.
- 🔹 Potential Physical Risks: In extreme cases, attackers could misuse location data for harmful purposes.
💳 Financial Fraud and Banking Attacks
- 🔹 Banking App Exploitation: G700 RAT can overlay fake login screens on banking apps to steal credentials.
- 🔹 SMS Interception: It captures one-time passwords (OTPs), enabling unauthorized transactions.
- 🔹 Cryptocurrency Theft: Attackers can redirect wallet addresses during transactions.
- 🔹 Transaction Manipulation: The malware can alter payment details without user knowledge.
- 🔹 Direct Financial Loss: Victims may experience unauthorized withdrawals or purchases.
- 🔹 Fraud Automation: Some versions automate fraud processes, increasing efficiency for attackers.
- 🔹 Severe Economic Impact: This feature makes G700 RAT a major threat to financial security.
🌐 How G700 RAT 6.4 Spreads
📥 Common Infection Methods
- 📌 Fake Apps: Malware disguised as legitimate applications tricks users into installation.
- 📌 Cracked APK Files: Pirated apps often contain hidden malicious code.
- 📌 Phishing Links: Emails or messages redirect users to malicious downloads.
- 📌 Fake Updates: Users install malware thinking it is a system update.
- 📌 Malicious Ads: Clicking suspicious ads leads to automatic downloads.
⚠️ Signs Your Device May Be Infected
- 🚩 Fast battery drain
- 🚩 Slow performance
- 🚩 Unknown apps installed
- 🚩 High data usage
- 🚩 Random pop-ups
🛠️ How to Remove G700 RAT 6.4
- ✅ Install trusted antivirus software
- ✅ Remove suspicious applications
- ✅ Boot into safe mode
- ✅ Perform factory reset if needed
- ✅ Update your operating system
🔐 How to Protect Your Device
- ✔️ Download apps only from official stores
- ✔️ Avoid pirated software
- ✔️ Check app permissions carefully
- ✔️ Use mobile security tools
- ✔️ Keep your device updated
Download G700 RAT 6.4
Virus Total Report of G700 RAT 6.4
https://www.virustotal.com/gui/file/6289456a644a5392de77382b9658596ffe4a76a5687635ff08edd6ce95d07eaa🧠 Conclusion
G700 RAT 6.4 is a highly advanced and dangerous Android malware that poses serious risks to privacy, security, and financial stability. Its stealth capabilities and powerful features make it one of the most concerning threats in today’s mobile cybersecurity landscape.
Staying informed and practicing safe digital habits is essential to protect your data and devices from such threats.
❓ FAQs
What is G700 RAT 6.4 used for?
G700 RAT 6.4 is used by cybercriminals to remotely control devices, steal data, and conduct surveillance or financial fraud.
Is G700 RAT 6.4 dangerous?
Yes, it is extremely dangerous because it provides full device access and can steal sensitive information.
How does G700 RAT infect devices?
It spreads through fake apps, phishing links, cracked software, and malicious downloads.
Can G700 RAT be removed?
Yes, it can be removed using antivirus tools or by performing a factory reset.
How can I protect my phone from RAT malware?
Avoid downloading apps from unknown sources, keep your device updated, and use reliable security software.